The malware loader recognized as Bumblebee is being progressively co-opted by menace actors linked with BazarLoader, TrickBot, and IcedID in their campaigns to breach target networks for publish-exploitation functions.
“Bumblebee operators conduct intense reconnaissance actions and redirect the output of executed commands to information for exfiltration,” Cybereason scientists Meroujan Antonyan and Alon Laufer said in a complex create-up.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Bumblebee initial came to gentle in March 2022 when Google’s Risk Assessment Team (TAG) unmasked the activities of an initial entry broker dubbed Unique Lily with ties to the TrickBot and the larger sized Conti collectives.
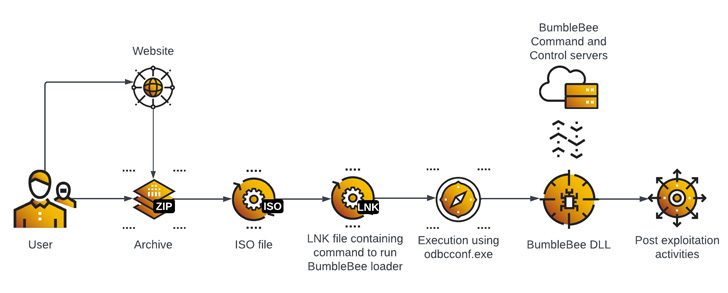
Generally shipped through initial access acquired through spear-phishing campaigns, the modus operandi has since been tweaked by eschewing macro-laced documents in favor of ISO and LNK documents, mostly in reaction to Microsoft’s choice to block macros by default.
“Distribution of the malware is completed by phishing e-mails with an attachment or a connection to a malicious archive that contains Bumblebee,” the researchers said. “The initial execution depends on the conclusion-consumer execution which has to extract the archive, mount an ISO graphic file, and simply click a Windows shortcut (LNK) file.”
The LNK file, for its portion, contains the command to start the Bumblebee loader, which is then used as a conduit for next-phase steps these types of as persistence, privilege escalation, reconnaissance, and credential theft.

Also used in the course of the attack is the Cobalt Strike adversary simulation framework on gaining elevated privileges on infected endpoints, enabling the threat actor to laterally move throughout the network. Persistence is achieved by deploying AnyDesk remote desktop program.
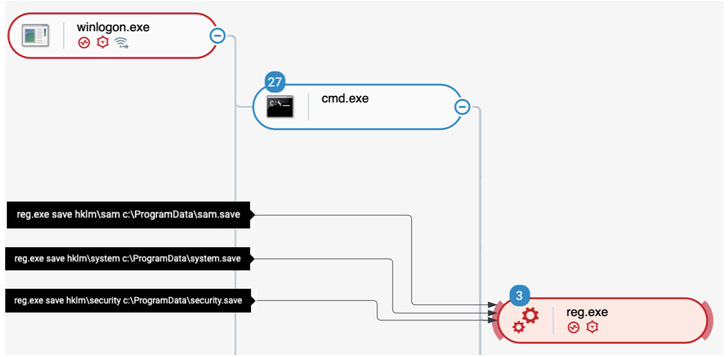
In the incident analyzed by Cybereason, the stolen credentials of a extremely privileged consumer were subsequently used to seize manage of the Energetic Directory, not to point out make a community user account for info exfiltration.
“The time it took among first obtain and Energetic Directory compromise was considerably less than two days,” the cybersecurity agency said. “Attacks involving Bumblebee must be taken care of as critical, […] and this loader is recognized for ransomware delivery.”
Found this posting fascinating? Observe THN on Fb, Twitter and LinkedIn to read through extra unique content we article.
Some parts of this posting are sourced from:
thehackernews.com


 Penetration Testing or Vulnerability Scanning? What’s the Difference?
Penetration Testing or Vulnerability Scanning? What’s the Difference?