German authorities past week disclosed that a ransomware attack on the College Hospital of Düsseldorf (UKD) brought about a failure of IT programs, resulting in the demise of a girl who had to be sent to yet another hospital that was 20 miles away.
The incident marks the very first recorded casualty as a consequence of cyberattacks on critical health care facilities, which has ramped up in new months.
The attack, which exploited a Citrix ADC CVE-2019-19781 vulnerability to cripple the medical center techniques on September 10, is explained to have been “misdirected” in that it was originally intended for Heinrich Heine University, in accordance to an extortion be aware left by the perpetrators.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

Soon after legislation enforcement contacted the danger actors and informed them that they had encrypted a medical center, the operators guiding the attack withdrew the ransom desire and presented the decryption crucial.
The scenario is now getting dealt with as a homicide, BBC News reported over the weekend.
Unpatched Vulnerabilities Turn into Gateway to Ransomware Attacks
Even though various ransomware gangs stated early on in the pandemic that they would not intentionally goal hospitals or health-related amenities, the recurring attacks prompted the Interpol to issue a warning cautioning hospitals in opposition to ransomware assaults made to lock them out of their critical methods in an endeavor to extort payments.
Weak qualifications and VPN vulnerabilities have verified to be a blessing in disguise for threat actors to split into the interior networks of companies and companies, leading cybersecurity organizations in the U.S. and U.K. to publish multiple advisories about active exploitation of the flaws.
“The [Federal Office for Information Security] is turning into more and more mindful of incidents in which Citrix techniques had been compromised just before the security updates that were created offered in January 2020 were being installed,” the German cybersecurity agency said in an alert past 7 days.
“This implies that attackers nevertheless have accessibility to the system and the networks powering it even right after the security hole has been shut. This likelihood is currently ever more currently being applied to have out attacks on influenced corporations.”
The progress also coincides with a fresh advisory from the U.K. Countrywide Cyber Security Centre (NCSC), which reported it is observed an uptick in ransomware incidents concentrating on instructional establishments at least because August 2020, whilst urging faculties and universities to put into practice a “defence in depth” method to defend from such malware attacks.
Some of the impacted institutions included Newcastle and Northumbria Universities, between others.
Citing Distant Desktop Protocol (RDP), susceptible software or hardware, and email phishing as the a few most common infection vectors, the agency recommended organizations to sustain up-to-day offline backups, undertake endpoint malware defense, safe RDP providers making use of multi-issue authentication, and have an efficient patch management technique in spot.
A Spike in Ransomware Bacterial infections
If anything at all, the ransomware crisis seems to be only acquiring worse. Historical data gathered by Temple University’s Treatment cybersecurity lab has proven that there have been a full of 687 publicly disclosed scenarios in the U.S. due to the fact 2013, with 2019 and 2020 by yourself accounting for a lot more than fifty percent of all noted incidents (440).
Federal government services, academic establishments, and health care corporations are the most commonly strike sectors, as for each the evaluation.
And if 2020 is any indication, assaults against colleges and universities are demonstrating no indicators of slowing down.
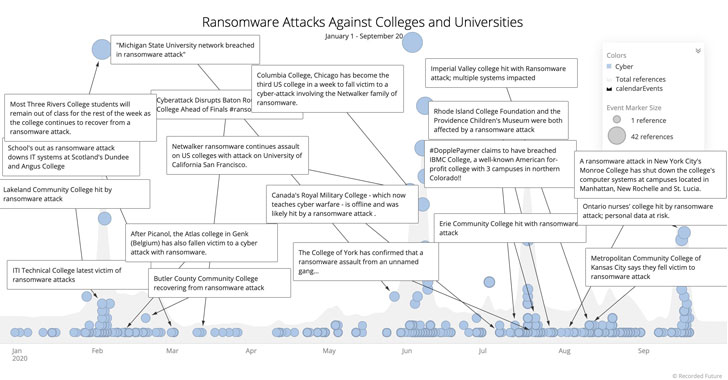
Allan Liska, a risk intelligence analyst at Recorded Potential, discovered there experienced been at least 80 publicly noted ransomware bacterial infections targeting the instruction sector to date this yr, a huge bounce from 43 ransomware attacks for the complete of 2019.
“Part of this alter can be attributed to extortion websites, which force much more victims to announce assaults,” Liska stated in a tweet. “But, in typical, ransomware actors have extra desire in likely right after colleges and universities, and they are generally simple targets.”
You can read through much more about NCSC’s mitigation measures here. For much more steering on proofing businesses in opposition to ransomware assaults, head to US Cybersecurity Security and Infrastructure Security Agency’s response guide here.
Identified this posting fascinating? Stick to THN on Fb, Twitter and LinkedIn to read additional distinctive material we article.
Some parts of this article is sourced from:
thehackernews.com


 US Judge Blocks Trump’s WeChat Ban
US Judge Blocks Trump’s WeChat Ban