Organizations and security teams operate to protect by themselves from any vulnerability, and frequently will not recognize that risk is also brought on by configurations in their SaaS apps that have not been hardened. The newly released GIFShell attack process, which occurs via Microsoft Teams, is a fantastic example of how danger actors can exploit legitimate characteristics and configurations that have not been accurately established. This short article takes a glance at what the approach entails and the steps essential to overcome it.
The GifShell Attack Process
Found out by Bobby Rauch, the GIFShell attack system enables bad actors to exploit many Microsoft Teams options to act as a C&C for malware, and exfiltrate knowledge working with GIFs without having staying detected by EDR and other network monitoring instruments. This attack process needs a device or consumer that is by now compromised.
Discover how an SSPM can assess, observe and remediate SaaS misconfigurations and Gadget-to-SaaS user risk.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
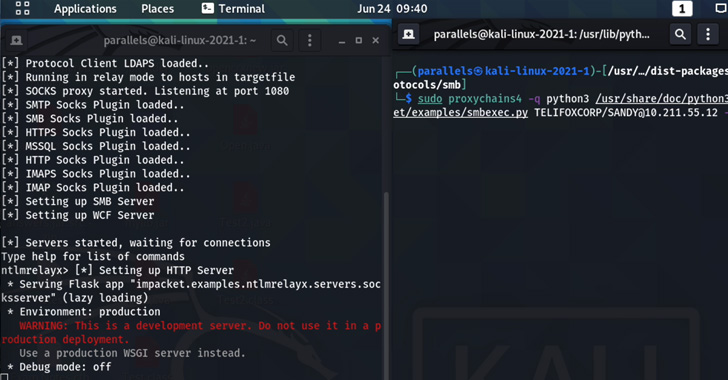
The principal ingredient of this attack lets an attacker to make a reverse shell that provides destructive commands through base64 encoded GIFs in Groups, and exfiltrates the output by way of GIFs retrieved by Microsoft’s very own infrastructure.
How does it get the job done?
- To develop this reverse shell, an attacker should initial compromise a personal computer to plant the malware — which usually means the negative actor requirements to convince the consumer to put in a malicious stager, like with phishing, that executes instructions and uploads command output by using a GIF url to a Microsoft Teams web hook.
- Once the stager is in area, the menace actor results in their very own Microsoft Groups tenant and contacts other Microsoft Teams buyers outside of the group.
- The menace actor can then use a GIFShell Python script to send a concept to a Microsoft Teams consumer that contains a specifically crafted GIF. This authentic GIF image has been modified to contain commands to execute on a target’s equipment.
- When the concentrate on receives the concept, the message and the GIF will be stored in Microsoft Team’s logs. Significant to notice: Microsoft Teams runs as a track record system, so the GIF does not even will need to be opened by the user to acquire the attacker’s commands to execute.
- The stager monitors the Teams logs and when it finds a GIF, it extracts and runs the commands.
- Microsoft’s servers will link back to the attacker’s server URL to retrieve the GIF, which is named using the base64 encoded output of the executed command.
- The GIFShell server operating on the attacker’s server will get this ask for and instantly decode the information letting the attackers to see the output of the command operate on the victim’s device.
Microsoft’s response
As documented by Lawrence Abrams in BleepingComputer, Microsoft agrees that this attack method is a issue, nevertheless, it “does not satisfy the bar for an urgent security correct.” They “could acquire action in a long term release to enable mitigate this technique.” Microsoft is acknowledging this research but asserting that no security boundaries have been bypassed.
While Rauch promises that without a doubt “two supplemental vulnerabilities identified in Microsoft Groups, a lack of permission enforcement and attachment spoofing”, Microsoft argues, “For this case… these all are submit exploitation and rely on a goal currently being compromised.” Microsoft is asserting that this method is employing reputable capabilities from the Teams platform and not a thing they can mitigate at the moment.
In accordance with Microsoft’s assertions, without a doubt this is the challenge quite a few companies face — there are configurations and capabilities that danger actors can exploit if not hardened. A few alterations to your tenant’s configurations can avert these inbound attacks from unidentified Teams tenants.
How to Defend Towards the GIFShell Attack
There are security configurations inside of Microsoft that, if hardened, can support to protect against this form of attack.
1 — Disable Exterior Obtain: Microsoft Groups, by default, allows for all exterior senders to deliver messages to buyers within just that tenant. Several business admins most likely are not even mindful that their organization allows for External Teams collaboration. You can harden these configurations:
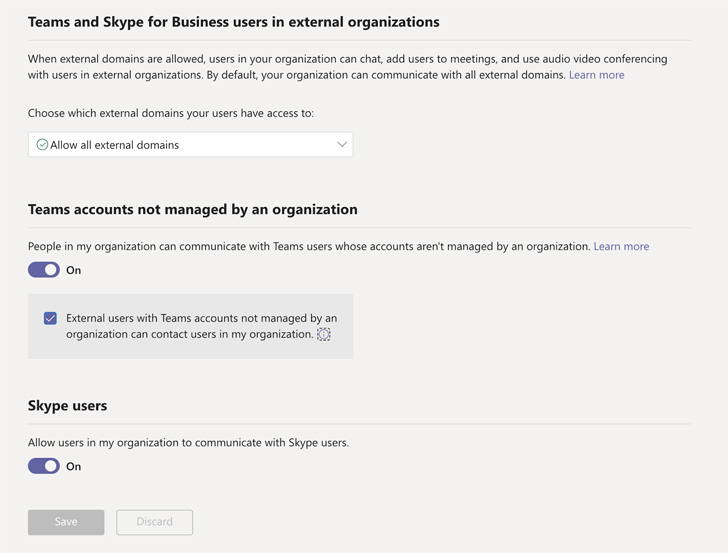 Figure 1: Microsoft Teams External Accessibility Configurations
Figure 1: Microsoft Teams External Accessibility Configurations
- Disable external area accessibility — Prevent persons in your group from acquiring, contacting, chatting, and environment up conferences with people today exterior to your firm in any area. Although not as seamless of a course of action as via Groups, this far better shields the group and is worthy of the further effort and hard work.
- Disable unmanaged external teams commence discussion — Block Groups people in your business from communicating with exterior Teams buyers whose accounts are not managed by an group.
2 — Acquire Device Stock Perception: You can assure your full organization’s units are entirely compliant and protected by applying your XDR / EDR / Vulnerability Management resolution, like Crowdstrike or Tenable. Endpoint security instruments are your 1st line of protection in opposition to suspicious activity these types of as accessing the device’s nearby teams log folder which is utilised for details exfiltration in GIFShell.
You can even go a action more and integrate an SSPM (SaaS Security Posture Administration) remedy, like Adaptive Protect, with your endpoint security resources to obtain visibility and context to effortlessly see and regulate the challenges that stem from these styles of configurations, your SaaS customers, and their linked gadgets.
How to Automate Protection In opposition to These Attacks
There are two techniques to battle misconfigurations and harden security configurations: handbook detection and remediation or an automatic SaaS Security Posture Management (SSPM) remedy. With the multitudes of configurations, end users, gadgets, and new threats, the guide strategy is an unsustainable drain on resources, leaving security teams overwhelmed. Even so, an SSPM resolution, this kind of as Adaptive Shield, allows security groups to gain complete manage over their SaaS apps and configurations. The correct SSPM automates and streamlines the approach of checking, detection and remediation for SaaS misconfigurations, SaaS-to-SaaS obtain, SaaS connected IAM, and Unit-to-SaaS person risk in compliance with equally sector and firm benchmarks.
In scenarios these types of as the GifShell attack strategy, Adaptive Shield’s misconfiguration management functions enables security groups to repeatedly assess, keep an eye on, establish and inform for when there is a misconfiguration (see determine 1). Then they can quickly remediate by way of the method or use a ticketing procedure of choice to deliver the pertinent information for fast remediation.
 Determine 2. Landscape See of SaaS App Hygiene
Determine 2. Landscape See of SaaS App Hygiene
Similarly, Adaptive Shield’s System Stock attribute (noticed in determine 2) can observe products getting employed organization-large and flag any Gadget-to-SaaS risk while correlating that info with the consumer roles and permissions and the SaaS applications in use. This permits security teams to gain a holistic watch of consumer-system posture to safeguard and protected significant-risk devices that can provide as a critical menace in their SaaS surroundings.
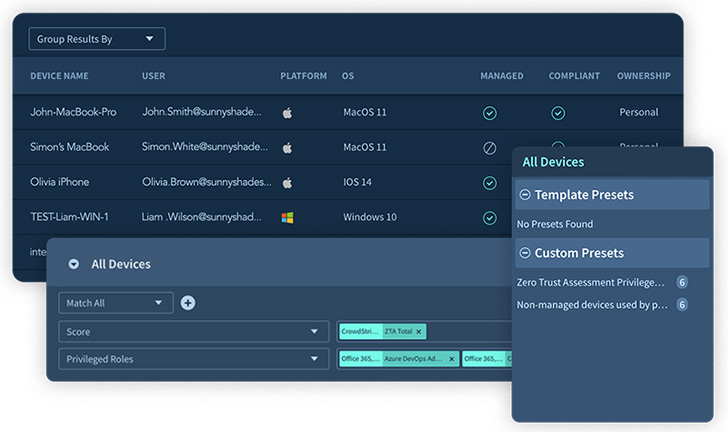 Figure 3. Gadget Inventory
Figure 3. Gadget Inventory
Study more about how the Adaptive Shield SSPM can safeguard your SaaS application ecosystem.
Found this short article appealing? Adhere to THN on Fb, Twitter and LinkedIn to read far more exclusive material we write-up.
Some areas of this report are sourced from:
thehackernews.com

 Europol and Bitdefender Release Free Decryptor for LockerGoga Ransomware
Europol and Bitdefender Release Free Decryptor for LockerGoga Ransomware