If the Pulse Connect Safe gateway is portion of your business network, you have to have to be mindful of a newly learned critical zero-working day authentication bypass vulnerability (CVE-2021-22893) that is now staying exploited in the wild and for which there is no patch nevertheless.
At least two risk actors have been powering a collection of intrusions concentrating on defense, authorities, and fiscal corporations in the U.S. and somewhere else by leveraging critical vulnerabilities in Pulse Safe VPN equipment to circumvent multi-factor authentication protections and breach organization networks.
“A mixture of prior vulnerabilities and a previously unknown vulnerability discovered in April 2021, CVE-2021-22893, are liable for the first infection vector,” cybersecurity firm FireEye stated on Tuesday.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The organization has identified 12 malware family members affiliated with the exploitation of Pulse Protected VPN appliances.

The cybersecurity organization is also monitoring the action below two risk clusters UNC2630 and UNC2717 (“UNC” for Uncategorized) — the former joined to a break-in of U.S. Protection Industrial base (DIB) networks, when the latter was located focusing on a European corporation in March 2021 — with the investigation attributing UNC2630 to operatives functioning on behalf of the Chinese government, in addition to suggesting probable ties to another espionage actor APT5 based mostly on “solid similarities to historic intrusions dating back again to 2014 and 2015.”
Attacks staged by UNC2630 are thought to have commenced as early as August 2020, right before they expanded in October 2020, when UNC2717 began repurposing the same flaws to put in custom malware on the networks of government businesses in Europe and the U.S. The incidents continued until finally March 2021, according to FireEye.
The list of malware family members is as follows –
- UNC2630 – SLOWPULSE, RADIALPULSE, THINBLOOD, ATRIUM, PACEMAKER, SLIGHTPULSE, and PULSECHECK
- UNC2717 – HARDPULSE, QUIETPULSE, AND PULSEJUMP
Two further malware strains, STEADYPULSE and LOCKPICK, deployed all through the intrusions have not been connected to a particular team, citing deficiency of evidence.
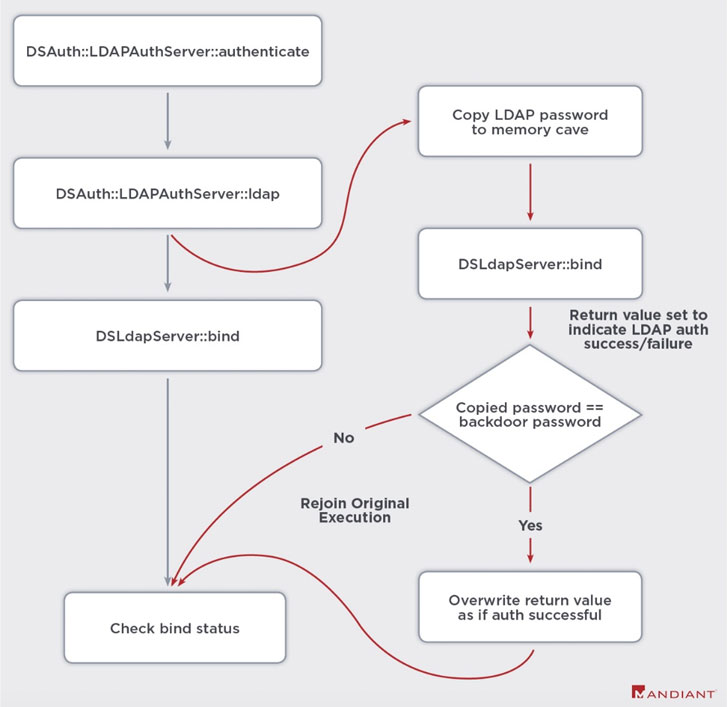
By exploiting Pulse Secure VPN weaknesses (CVE-2019-11510, CVE-2020-8260, CVE-2020-8243, and CVE-2021-22893), UNC2630 is stated to have harvested login credentials, making use of them to move laterally into the afflicted environments. In get to manage persistence to the compromised networks, the actor used respectable, but modified, Pulse Secure binaries and scripts to enable arbitrary command execution and inject web shells capable of carrying out file operations and working destructive code.

Ivanti, the firm guiding the Pulse Safe VPN, has launched temporary mitigations to address the arbitrary file execution vulnerability (CVE-2021-22893, CVSS rating: 10), although a resolve for the issue is envisioned to be in place by early Might. The Utah-centered enterprise acknowledged that the new flaw impacted a “extremely constrained quantity of customers,” including it has introduced a Pulse Link Secure Integrity Tool for consumers to look at for symptoms of compromise.
Pulse Protected prospects are advised to enhance to PCS Server version 9.1R.11.4 when it will become accessible.
Information of compromises influencing authorities companies, critical infrastructure entities, and other private sector corporations comes a week after the U.S. govt launched an advisory, warning companies of energetic exploitation of five publicly recognized vulnerabilities by the Russian Foreign Intelligence Provider (SVR), which include CVE-2019-11510, to acquire initial footholds into target products and networks.
Discovered this write-up exciting? Follow THN on Facebook, Twitter and LinkedIn to read much more unique content material we submit.
Some sections of this write-up are sourced from:
thehackernews.com


 With details sparse, vendors scramble to make sense of Biden 100-day grid security plan
With details sparse, vendors scramble to make sense of Biden 100-day grid security plan