A critical security vulnerability in a well-liked video clip contacting application development package (SDK) could have authorized an attacker to spy on ongoing non-public video clip and audio phone calls.
Which is in accordance to new exploration published by the McAfee Advanced Risk Investigation (ATR) workforce right now, which uncovered the aforementioned flaw in Agora.io’s SDK employed by a number of social applications these kinds of as eHarmony, A great deal of Fish, MeetMe, and Skout health care applications like Talkspace, Practo, and Dr. First’s Backline and in the Android app which is paired with “temi” own robotic.
California-centered Agora is a online video, voice, and live interactive streaming platform, allowing developers to embed voice and online video chat, true-time recording, interactive stay streaming, and real-time messaging into their applications. The company’s SDKs are approximated to be embedded into cellular, web, and desktop programs across a lot more than 1.7 billion units globally.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

McAfee disclosed the flaw (CVE-2020-25605) to Agora.io on April 20, 2020, pursuing which the company unveiled a new SDK on December 17, 2020, to remediate the threat posed by the vulnerability.
The security weak point, which is the consequence of incomplete encryption, could have been leveraged by poor actors to launch gentleman-in-the-middle attacks and intercept communications in between two get-togethers.
“Agora’s SDK implementation did not allow for programs to securely configure the set up of video/audio encryption, therefore leaving a likely for hackers to snoop on them,” the researchers stated.
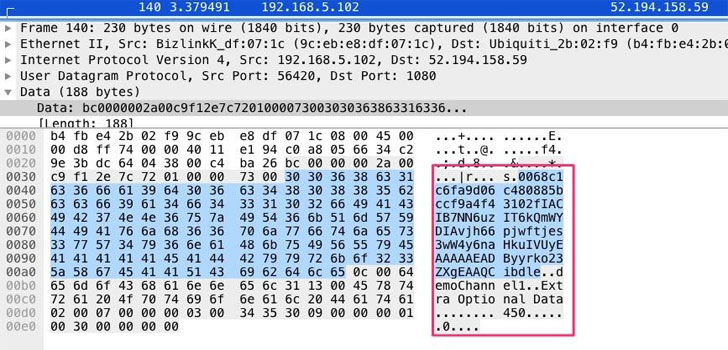
Particularly, the perform liable for connecting an close-person to a connect with passed parameters this kind of as App ID and authentication token parameter in plaintext, thereby permitting an attacker to abuse this shortcoming to sniff network targeted traffic so as to assemble contact info and subsequently start their individual Agora online video application to dial into calls without having the attendees’ expertise stealthily.
Although there’s no proof that the vulnerability was exploited in the wild, the enhancement when all over again underscores the will need for securing purposes to safeguard user privacy.
“In the planet of on the internet courting, a breach of security or the means to spy on phone calls could lead to blackmail or harassment by an attacker,” the scientists concluded. “Other Agora developer purposes with smaller customer bases, these kinds of as the temi robotic, are employed in several industries this kind of as hospitals, where by the ability to spy on discussions could direct to the leak of delicate medical facts.”
It is really remarkably advised that builders making use of Agora SDK up grade to the latest version to mitigate the risk.
Located this posting intriguing? Adhere to THN on Facebook, Twitter and LinkedIn to read through much more unique content we article.
Some areas of this report are sourced from:
thehackernews.com


 F-Secure: CISOs Must Develop Emotional Intelligence Skills to Succeed
F-Secure: CISOs Must Develop Emotional Intelligence Skills to Succeed