A working day immediately after releasing Patch Tuesday updates, Microsoft acknowledged but an additional distant code execution vulnerability in the Windows Print Spooler ingredient, including that it truly is functioning to remediate the issue in an forthcoming security update.
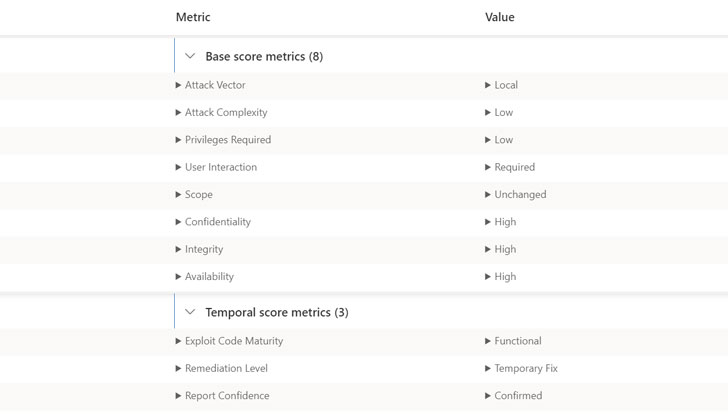
Tracked as CVE-2021-36958 (CVSS rating: 7.3), the unpatched flaw is the most up-to-date to be part of a listing of bugs collectively recognized as PrintNightmare that have plagued the printer support and appear to light-weight in latest months. Victor Mata of FusionX, Accenture Security, who has been credited with reporting the flaw, reported the issue was disclosed to Microsoft in December 2020.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“A remote code execution vulnerability exists when the Windows Print Spooler company improperly performs privileged file operations,” the business reported in its out-of-band bulletin, echoing the vulnerability information for CVE-2021-34481. “An attacker who successfully exploited this vulnerability could run arbitrary code with System privileges. An attacker could then set up plans watch, transform, or delete details or create new accounts with comprehensive person rights.”
It is worthy of noting that the Windows maker has given that unveiled updates to change the default Level and Print default behavior, efficiently barring non-administrator people from putting in or updating new and current printer drivers utilizing drivers from a remote computer or server with out very first elevating by themselves to an administrator.
As workarounds, Microsoft is recommending users to end and disable the Print Spooler provider to avert destructive actors from exploiting the vulnerability. The CERT Coordination Heart, in a vulnerability take note, is also advising users to block outbound SMB website traffic to reduce connecting to a malicious shared printer.
Located this report exciting? Comply with THN on Facebook, Twitter and LinkedIn to examine more exceptional content material we post.
Some elements of this post are sourced from:
thehackernews.com

 Accenture Confirms LockBit Ransomware Attack
Accenture Confirms LockBit Ransomware Attack