Pentesting and vulnerability scanning are often perplexed for the exact same assistance. The problem is, business house owners generally use just one when they genuinely will need the other. Let’s dive in and demonstrate the variations.
Men and women commonly confuse penetration tests and vulnerability scanning, and it’s uncomplicated to see why. Both appear for weaknesses in your IT infrastructure by checking out your units in the exact way an actual hacker would. Nevertheless, there is a quite critical distinction between the two – and when just about every is the much better alternative.
Handbook or automated?
Penetration testing is a handbook security evaluation in which cyber security experienced makes an attempt to discover a way to split into your programs. It is a fingers-on, in-depth take a look at to examine security controls throughout a wide range of devices, like web application, network and cloud environments. This form of tests could acquire many weeks to full, and because of to its complexity and expense, is usually carried out after a 12 months.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Vulnerability scanning, on the other hand, is automatic and done by tools which can be both installed specifically on your network or accessed on line. Vulnerability scanners operate countless numbers of security checks throughout your methods, developing a checklist of vulnerabilities with remediation advice. So it truly is achievable to run continuous security checks even with no possessing a full-time cyber security expert on your crew.
A person-off or standard?
Penetration assessments have lengthy been an critical part of many organization’s strategy to protect by themselves from cyber attack, and an superb way to uncover flaws at a specified point in time. But penetration testing on your own can depart corporations defenceless inbetween screening.
Executing once-a-year penetration tests as a key defence towards attackers has long been an crucial element of a lot of organisation’s method to defend themselves from cyber attack, for very good purpose. And though it is definitely better than executing nothing, it does have a rather sizeable drawback — what transpires in between assessments?
For case in point, what transpires when a critical new vulnerability is found in the Apache web server operating a sensitive customer portal during that extensive 12 months involving their yearly pentesting? Or a security misconfiguration is created by a junior developer? What if a network engineer briefly opens up a port on a firewall exposing a databases to the internet, and forgets to shut it? Whose position is it to detect these issues which, if remaining unchecked, could consequence in a knowledge breach or compromise?
Pentesting is not sufficient
Without the need of constant checking of issues these types of as these, they wouldn’t be recognized and mounted before attackers received the opportunity to exploit them.
Businesses that need to have robust bodily security frequently boast of getting 24/7 automated answers to prevent attackers 365 times a year. So why do some handle cyber security any differently? Particularly when on regular 20 new vulnerabilities get identified each individual single working day.
So you can see why occasionally scheduled pentesting alone is not adequate. Here is a uncomplicated analogy: it can be like examining the locks of your superior-security premises the moment a yr, but leaving it unmanned or not examining if it can be safe until finally your up coming annual as soon as more than. Seems crazy, ideal? Who’s examining that the door’s locked?
All around the clock protection
Whilst some providers nevertheless use annual pentesting as their only line of defence, lots of are setting up to see how routinely new threats come up and the value of steady, automatic menace scanning.
Scanning on a standard foundation with a vulnerability scanner like Intruder enhances guide testing by supplying organisations with ongoing security coverage involving manual penetration tests. Intruder’s automated scanner runs about the clock alerting people to new vulnerabilities as shortly as they surface.
Vulnerability scanning is by now the initial port of call for companies of all dimensions, with expert handbook penetration tests incorporated in alternatives like Intruder’s Vanguard employed as a potent backup.
It truly is not adequate to merely do 1 or the other. Fortunately, recognition is growing of the will need for a system which delivers defense all calendar year round.
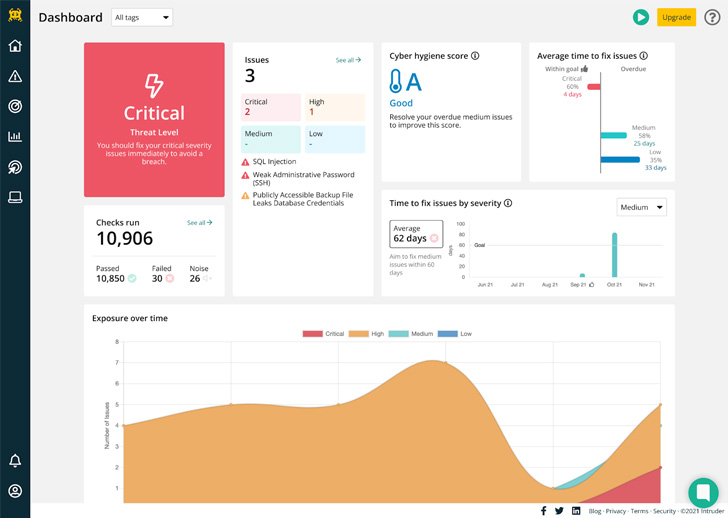
Intruder’s continual vulnerability scanning service helps you maintain on top of the newest vulnerabilities and alerts you to rising threats which affect your most-exposed units. Get started with a free of charge demo nowadays.
Observed this posting fascinating? Abide by THN on Facebook, Twitter and LinkedIn to go through a lot more distinctive written content we submit.
Some elements of this short article are sourced from:
thehackernews.com


 Apple Releases Security Updates to Patch Two New Zero-Day Vulnerabilities
Apple Releases Security Updates to Patch Two New Zero-Day Vulnerabilities