Popular Apple provider Quanta on Wednesday reported it endured a ransomware attack from the REvil ransomware team, which is now demanding the iPhone maker spend a ransom of $50 million to avert leaking delicate documents on the dark web.
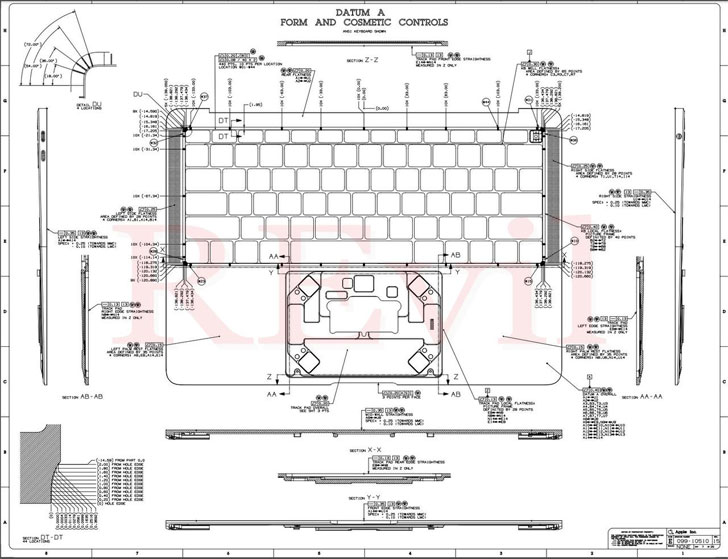
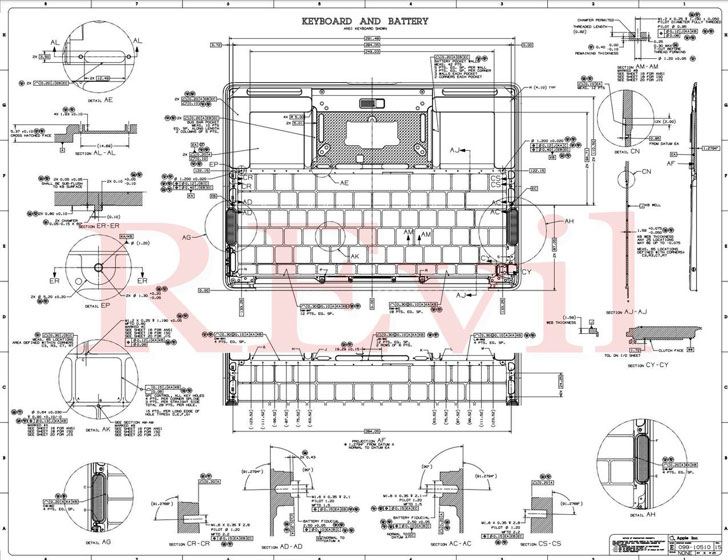
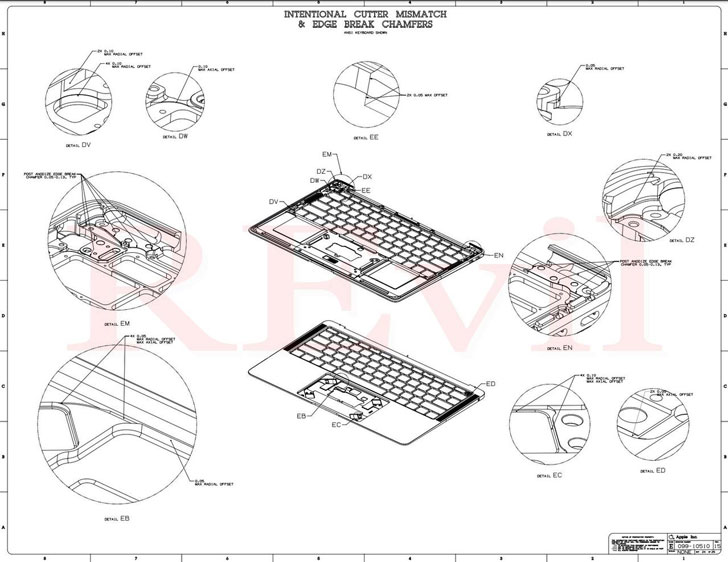
In a submit shared on its deep web “Happy Blog” portal, the threat actor claimed it arrived into possession of schematics of the U.S. company’s solutions these as MacBooks and Apple Look at by infiltrating the network of the Taiwanese manufacturer, professing it’s building a ransom need to Apple soon after Quanta expressed no interest in paying out to recover the stolen blueprints.
“Our team is negotiating the sale of significant quantities of private drawings and gigabytes of private details with numerous significant brand names,” the REvil operators claimed. “We advocate that Apple acquire back again the obtainable data by May perhaps 1.”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

Given that initial detected in June 2019, REvil (aka Sodinokibi or Sodin) has emerged as a person of the most prolific ransomware-as-a-services (RaaS) groups, with the gang remaining the initially to adopt the so-termed procedure of “double extortion” that has considering the fact that been emulated by other teams to increase their prospects of making a gain.
The method seeks to strain target organizations into paying up mostly by publishing a handful of documents stolen from their extortion targets prior to encrypting them and threatening to release more knowledge unless of course and until eventually the ransom desire is achieved.
The principal actor associated with promotion and advertising and marketing REvil on Russian-language cybercrime discussion boards is identified as Unidentified, aka UNKN. The ransomware is also operated as an affiliate company, whereby menace actors are recruited to spread the malware by breaching corporate network victims, although the core builders consider demand of sustaining the malware and payment infrastructure. Affiliates normally obtain 60% to 70% of the ransom payment.
Ransomware operators have netted extra than $350m in 2020, a 311% soar from the prior calendar year, according to blockchain examination corporation Chainalysis.

The latest progress also marks a new twist in the double extortion game, in which a ransomware cartel has long gone immediately after a victim’s buyer next an unsuccessful attempt to negotiate ransom with the key target.
We have achieved out to Quanta for comment, and we will update the tale if we hear back.
Nonetheless, in a assertion shared with Bloomberg, the company said it labored with external IT specialists in reaction to “cyber attacks on a modest variety of Quanta servers,” incorporating “there’s no content influence on the firm’s company operation.”
Found this short article appealing? Comply with THN on Facebook, Twitter and LinkedIn to go through far more exceptional content we article.
Some areas of this write-up are sourced from:
thehackernews.com


 Improve Your Cyber Security Posture by Combining State of the Art Security Tools
Improve Your Cyber Security Posture by Combining State of the Art Security Tools