Firms know they require to secure their shopper-side scripts. Written content security procedures (CSPs) are a terrific way to do that. But CSPs are cumbersome. Just one oversight and you have a perhaps sizeable consumer-facet security gap. Finding these gaps usually means lengthy and monotonous hours (or times) in guide code critiques by way of 1000’s of strains of script on your web applications. Automatic information security policies can assistance streamline the code evaluate process by very first determining all first- and 3rd-party scripts and the property they obtain, and then making an suitable articles security coverage to assistance much better safe the shopper-side attack surface area.
There are couple of developers or AppSec pros who claim to delight in deploying CSPs. 1st, the CSP has to operate for the certain web software. Then the team requires to make sure it gives the ideal stage of security. The CSP also are unable to conflict with any present widgets or plugins (or the selection must be designed to not deploy the CSP or deactivate individuals plugins, which can result in issues in other spots, these as shopper engagement, advertising, and profits).

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
And then, when a CSP fails, there is the dreaded audit to establish the why and wherever.
The CSP-audit-avoidance difficulty (aka steering clear of manual code critiques or loss of life by a thousand scripts) is pretty common. Currently, client-aspect web purposes include countless numbers of scripts, assembled from a number of open-source libraries or other third- and fourth-party repositories. Couple growth or security groups get the time to preserve a in-depth report of all the scripts utilized in web software assembly, together with their functions, their sources, and no matter if they’ve been updated or patched to handle any identified security issues.
Even when groups do identify all third-party script sources, which is no guarantee that the scripts are secure. Ongoing issues nevertheless surface area with bundle professionals containing obfuscated and malicious JavaScript utilised to harvest sensitive information from internet websites and web programs. In a modern example, scientists found that malicious deals had been downloaded 27,000 instances by unsuspecting developers.
Sadly, the CSP-audit-avoidance difficulty expands an by now substantial consumer-aspect attack floor.
The issues with CSPs have nothing to do with their value. CSPs are great at delivering violation reporting and coverage optimization and support uncover susceptible scripts that direct to JavaScript injection attacks, cross-site scripting (XSS), and skimming attacks, like Magecart. Manual written content security insurance policies are just a agony to deal with, which means developers could stay clear of critical CSP procedures, primary to elevated security risk.
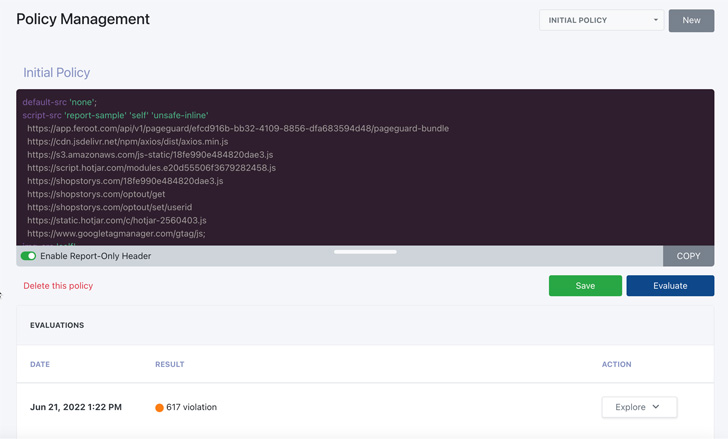
Automated content material security insurance policies aid handle CSPs to much better shield the consumer-side attack surface and take away the risk connected with handbook CSP oversight. By pinpointing all initial- and third-party scripts, digital assets, and the knowledge these belongings obtain, organizations can streamline the CSP development and administration course of action, and enhance over-all shopper-aspect security. Automatic CSPs are managed at the area level for superior reporting and version control.
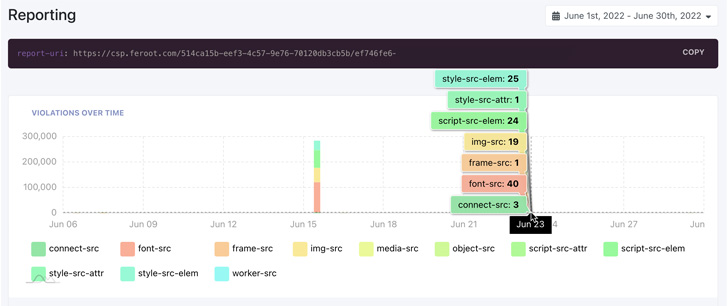
Automatic CSPs operate by crawling a web site or web software and initiating synthetic users to assess how scripts are functioning on the web software and what type of knowledge the script could be accessing. The system then generates the CSP to align it with the security wants of the website or web application. Automatic CSPs also get the job done inside the actual creation setting, to emulate insurance policies for quick testing (and stay clear of regular CSP deployment in a growth natural environment) and concentration on bringing coverage violations as close to zero as feasible.
More capabilities of an automatic CSP contain producing new policies immediately after a detected violation to permit speedy updates and tackle existing security threats and ingesting log data into security incident and event management (SIEM) and other log-based data assortment devices for integration into existing security tactics and workflows.
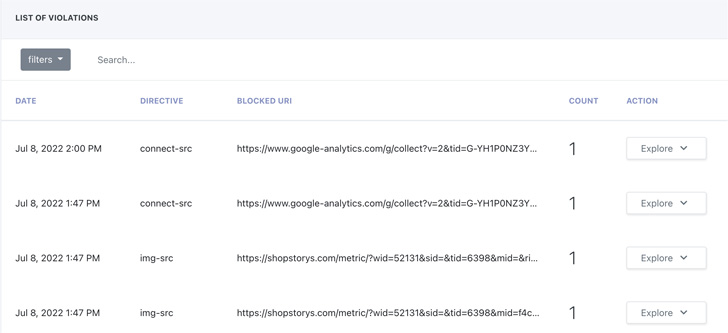
With violation reporting entirely integrated, an automated CSP remedy complements current security procedures and workflows. It also presents critical help for regulatory and compliance standards like PCI DSS 4., HIPAA, and other folks.
Feroot Security delivers DomainGuard, a intent-developed, automated CSP that will help corporations manage their consumer-side attack area by simplifying the written content security coverage management method. DomainGuard integrates violation reporting with current security equipment to enhance recent security procedures and workflows and significantly reduce the time it usually takes to create and deal with CSPs throughout teams, web-sites, and web applications.
Located this short article fascinating? Stick to THN on Facebook, Twitter and LinkedIn to go through far more distinctive articles we write-up.
Some sections of this article are sourced from:
thehackernews.com

 Microsoft makes Windows Autopatch generally available to enterprise users
Microsoft makes Windows Autopatch generally available to enterprise users