A limited-lived phishing marketing campaign has been observed taking benefit of a novel exploit that bypassed a patch put in location by Microsoft to correct a distant code execution vulnerability impacting the MSHTML element with the objective of providing Formbook malware.
“The attachments represent an escalation of the attacker’s abuse of the CVE-2021-40444 bug and exhibit that even a patch are unable to constantly mitigate the steps of a enthusiastic and sufficiently expert attacker,” SophosLabs researchers Andrew Brandt and Stephen Ormandy reported in a new report posted Tuesday.
CVE-2021-40444 (CVSS score: 8.8) relates to a distant code execution flaw in MSHTML that could be exploited working with specifically crafted Microsoft Office files. Even though Microsoft tackled the security weak point as portion of its September 2021 Patch Tuesday updates, it has been place to use in a number of attacks at any time considering the fact that particulars pertaining to the flaw turned public.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

That exact same thirty day period, the technology big uncovered a specific phishing campaign that leveraged the vulnerability to deploy Cobalt Strike Beacons on compromised Windows techniques. Then in November, SafeBreach Labs reported details of an Iranian menace actor operation that qualified Farsi-speaking victims with a new PowerShell-primarily based details stealer created to collect sensitive data.
The new marketing campaign found out by Sophos aims to get all-around the patch’s defense by morphing a publicly readily available evidence-of-notion Business office exploit and weaponizing it to distribute Formbook malware. The cybersecurity agency explained the good results of the attack can, in element, be attributed to a “as well-narrowly targeted patch.”
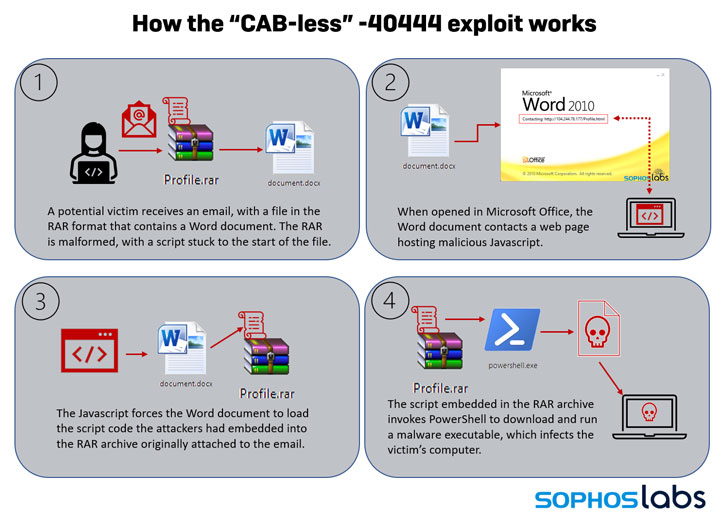
“In the original variations of CVE-2021-40444 exploits, [the] malicious Office document retrieved a malware payload packaged into a Microsoft Cabinet (or .Cab) file,” the researchers spelled out. “When Microsoft’s patch shut that loophole, attackers learned they could use a distinct attack chain altogether by enclosing the maldoc in a specially crafted RAR archive.”
Taxi-a lot less 40444, as the modified exploit is termed, lasted for 36 hours amongst October 24 and 25, all through which spam emails that contains a malformed RAR archive file were being sent to prospective victims. The RAR file, in convert, bundled a script created in Windows Script Host (WSH) and a Word Doc that, on opening, contacted a distant server hosting destructive JavaScript.
As a result, the JavaScript code used the Term Doc as a conduit to launch the WSH script and execute an embedded PowerShell command in the RAR file to retrieve the Formbook malware payload from an attacker-managed site.
As for why the exploit disappeared a minor about a day in use, clues lie in the truth that the modified RAR archive documents wouldn’t perform with older variations of the WinRAR utility. “So, unexpectedly, in this scenario, people of the considerably older, outdated variation of WinRAR would have been superior secured than customers of the most recent release,” the scientists reported.
“This exploration is a reminder that patching on your own simply cannot shield against all vulnerabilities in all circumstances,” SophosLabs Principal Researcher Andrew Brandt explained. “Environment limits that avert a user from unintentionally triggering a malicious doc assists, but folks can however be lured into clicking the ‘enable content’ button.”
“It is thus vitally vital to teach staff and remind them to be suspicious of emailed documents, particularly when they get there in abnormal or unfamiliar compressed file formats from persons or providers they don’t know,” Brandt added.
Found this post fascinating? Observe THN on Fb, Twitter and LinkedIn to go through more unique material we article.
Some parts of this report are sourced from:
thehackernews.com



 Active Directory Bugs Could Let hackers Take Over Windows Domain Controllers
Active Directory Bugs Could Let hackers Take Over Windows Domain Controllers