The Estonian governing administration has discovered that the nation was on the receiving conclusion of the “most extensive” DDoS attacks in 15 many years this 7 days following angering Moscow. The …
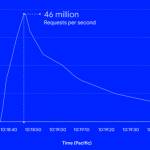
Google Cloud Blocks Record DDoS attack of 46 Million Requests Per Second
Google's cloud division on Thursday disclosed it mitigated a collection of HTTPS dispersed denial-of-company (DDoS) attacks which peaked at 46 million requests per next (RPS), generating it the …
Google Cloud Blocks Record DDoS attack of 46 Million Requests Per SecondRead More
UK Carrier Claims to Block One Million Vishing Calls Per Day
UK provider EE claims to have blocked 11 million scam phone calls given that rolling out new AI technology in July to detect possible vishing attacks. The agency mentioned it makes use of the unnamed …
UK Carrier Claims to Block One Million Vishing Calls Per DayRead More
IT Pro News In Review: Global south fights ransomware while Alphabet splurges on blockchain
IT Pro News In Critique: World wide south fights ransomware when Alphabet splurges on blockchain Some parts of this short article are sourced from: www.itpro.co.uk …
IT Pro News In Review: Global south fights ransomware while Alphabet splurges on blockchainRead More
Cyber Tops Staff Retention as Biggest Business Risk
Cybersecurity problems depict the most critical risk going through organizations, beating inflation, expertise acquisition/retention and soaring output expenses, according to a new PwC study. The PwC …
Cyber Tops Staff Retention as Biggest Business RiskRead More
New Amazon Ring Vulnerability Could Have Exposed All Your Camera Recordings
Retail large Amazon patched a large-severity security issue in its Ring application for Android in May perhaps that could have enabled a rogue software mounted on a user's gadget to obtain delicate …
New Amazon Ring Vulnerability Could Have Exposed All Your Camera RecordingsRead More
The IT Pro Podcast: Does threat attribution matter?
There is a vast universe of threats going through modern companies, from opportunistic lone hackers and organised prison gangs, to condition-backed intelligence models performing for nations this kind …
The IT Pro Podcast: Does threat attribution matter?Read More
Podcast transcript: Does threat attribution matter?
This automatically-generated transcript is taken from the IT Pro Podcast episode ‘Does threat attribution matter?’. We apologise for any errors.Adam Shepherd Hi, I'm Adam Shepherd.Connor Jones And …
Podcast transcript: Does threat attribution matter?Read More
Researchers Detail Evasive DarkTortilla Crypter Used to Deliver Malware
A .NET-dependent evasive crypter named DarkTortilla has been utilised by risk actors to distribute a broad array of commodity malware as properly as specific payloads like Cobalt Strike and …
Researchers Detail Evasive DarkTortilla Crypter Used to Deliver MalwareRead More
Hackers Deploy Bumblebee Loader to Breach Target Networks
Danger actors involved with BazarLoader, TrickBot and IcedID malware are now progressively deploying the loader regarded as Bumblebee to breach focus on networks and subsequently perform …
Hackers Deploy Bumblebee Loader to Breach Target NetworksRead More
ATMZOW JS Sniffer Campaign Linked to Hancitor Malware
The same menace actors could be guiding both of those the ATMZOW JS sniffer campaign and the Hancitor malware downloader. The link was manufactured early this week by risk intelligence analyst Victor …
ATMZOW JS Sniffer Campaign Linked to Hancitor MalwareRead More
Quarter of All Gambling Sites Hit by DDoS Attacks in June
A quarter of all gambling web-sites were being hit with dispersed denial-of-company (DDoS) attacks executed by botnets in June, in accordance to a new report by cybersecurity corporation Imperva. The …
Quarter of All Gambling Sites Hit by DDoS Attacks in JuneRead More
Google adds prevalence visualisation, curated threat detection to Chronicle suite
ShutterstockGoogle Cloud has introduced the typical availability of new curated menace detection capabilities within its Chronicle Cloud SecOps suite.Security groups will now be able to simply …
Google adds prevalence visualisation, curated threat detection to Chronicle suiteRead More
China-backed APT41 Hackers Targeted 13 Organisations Worldwide Last Year
The Chinese highly developed persistent menace (APT) actor tracked as Winnti (aka APT41) has targeted at the very least 13 organizations geographically spanning throughout the U.S, Taiwan, India, …
China-backed APT41 Hackers Targeted 13 Organisations Worldwide Last YearRead More
Estonia fends off major cyber attack following Soviet-era monuments ousting
Estonia, a region in northeastern Europe, properly withstood and survived "the most considerable cyber attacks considering that 2007" soon following it taken out Soviet monuments from a location …
Estonia fends off major cyber attack following Soviet-era monuments oustingRead More
US government set to outlaw leaky software in the military
ShutterstockThe US government has handed a Monthly bill that would forbid the Section of Defense (DoD) from procuring any software programs that contained a solitary security vulnerability.It marks …
US government set to outlaw leaky software in the militaryRead More
Threat Group Ramps-Up Attacks on Travel Sector in 2022
Researchers have revealed new aspects of a prolific APT team which has applied 15 malware people in excess of the earlier four many years to steal information from travel and hospitality …
Threat Group Ramps-Up Attacks on Travel Sector in 2022Read More
Apple patches ‘superpower’ zero-days affecting iPhones, iPads, and Macs
ShutterstockApple has set two zero-working day vulnerabilities impacting iOS, iPadOS, and macOS Monterrey that may well have been actively exploited.The first exploit is a distant code execution (RCE) …
Apple patches ‘superpower’ zero-days affecting iPhones, iPads, and MacsRead More
Apple patches ‘superpower’ zero-days affecting iPhones, iPads, and Macs
ShutterstockApple has fastened two zero-day vulnerabilities impacting iOS, iPadOS, and macOS Monterrey that may have been actively exploited.The 1st exploit is a remote code execution (RCE) flaw …
Apple patches ‘superpower’ zero-days affecting iPhones, iPads, and MacsRead More
Researchers Find 35 Adware Apps on Google Play
Security gurus have recurring warnings about destructive programs hiding on official cellular application stores soon after acquiring dozens of them on Google Perform. Bitdefender said it discovered …