Microsoft is warning of a prevalent credential phishing marketing campaign that leverages open up redirector backlinks in email communications as a vector to trick users into browsing destructive internet sites while properly bypassing security software.
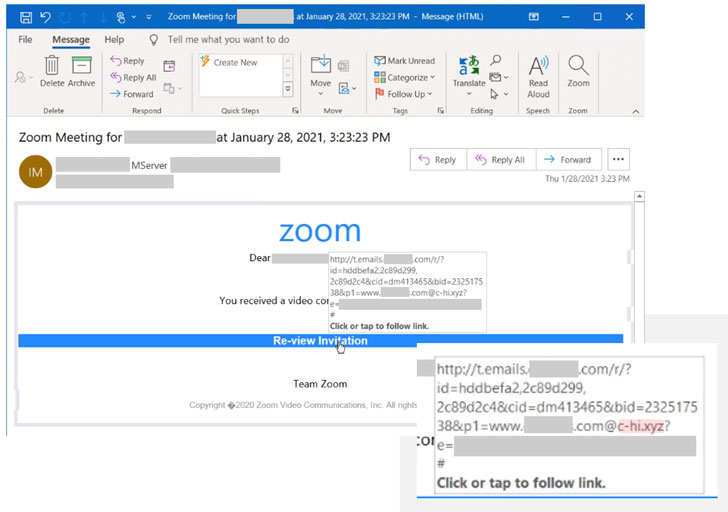
“Attackers merge these back links with social engineering baits that impersonate perfectly-identified productiveness instruments and products and services to entice users into clicking,” Microsoft 365 Defender Risk Intelligence Staff stated in a report released this week.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
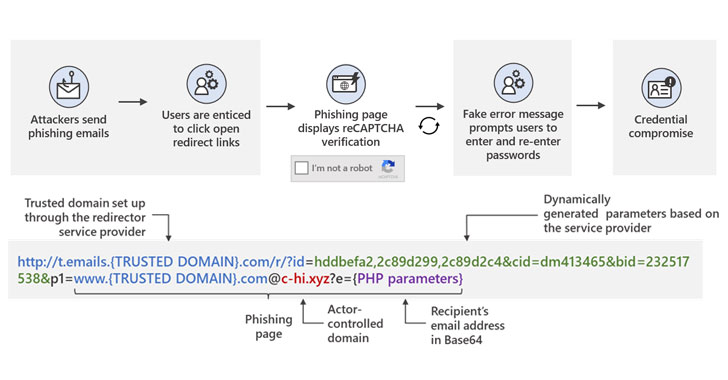
“Undertaking so leads to a collection of redirections — like a CAPTCHA verification site that adds a perception of legitimacy and makes an attempt to evade some automated analysis units — before using the user to a pretend signal-in web page. This finally potential customers to credential compromise, which opens the person and their organization to other attacks.”
Despite the fact that redirect hyperlinks in email messages provide a crucial device to just take recipients to third-party internet websites or track click premiums and measure the achievements of gross sales and marketing strategies, the very same method can be abused by adversaries to redirect these types of inbound links to their possess infrastructure, at the exact time preserving the trustworthy area in the comprehensive URL intact to evade examination by anti-malware engines, even when people endeavor to hover on one-way links to look at for any indicators of suspicious information.
The redirect URLs embedded in the message are set up making use of a reputable support in an endeavor to direct opportunity victims to phishing sites, while the remaining actor-controlled domains contained in the backlink leverage the top-stage domains .xyz, .club, .shop, and .on the internet (e.g. “c-tl[.]xyz”), which are passed as parameters and therefore sneaking past email gateway remedies.
Microsoft mentioned it noticed at the very least 350 one of a kind phishing domains as component of the marketing campaign — an attempt to obscure detection — underscoring the campaign’s powerful use of convincing social engineering lures that purport to be notification messages from applications like Workplace 365 and Zoom, effectively-crafted detection evasion method, and a tough infrastructure to carry out the attacks.

“This not only displays the scale with which this attack is becoming carried out, but it also demonstrates how substantially the attackers are investing in it, indicating likely considerable payoffs,” the researcher claimed.
To give the attack a veneer of authenticity, clicking the specifically-crafted back links redirects the buyers to a destructive landing web site that employs Google reCAPTCHA to block any dynamic scanning attempts. On completion of the CAPTCHA verification, the victims are displayed a fraudulent login web site mimicking a recognized support like Microsoft Workplace 365, only to swipe their passwords on distributing the details.
“This phishing marketing campaign exemplifies the great storm of [social engineering, detection evasion, and a large attack infrastructure] in its attempt to steal qualifications and finally infiltrate a network,” the researchers observed. “And given that 91% of all cyberattacks originate with email, corporations ought to thus have a security answer that will offer them multi-layered defense versus these kinds of attacks.”
Discovered this write-up attention-grabbing? Observe THN on Fb, Twitter and LinkedIn to browse more unique articles we publish.
Some areas of this short article are sourced from:
thehackernews.com

 Parallels Offers ‘Inconvenient’ Fix for High-Severity Bug
Parallels Offers ‘Inconvenient’ Fix for High-Severity Bug