North Korean defectors, journalists who go over North Korea-linked information, and entities in South Korea are being zeroed in on by a nation-point out-sponsored advanced persistent danger (APT) as element of a new wave of extremely-qualified surveillance attacks.
Russian cybersecurity business Kaspersky attributed the infiltrations to a North Korean hacker team tracked as ScarCruft, also identified as APT37, Reaper Team, InkySquid, and Ricochet Chollima.
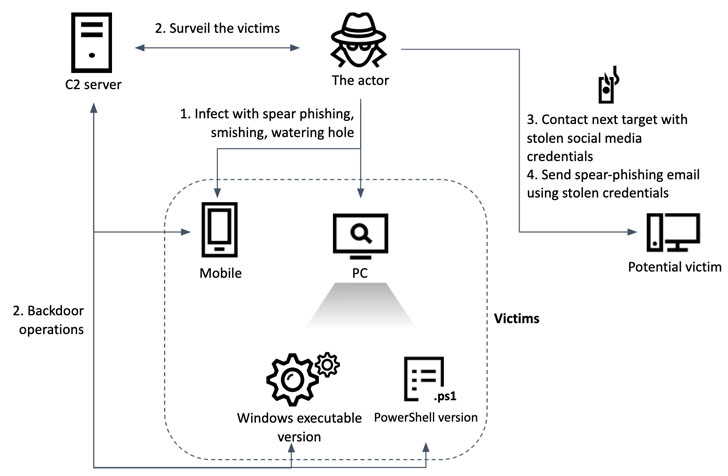
“The actor utilized a few sorts of malware with comparable functionalities: variations applied in PowerShell, Windows executables and Android programs,” the firm’s World wide Investigation and Investigation Crew (Terrific) stated in a new report published nowadays. “Although meant for various platforms, they share a comparable command and handle plan primarily based on HTTP interaction. As a result, the malware operators can control the complete malware household through one established of command and regulate scripts.”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

Likely energetic since at minimum 2012, ScarCruft is identified for concentrating on general public and non-public sectors positioned in South Korea with an intention to plunder delicate info saved in the compromised devices, and has been previously noticed working with a Windows-primarily based backdoor termed RokRAT.
The most important first an infection vector employed by APT37 is spear-phishing, in which the actor sends an email to a goal that is weaponized with a malicious doc. In August 2021, the threat actor was unmasked applying two exploits in the Internet Explorer web browser to infect victims with a custom made implant identified as BLUELIGHT by staging a watering gap attack from a South Korean on the web newspaper.
The circumstance investigated by Kaspersky is the two related and various in some strategies. The actor arrived at out to the victim’s associates and acquaintances making use of stolen Fb account credentials to create initial make contact with, only to comply with it up with a spear-phishing email enclosing a password-safeguarded RAR archive that features a Phrase doc. This decoy document claims to be about “North Korea’s most up-to-date condition and our nationwide security.”
Opening the Microsoft Place of work doc triggers the execution of a macro and the decryption of the future-stage payload embedded in just the document. The payload, a Visible Basic Software (VBA), contains a shellcode that, in flip, retrieves from a remote server the closing-phase payload with backdoor capabilities.
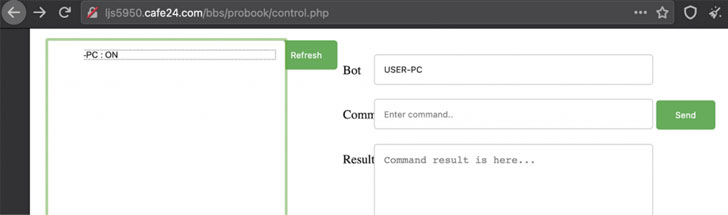
More tactics uncovered by Fantastic on one of the infected victims exhibit that post its breach on March 22, 2021, the operators managed to collect screenshots for a period of two months concerning August and September, just before deploying a completely-showcased malware known as Chinotto in late August to management the unit and exfiltrate delicate information and facts to a command-and-handle (C2) server.

What is actually much more, Chinotto will come with its possess Android variant to realize the similar target of spying on its users. The malicious APK file, shipped to the recipients through a smishing attack, prompts people to grant it a wide range of permissions through the set up section, enabling the application to amass contact lists, messages, contact logs, product information, audio recordings, and facts saved in apps such as Huawei Push, Tencent WeChat (aka Weixin), and KakaoTalk.
Kaspersky stated it labored with South Korea’s unexpected emergency response groups to consider down ScarCruft’s attack infrastructure, introducing it traced the roots of Chinotto in PoorWeb, a backdoor beforehand attributed to use by the APT group.
“Several journalists, defectors and human rights activists are targets of refined cyberattacks,” the researchers mentioned. “As opposed to firms, these targets ordinarily never have adequate applications to guard versus and react to really skilled surveillance attacks.”
Uncovered this posting attention-grabbing? Adhere to THN on Fb, Twitter and LinkedIn to read much more special content we submit.
Some pieces of this article are sourced from:
thehackernews.com


 Israel Blamed for Crippling Attack on Iranian Gas Stations
Israel Blamed for Crippling Attack on Iranian Gas Stations