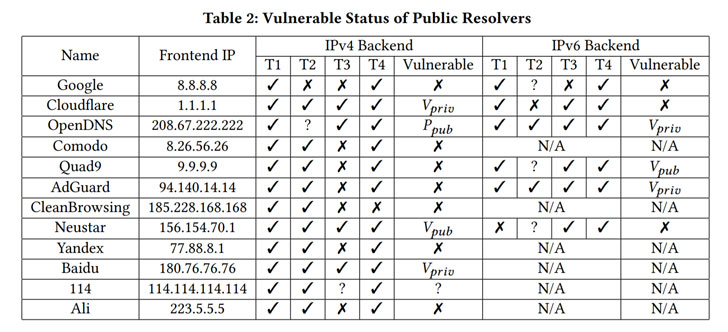
Scientists have shown but an additional variant of the Unfortunate DNS cache poisoning attack that leaves about 38% of the domain title resolvers susceptible, enabling attackers to redirect website traffic at first destined to respectable web sites to a server under their control.
“The attack permits an off-path attacker to inject a malicious DNS document into a DNS cache,” College of California scientists Keyu Male, Xin’an Zhou, and Zhiyun Qian reported. “Sad DNS attack enables an attacker to redirect any website traffic (at first destined to a particular domain) to his possess server and then grow to be a person-in-the-middle (MITM) attacker, allowing for eavesdropping and tampering of the conversation.”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The most current flaw affects Linux kernels as properly as preferred DNS application, together with BIND, Unbound, and dnsmasq jogging on major of Linux, but not when operate on other working systems FreeBSD or Windows.
From Kaminsky Attack to Unhappy DNS
DNS cache poisoning, also called DNS spoofing, is a system in which corrupt details is released into a DNS resolver’s cache, so that DNS queries return an incorrect response (i.e., IP address) for a trusted area (e.g., www.illustration.com) and consumers are directed to destructive internet sites. Originally learned by researcher Dan Kaminsky in 2008, the attack stemmed from the actuality that recursive resolvers normally utilised a single open port (ordinarily 53) to deliver and get messages to authoritative nameservers.

This not only designed guessing the source port trivial, an adversary can forge a reaction by flooding the resolver with DNS responses for some or all of the 65 thousand or so doable transaction IDs that are connected to the DNS lookup requests sent to the nameservers.
To reach this, all an attacker experienced to do was guess the 16-bit identifier — i.e., that means there can be only 65,536 transaction ID values — which is applied to confirm the authenticity of the nameserver and prove that the IP deal with returned is legitimate. Thus in the event the destructive reply with the correct transaction ID arrives in advance of the reaction from the authoritative server, then the DNS cache would be poisoned, returning the attacker’s selected deal with as an alternative of the genuine IP deal with.
But considering the fact that the recursive resolver caches information and facts gained from authoritative nameservers, this also signifies that if the resolver receives a request for an IP deal with of a domain name that was a short while ago requested by a different consumer, it just replies back again to the shopper the asked for record from its cache without the need of having to connect with the nameservers.
Since then, the attacks have been rendered unfeasible by rising the entropy making use of the transaction ID alongside with a randomized UDP port as a next identifier alternatively of employing the default port 53 for lookup queries. Having said that, newly discovered leaky facet channels have designed it feasible to derandomize the ephemeral port number, proficiently undoing the protections.
Unfortunate DNS aka Side channel AttackeD DNS, disclosed by the identical team of scientists in November 2020, depends on ICMP “port unreachable” concept as a indicates to infer which ephemeral port is utilized. Although ICMP is important for routing diagnostic and mistake responses in an IP network, the protocol’s charge-restricting function gives a system for restricting the quantity of bandwidth that may perhaps be utilized for inbound ICMP targeted traffic on a port with the goal of protecting against denial-of-provider (DoS) attacks that can come up when an attacker attempts overload the network with ICMP messages.

The novel aspect channel attack includes the attacker sending a variety of spoofed UDP probes made up of the victim’s forged supply address to the focus on that’s huge enough to cause the amount-limiting, employing the method to slim down the open ports and guess the transaction ID, like it is really in the case of the primary Kaminsky attack.
“Specifically, if a guessed port range (in a spoofed UDP probe) transpires to match the suitable ephemeral port, the resolver will not generate an ICMP message (otherwise it would),” the scientists stated. “This final results in possibly a stationary limit counter or a decrement of the counter. An attacker can then test irrespective of whether the counter has been drained by attempting to solicit ICMP responses with a UDP probe from his true/non-spoofed IP.”
A beforehand ignored attack area
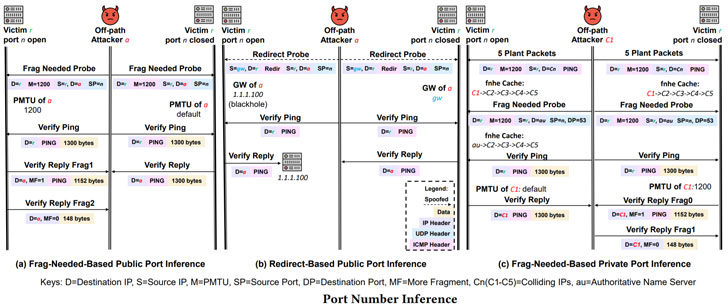
Whilst prior techniques, counting Unfortunate DNS, hire UDP probes to determine whether or not a UDP port is open or closed, the newly discovered DNS cache poisoning attack immediately explores a facet channel in the course of the method of dealing with ICMP error messages — i.e., ICMP frag wanted or ICMP redirect packets — that by structure do not elicit a reaction, utilizing it as a yardstick to attain the same objective.
“An attacker does not always have to count on the explicit suggestions from an ICMP probe,” the researchers noted. “As an alternative, even if the processing of ICMP probes is totally silent, as extended as there is some shared useful resource whose state is influenced, we may locate means (other probes) to notice the adjusted state of the shared useful resource.”
The central notion of the attack is to use the constrained variety of full slots in the world wide exception cache, a 2048-bucket hash table, to discern if an update has occurred following a batch of ICMP probes. The aspect channel is also diverse from Unhappy DNS in that it arises when processing incoming ICMP messages (as opposed to egress packets) and it “leverages the area useful resource limit (i.e., the area for storing the following hop exception cache is restricted) when Unhappy DNS’ aspect channel leverages the time source restrict (i.e., ICMP mistake making amount is confined).
The scientists suggest a variety of mitigations to protect against the hottest attack, these as randomizing the caching framework, rejecting ICMP redirect messages, and environment the socket alternative IP_PMTUDISC_OMIT, which instructs the fundamental working method not to acknowledge the ICMP frag wanted messages and therefore absolutely eradicates the side channel similar processing in the kernel.
“DNS is a single of the fundamental and historical protocols on the Internet that supports numerous network applications and expert services,” the researchers said. “However, DNS was developed with no security in mind and is subject to a wide variety of major attacks, a person of which is the well-identified DNS cache poisoning attack. In excess of the a long time of evolution, it has confirmed terribly demanding to retrofit potent security capabilities into it.”
Uncovered this short article intriguing? Adhere to THN on Fb, Twitter and LinkedIn to go through a lot more special content material we publish.
Some sections of this report are sourced from:
thehackernews.com


 North Korean Cyber-criminal Recycles Tactics and Targets
North Korean Cyber-criminal Recycles Tactics and Targets