The monetarily inspired FIN7 cybercrime gang has masqueraded as but a further fictitious cybersecurity organization called “Bastion Secure” to recruit unwitting program engineers beneath the guise of penetration screening in a likely lead-up to a ransomware scheme.
“With FIN7’s most current phony company, the criminal team leveraged legitimate, publicly obtainable information and facts from numerous reputable cybersecurity companies to make a slim veil of legitimacy all around Bastion Protected,” Recorded Future’s Gemini Advisory device stated in a report. “FIN7 is adopting disinformation strategies so that if a potential use or fascinated party had been to reality examine Bastion Protected, then a cursory search on Google would return ‘true’ information and facts for companies with a very similar identify or market to FIN7’s Bastion Secure.”


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
FIN7, also identified as Carbanak, Carbon Spider, and Anunak, has a observe document of striking cafe, gambling, and hospitality industries in the U.S. to infect position-of-sale (POS) devices with malware intended to harvest credit score and debit card quantities that are then utilised or offered for profit on underground marketplaces. The most up-to-date growth shows the group’s expansion into the remarkably lucrative ransomware landscape.
Environment up pretend entrance businesses is nothing new for FIN7, which has been earlier linked to yet another sham cybersecurity firm dubbed Combi Security that claimed to offer you penetration tests providers to buyers. Seen in that light, Bastion Safe is no distinctive.
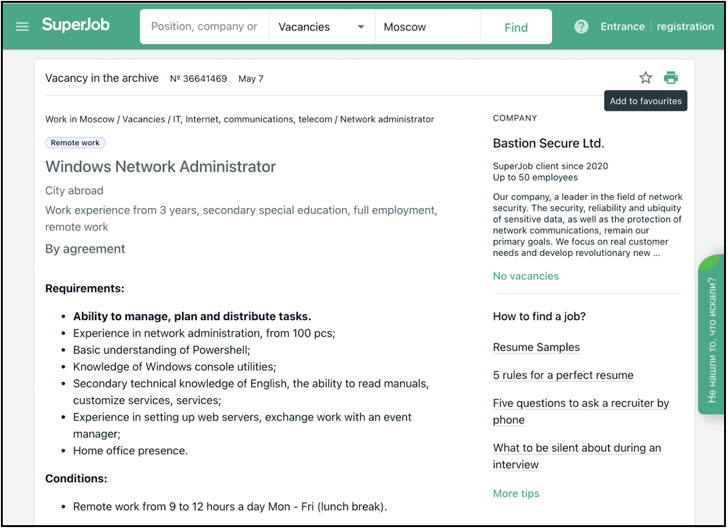
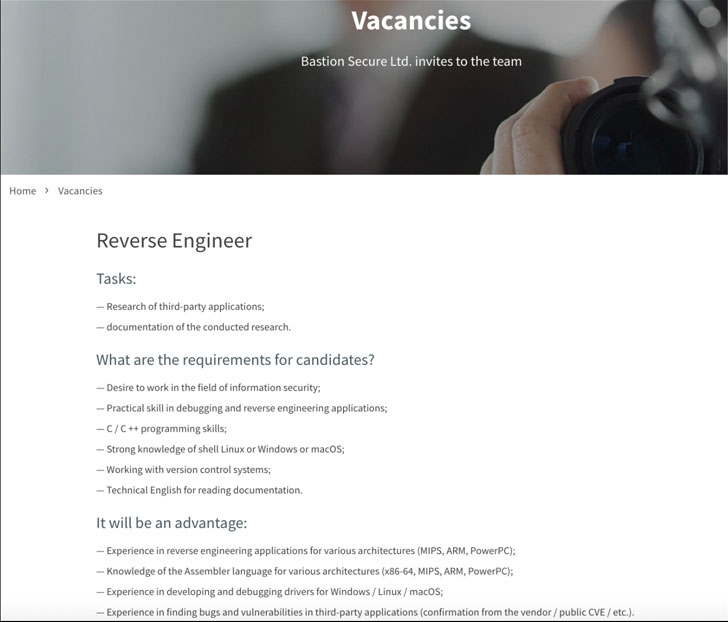
Not only does the new web-site function stolen content material compiled from other legitimate cybersecurity firms — largely Convergent Network Options — the operators advertised seemingly legitimate using the services of prospects for C++, PHP, and Python programmers, system directors and reverse-engineers on job boards, presenting them many equipment for apply assignments during the interview course of action.
These tools were being analyzed and located to be elements of the write-up-exploitation toolkits Carbanak and Lizar/Tirion, each of which have been previously attributed to the team and can be leveraged to compromise POS methods and deploy ransomware.
It can be, even so, in the upcoming phase of the using the services of course of action that Bastion Secure’s involvement in felony exercise turned obvious, what with the company’s associates offering obtain to a so-called consumer firm’s network and asking possible candidates to acquire facts on area directors, file methods, and backups, signalling a robust inclination towards conducting ransomware attacks.
“Bastion Secure’s occupation delivers for IT professional positions ranged amongst $800 and $1,200 USD a month, which is a feasible starting wage for this variety of place in article-Soviet states,” the scientists mentioned. “Nevertheless, this ‘salary’ would be a smaller portion of a cybercriminal’s portion of the felony earnings from a effective ransomware extortion or huge-scale payment card-thieving operation.”
By spending “unwitting ’employees’ far a lot less than it would have to pay back knowledgeable criminal accomplices for its ransomware schemes, […] FIN7’s bogus business scheme enables the operators of FIN7 to attain the expertise that the group requirements to have out its prison things to do, while at the same time retaining a greater share of the earnings,” the scientists included.
Aside from posing as a company entity, an more stage taken by the actor to give it a ring of authenticity is the actuality that 1 of the firm’s office environment addresses is the identical as that of a now-defunct, U.K.-primarily based firm named Bastion Security (North) Minimal. Web browsers such as Apple Safari and Google Chrome have since blocked obtain to the misleading web-site.
“Whilst cybercriminals looking for unwitting accomplices on authentic job web sites is practically nothing new, the sheer scale and blatancy with which FIN7 operates go on to surpass the actions demonstrated by other cybercriminal groups,” the researchers said, introducing the group is “making an attempt to obfuscate its real identity as a prolific cybercriminal and ransomware group by making a fabricated web existence via a largely legit-showing up web page, experienced task postings, and enterprise information webpages on Russian-language enterprise enhancement sites.”
Discovered this posting exciting? Comply with THN on Fb, Twitter and LinkedIn to read extra special content we submit.
Some elements of this posting are sourced from:
thehackernews.com


 Researchers Discover Microsoft-Signed FiveSys Rootkit in the Wild
Researchers Discover Microsoft-Signed FiveSys Rootkit in the Wild