International IT consultancy big Accenture has turn out to be the most up-to-date organization to be hit by the LockBit ransomware gang, in accordance to a put up manufactured by the operators on their dark web portal, likely filling a void still left in the wake of DarkSide and REvil shutdown.
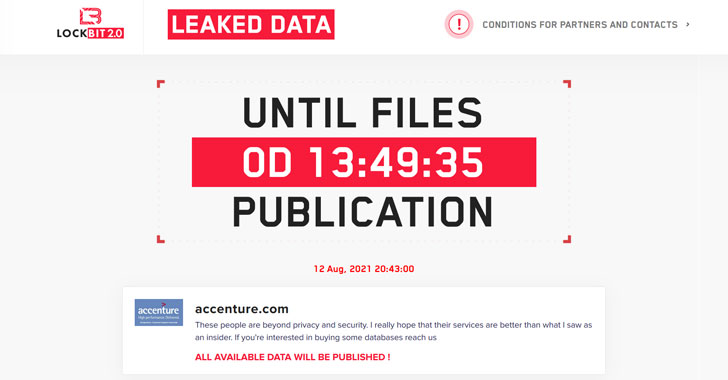
“These men and women are outside of privacy and security. I actually hope that their expert services are improved than what I noticed as an insider,” go through a message posted on the information leak site. Accenture said it has since restored the influenced devices from backups.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
LockBit, like its now-defunct DarkSide and REvil counterparts, operates utilizing a ransomware-as-a-assistance (RaaS) model, roping in other cybercriminals (aka affiliates) to carry out the intrusion working with its platform, with the payments frequently divided in between the criminal entity directing the attack and the main builders of the malware.
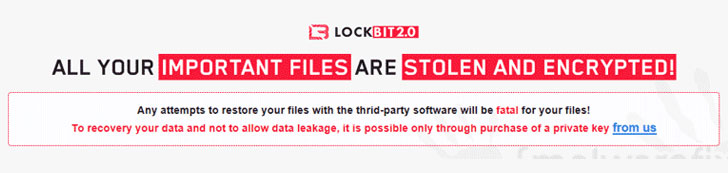
The ransomware team emerged on the menace landscape in September 2019, and in June 2021 introduced LockBit 2. together with an advertising campaign to recruit new partners. “LockBit also promises to provide the speediest knowledge exfiltration on the market place through StealBit, a facts theft tool that can allegedly obtain 100 GB of facts from compromised units in beneath 20 minutes,” Emsisoft pointed out in a profile of the criminal offense syndicate.
Some of LockBit’s previous victims include the Push Trust of India and Merseyrail.

The progress comes as ransomware incidents have come to be a critical danger to nationwide and financial security that have still left organizations scrambling to pay back hefty extortion calls for.
The spike in attacks from corporate and critical infrastructure have also been progressively accompanied by a tactic called “triple extortion,” whereby delicate info on a target’s devices is extracted prior to locking up as a result of encryption, followed by applying tension on victim providers into paying up by threatening to publish the stolen information on line, failing which, the attackers then undertake a third period, making use of that info to blackmail its consumers or launch DDoS attacks.
We have arrived at out to Accenture for additional remark, and we will update the story at the time we listen to again.
Uncovered this post interesting? Follow THN on Facebook, Twitter and LinkedIn to examine additional unique material we publish.
Some areas of this short article are sourced from:
thehackernews.com

 Microsoft Security Bulletin Warns of New Windows Print Spooler RCE Vulnerability
Microsoft Security Bulletin Warns of New Windows Print Spooler RCE Vulnerability