Nowadays there are loads of cybersecurity applications on the sector. It is now much more vital than at any time that the applications you choose to use function nicely alongside one another. If they really don’t, you will not get the entire picture, and you will not be equipped to evaluate the complete process from a holistic standpoint.
This usually means that you won’t be ready to do the appropriate mitigations to improve your security posture. Listed here are examples of two equipment that work pretty properly collectively and how they will help you to get a holistic see of your cybersecurity posture.
Debricked – Use Open Supply Securely
How is Open up Resource a Security Risk?

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Open resource is not a security risk per se it truly is much more protected than proprietary application in many techniques! With the code remaining publicly readily available, it really is a great deal less complicated for the surrounding community to identify vulnerabilities, and fixes can be performed quickly.
What you do need to hold in head, although, is that any vulnerabilities in open supply are publicly disclosed and the public to everyone and everybody who appears to be. This means that if an attacker would like to find a vulnerability in your procedure constructed on open up source, they likely do not want to put in considerably hard work. It’s all out there, open up for everyone to see.
How does open-supply security perform?
The most prevalent aspect of open up-supply security is, like stated higher than, vulnerabilities. But according to Debricked, there are a few principal regions to continue to keep in mind: vulnerabilities, licenses, and wellbeing.
The major dilemma that influences all three places is the fact that the consumption of packages normally isn’t really preceded by a great deal of exploration. Developers typically never have time to worry about bringing new vulnerabilities or non-compliant licenses into the codebase.
Debricked’s tool solves this problem, allowing for developers to devote less time on security and much more time on undertaking what they’re there to do – create code. This is completed by identifying vulnerabilities and non-compliant offers, suggesting solutions, and eventually stopping new kinds from staying imported.
How can my open up-source security be enhanced when applying Debricked’s software?
As stated above it allows you to get additional command whilst permitting go at the similar time. You get a greater overview of vulnerabilities and licenses when owning to devote less time and electricity on manual security function.
Progressive characteristics
Debricked likes to target on two major matters:
1st and foremost, knowledge high quality. Debricked employs an array of sources, not just the classic ones, to make their vulnerability database. Their software is centered on device studying, which assists us discover new vulnerabilities more quickly as well as be additional correct than any human could be. As of ideal now, debricked scores a precision of in excess of 90% in most of the languages that debricked assistance, and debricked are continually on the lookout for new strategies to improve.
The latest addition to their offering, so now it truly is not even readily available in the instrument nonetheless, is what debricked call Open up Supply Overall health. OSH is a way of measuring the wellbeing of open up source projects quantitatively. It offers us knowledge on a series of facets, these kinds of as security (how speedily does the job disclose vulnerabilities?), local community well being (are the main maintainers nevertheless energetic?), and acceptance (how lots of commits have been created the previous yr, is the quantity lowering?) and substantially considerably a lot more. It minimizes the total of time desired for exploring a bundle right before importing it and helps make it simpler to make educated choices
securiCAD by foreseeti – Continuously Manage Your Security Risk Posture with Attack Simulations
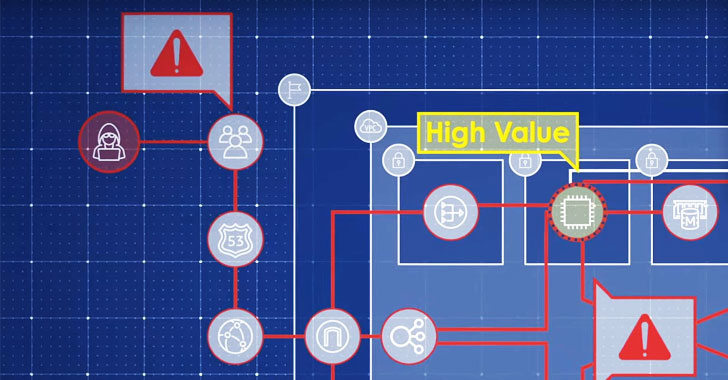
securiCAD by foreseeti is a leading tool for controlling your cybersecurity risk posture. It permits people to get a holistic, in-depth check out of the cybersecurity risk posture, triage and prioritize the dangers, and discover and prioritize the risk mitigation steps with the very best risk-mitigating effect. This is finished via state-of-the-artwork price awarded automatic risk modeling and attack simulations.
The simulations can be operate consistently in your cloud or on-prem setting – providing your security and DevOps groups with continual risk insights and proactive mitigation motion assistance. And as the simulations are conducted on digital twins/versions of your environments, you do not interfere with your are living ecosystem and can exam different what-if scenarios and mitigations at no risk in the product.
The science powering the product or service is based mostly on many years of analysis at the Royal Institute of Technology in Stockholm. securiCAD has simplified generating certain that you have command in excess of your setting. This is performed by preventing breaches by examining your configurations, enabling you to detect misconfigurations, possible lateral actions, and prioritize vulnerabilities.

The securiCAD Concept
Deliver Product:
The electronic twin product can be routinely made by importing data through the securiCAD API’s. In cloud environments, these types of as AWS and Azure, and many others., you simply just import the cloud-config details. If you have vulnerability scan information, you can import this into the product as perfectly. The digital twin model of your atmosphere is then immediately developed.
The logic is precisely the identical in on-prem environments. You can also generate a product manually – which is the situation in structure scenario risk modeling. Just after obtaining presented securiCAD with the design details, you determine high-price belongings and select the attacker profile.
Simulate attacks:
One of the most effective items about the simulation part is that it is accomplished on a digital twin design of your ecosystem. So that no assessments will in any way have an impact on your dwell surroundings. After you have set the parameters, the resource routinely simulates thousands of AI attacks to the electronic twin design. The attacker will try all probable attacks and attempt to get to and compromise all areas of the infrastructure.
Take care of Risk Exposure – Find, prioritize and mitigate:
Each and every simulation outcomes in a report with in-depth data, which include:
- Visualization of your ecosystem
- Risk Publicity for all the higher-worth property merged.
- Critical Paths for attackers to get to your superior-price assets.
- Chokepoints in your architecture that are an asset the place attacks (toward attack techniques with a consequence on them) converge in the design.
- Danger Summary with rated threats and descriptions.
- Recommended Mitigations to lessen your risk publicity.
Combining the Instruments
Facts from Debricked
Given that the most typical facet of open up-resource security is vulnerabilities, it is significant you get the ideal facts and can foundation your decisions on what risks you should really mitigate. That is why if you have any open supply-based mostly code in your project, you ought to contain Debricked’s vulnerability database when examining your natural environment.
Predictive Attack Simulations from securiCAD by foreseeti
securiCAD supports information from third events such as Debricked. This allows you to obtain all the info in a person place, and considering that all the prioritization is finished quickly, this is an productive use of your means. Environments can be difficult to visualize, securiCAD will make this simple given that all concepts, services, and configurations are represented in the electronic twin, and if you mix this with, for illustration, Debricked’s software, you can also visualize the dependencies.
The Holistic Watch
It isn’t really normally the vulnerability with the maximum severity that is the most hazardous one particular. It can frequently be the mix of various vulnerabilities that can be devastating. While Debricked supplies the vulnerability information, securiCAD will analyze the architecture from a proactive and holistic point of view.
With the complete image, you will find the weak spots in your environments – the critical paths for attackers to attain your superior-value assets – and get insights into what you need to have to do to mitigate hazards. Constantly, at scale, around time.
Discovered this short article interesting? Stick to THN on Fb, Twitter and LinkedIn to read through extra unique content material we post.
Some pieces of this short article are sourced from:
thehackernews.com

 Novel Email-Based Campaign Targets Bloomberg Clients with RATs
Novel Email-Based Campaign Targets Bloomberg Clients with RATs