An superior persistent risk (APT) actor has been tracked in a new campaign deploying Android malware via the Syrian e-Authorities Web Portal, indicating an upgraded arsenal developed to compromise victims.
“To the most effective of our information, this is the initial time that the team has been publicly observed using malicious Android applications as part of its attacks,” Craze Micro researchers Zhengyu Dong, Fyodor Yarochkin, and Steven Du stated in a complex produce-up released Wednesday.
StrongPity, also codenamed Promethium by Microsoft, is thought to have been energetic considering that 2002 and has normally centered on targets throughout Turkey and Syria. In June 2020, the espionage risk actor was related to a wave of actions that banked on watering gap attacks and tampered installers, which abuse the level of popularity of authentic applications, to infect targets with malware.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

“Promethium has been resilient in excess of the yrs,” Cisco Talos disclosed past calendar year. “Its strategies have been exposed a number of occasions, but that was not more than enough to make the actors powering it to make them cease. The reality that the group does not refrain from launching new strategies even immediately after staying uncovered displays their resolve to achieve their mission.”
The most current procedure is no distinctive in that it underscores the danger actor’s propensity toward repackaging benign apps into trojanized variants to aid the attacks.
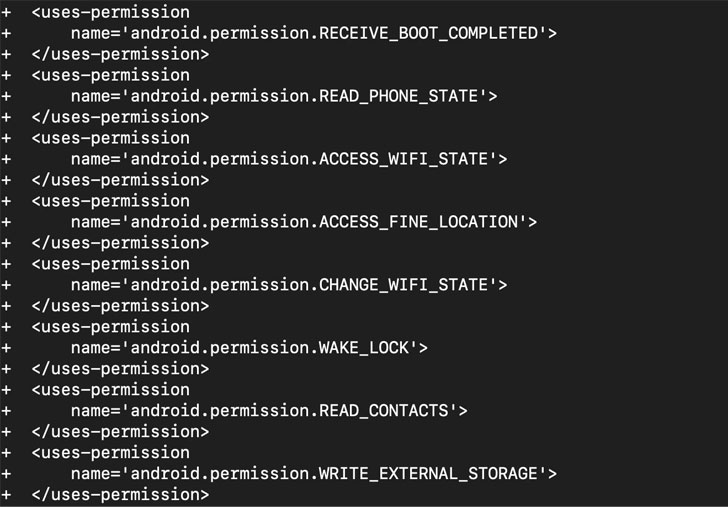
The malware, masquerading as the Syrian e-Gov Android software, is explained to have been produced in May possibly 2021, with the app’s manifest file (“AndroidManifest.xml”) modified to explicitly request added permissions on the phone, which include the skill to study contacts, compose to exterior storage, keep the product awake, entry data about cellular and Wi-Fi networks, precise place, and even allow the application to have alone begun as shortly as the procedure has concluded booting.
Also, the malicious application is made to accomplish prolonged-managing jobs in the history and set off a request to a distant command-and-management (C2) server, which responds back again with an encrypted payload containing a settings file that makes it possible for the “malware to alter its conduct according to the configuration” and update its C2 server handle.
Previous but not the very least, the “really modular” implant has the capacity to hoover knowledge saved on the contaminated product, this kind of as contacts, Phrase and Excel paperwork, PDFs, photos, security keys, and data files saved employing Dagesh Pro Term Processor (.DGS), amongst many others, all of which are exfiltrated back to the C2 server.

Inspite of no acknowledged community stories of StrongPity working with malicious Android purposes in their attacks, Craze Micro’s attribution to the adversary stems from the use of a C2 server that has earlier been utilised in intrusions joined to the hacking team, notably a malware campaign documented by AT&T’s Alien Labs in July 2019 that leveraged tainted versions of the WinBox router management software package, WinRAR, and other reliable utilities to breach targets.
“We believe that that the threat actor is discovering various strategies of delivering the purposes to opportunity victims, this sort of as working with bogus applications and using compromised internet sites as watering holes to trick consumers into putting in malicious apps,” the scientists stated.
“Normally, these internet sites would need its customers to down load the purposes immediately onto their gadgets. In get to do so, these buyers would be essential to allow installation of the applications from ‘unknown sources’ on their products. This bypasses the ‘trust-chain’ of the Android ecosystem and tends to make it less complicated for an attacker to provide more malicious factors,” they included.
Found this posting interesting? Observe THN on Fb, Twitter and LinkedIn to read through far more distinctive content we publish.
Some parts of this post are sourced from:
thehackernews.com


 Reduce End-User Password Change Frustrations
Reduce End-User Password Change Frustrations