Microsoft is warning of an emerging risk concentrating on internet-linked cryptocurrency wallets, signaling a departure in the use of electronic coins in cyberattacks.
The tech big dubbed the new menace “cryware,” with the attacks ensuing in the irreversible theft of virtual currencies by means of fraudulent transfers to an adversary-managed wallet.
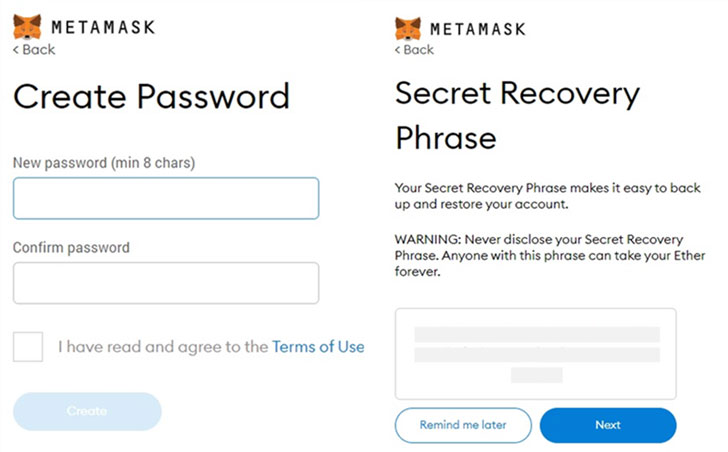
“Cryware are information stealers that collect and exfiltrate details straight from non-custodial cryptocurrency wallets, also identified as scorching wallets,” Berman Enconado and Laurie Kirk of the Microsoft 365 Defender Analysis Group reported in a new report.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
“Because incredibly hot wallets, as opposed to custodial wallets, are stored locally on a system and give less complicated obtain to cryptographic keys needed to execute transactions, additional and far more threats are focusing on them.”
Attacks of this form are not theoretical. Earlier this year, Kaspersky disclosed a economically-determined marketing campaign staged by the North Korea-based Lazarus Team, which involved targeting crypto companies with malware built to drain funds out of scorching wallets.
Cryware encompasses the following threats –
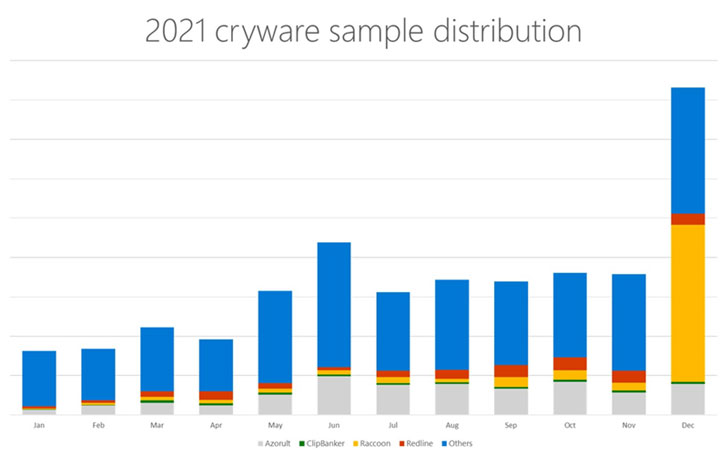
- Cryptojackers that surreptitiously take in a target’s system means to mine cryptocurrency
- Ransomware strategies that make use of cryptocurrency as a ransom payment to stay clear of detection
- Information and facts stealers (e.g., Mars Stealer, RedLine Stealer, Arkei, and Raccoon) that are becoming significantly upgraded to siphon hot wallet details together with other important facts saved in the technique, and
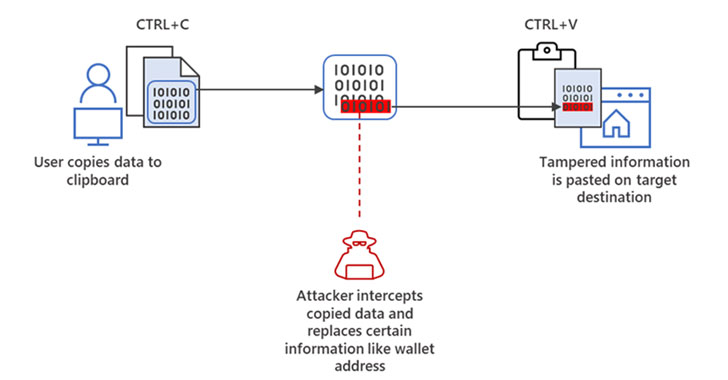
- ClipBankers (aka clippers) that steal cryptocurrency in the course of transactions by monitoring the clipboard and replacing the initial wallet tackle with the attacker’s handle

These information and facts-thieving attacks goal to extract hot wallet knowledge this sort of as private keys, seed phrases, and wallet addresses, thereby letting the menace actor to initiate rogue transactions and move funds to another wallet.
Alternatively, cybercriminals have also been observed to leverage strategies like memory dumping to screen the personal keys in plaintext, keylogging to seize keystrokes entered by a victim, or developing lookalike wallet internet websites to trick customers into entering their personal keys.
To mitigate these types of threats, Microsoft is recommending end users and businesses to lock very hot wallets when not trading, disconnect internet sites related to a wallet, stay away from storing non-public keys in plaintext, and validate the price of the wallet deal with when copying and pasting the info.
“Cryware signifies a shift in the use of cryptocurrencies in attacks: no extended as a suggests to an finish but the finish alone,” the researchers reported.
Discovered this posting fascinating? Observe THN on Fb, Twitter and LinkedIn to go through additional special articles we put up.
Some components of this post are sourced from:
thehackernews.com

 Russian Conti Ransomware Gang Threatens to Overthrow New Costa Rican Government
Russian Conti Ransomware Gang Threatens to Overthrow New Costa Rican Government