Google has declared a variety of consumer-experiencing and under-the-hood changes in an attempt to strengthen privacy and security, like rolling out two-factor authentication instantly to all suitable people and bringing iOS-styled privacy labels to Android application listings.
“These days we inquire folks who have enrolled in two-phase verification (2SV) to verify it is really genuinely them with a very simple tap by means of a Google prompt on their phone each time they indicator in,” the firm mentioned. “Before long we will start out routinely enrolling buyers in 2SV if their accounts are properly configured.”
Google Enjoy To Get Apple-Like Privacy Labels

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The Google Participate in Shop for Android is also having a big overhaul on the privacy front. The lookup giant said it plans to contain a new basic safety section for application listings that highlights the type of knowledge is gathered and saved — such as approximate or specific place, contacts, own facts, photos and movies, and audio documents — and how the information is employed, whether be it for delivering app operation, personalization, or promoting.

The transparency steps into how applications use data echo a identical press by Apple, which rolled out privacy labels in the Application Store in December 2020 with an intention to condense an app’s data assortment methods in an uncomplicated-to-recognize and consumer-friendly structure.
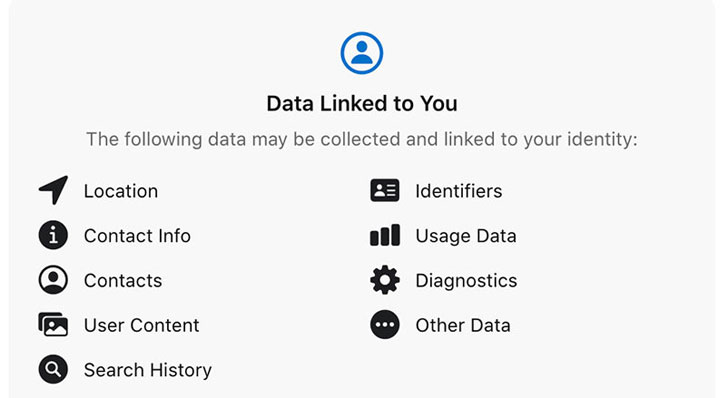
Interestingly, the enforcement goes outside of the privacy-oriented nourishment facts connected to each individual application entry, for the changes will also require app builders, which includes Google, to offer facts about whether their apps adhere to security methods, like facts encryption, comply with Google’s guidelines all-around applications and games aimed at children, and describe why a specific piece of info is currently being gathered, or if buyers have a preference in opting out of knowledge sharing.
A different essential change is that the part will also highlight no matter whether an impartial 3rd-party has confirmed the app’s privacy labels and regardless of whether people can request that their information be deleted should they make your mind up to uninstall the app.
The 3rd-party verification appears to be a go to counter criticism like that confronted by Apple for failing to vet apps that offered “misleading or flat-out inaccurate” labels. The adjustments are predicted to go into effect in the 2nd fiscal quarter of 2022.
Google Debuts Cosign for Verifying Container Photos
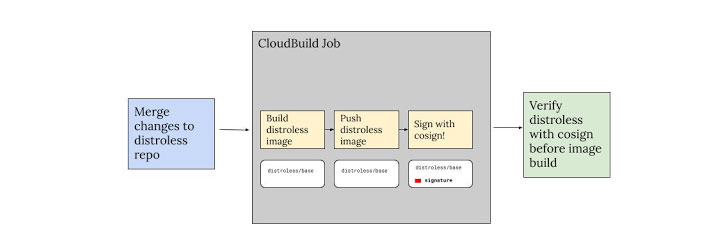
Before this March, Google, Linux Basis, and Purple Hat introduced a device identified as Sigstore to protected application offer chains by allowing for builders to sign their code and for end users to validate them to avert software supply-chain attacks like dependency confusion.
Now, the organization is increasing on that energy with Cosign, a new command-line instrument that aims to simplify signing and verifying container images, and as a consequence, reduce end users from slipping prey to typosquatting attacks or “get a destructive image if the distroless develop method was compromised.”
Google Chrome Will get Components-Enforced Exploit Protection
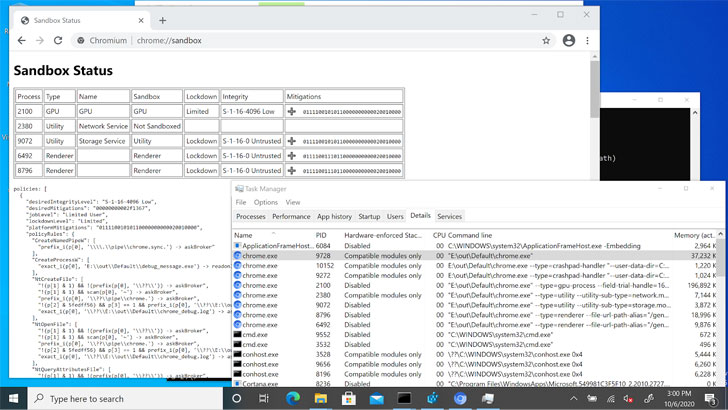
Which is not all. Google on Tuesday unveiled that Chrome 90 for Windows, which was released on April 13, 2021, will come outfitted with a new Windows 10 security function known as “Hardware-enforced Stack Safety” to safeguard the memory stack from arbitrary code execution attacks.
“Enabling Components-enforced Stack Protection will layer with existing and upcoming steps to make exploitation a lot more hard and so a lot more expensive for an attacker,” Alex Gough of Chrome System Security Group reported.
Observed this posting interesting? Follow THN on Fb, Twitter and LinkedIn to read extra exclusive material we write-up.
Some parts of this report are sourced from:
thehackernews.com