Four months following security researchers uncovered a “Tetrade” of 4 Brazilian banking Trojans focusing on fiscal establishments in Brazil, Latin The usa, and Europe, new results show that the criminals driving the procedure have expanded their strategies to infect mobile gadgets with spy ware.
According to Kaspersky’s World-wide Analysis and Assessment Staff (Fantastic), the Brazil-based risk group Guildma has deployed “Ghimob,” an Android banking Trojan concentrating on economic apps from banking companies, fintech firms, exchanges, and cryptocurrencies in Brazil, Paraguay, Peru, Portugal, Germany, Angola, and Mozambique.
“Ghimob is a full-fledged spy in your pocket: as soon as infection is concluded, the hacker can access the infected device remotely, finishing the fraudulent transaction with the victim’s smartphone, so as to keep away from device identification, security measures executed by money establishments and all their anti-fraud behavioral methods,” the cybersecurity firm claimed in a Monday evaluation.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
In addition to sharing the exact infrastructure as that of Guildma, Ghimob carries on the modus operandi of working with phishing e-mails as a mechanism to distribute the malware, luring unsuspecting buyers into clicking destructive URLs that downloads the Ghimob APK installer.
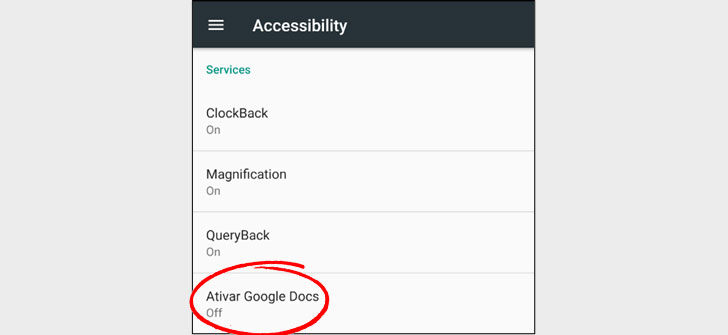
The Trojan, when installed on the unit, features a great deal identical to other cell RATs in that it masks its presence by hiding the icon from the app drawer and abuses Android’s accessibility options to attain persistence, disable handbook uninstallation and let the banking trojan to seize keystrokes, manipulate display screen information and supply whole distant control to the attacker.
“Even if the consumer has a display lock pattern in put, Ghimob is in a position to history it and afterwards replay it to unlock the unit,” the scientists said.
“When the cybercriminal is all set to execute the transaction, they can insert a black display as an overlay or open up some site in complete monitor, so though the person looks at that display screen, the criminal performs the transaction in the track record by employing the financial application running on the victim’s smartphone that the user has opened or logged in to.”
What is extra, Ghimob targets as numerous as 153 cellular applications, 112 of which are economic institutions based in Brazil, with cryptocurrency and banking applications in Germany, Portugal, Peru, Paraguay, Angola, and Mozambique accounting for the rest.
“Ghimob is the first Brazilian cellular banking trojan all set to broaden and concentrate on money establishments and their buyers dwelling in other nations,” Kaspersky scientists concluded. “The Trojan is very well organized to steal credentials from banking companies, fintechs, exchanges, crypto-exchanges, and credit cards from fiscal establishments operating in quite a few international locations.”
Identified this post attention-grabbing? Follow THN on Facebook, Twitter and LinkedIn to examine far more exceptional information we put up.
Some parts of this posting are sourced from:
thehackernews.com


 Breaking down a four-step process to email security
Breaking down a four-step process to email security