In nevertheless one more indicator of how hacking teams are brief to capitalize on environment gatherings and improvise their attack strategies for maximum affect, threat actors have been identified impersonating Amnesty Intercontinental to distribute malware that purports to be security software made to safeguard in opposition to NSO Group’s Pegasus surveillanceware.
“Adversaries have set up a phony site that seems to be like Amnesty International’s — a human legal rights-targeted non-governmental firm — and points to a promised antivirus resource to protect against the NSO Group’s Pegasus software,” Cisco Talos researchers mentioned. “Having said that, the download basically installs the tiny-recognized Sarwent malware.”


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
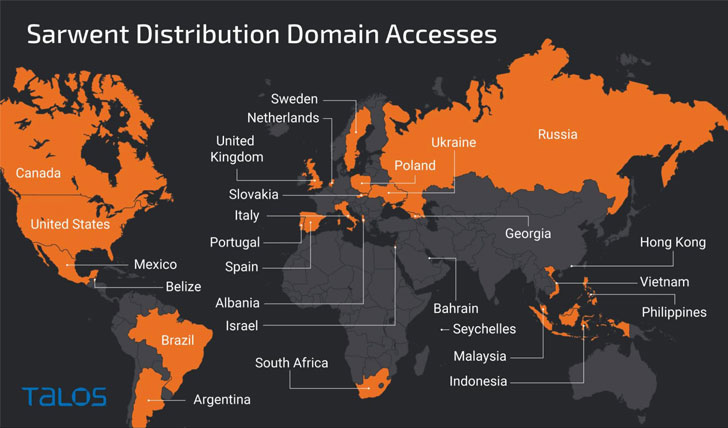
The nations around the world most affected by the campaign involve the U.K., the U.S., Russia, India, Ukraine, Czech Republic, Romania, and Colombia. Whilst it can be unclear as to how the victims are lured into visiting the faux Amnesty Global site, the cybersecurity company surmised the attacks could be aimed at end users who may well be particularly browsing for safety in opposition to this risk.
The growth will come on the heels of an explosive investigation in July 2021 that revealed prevalent abuse of the Israeli firm’s Pegasus “armed service-grade spy ware” to aid human rights violations by surveilling heads of condition, activists, journalists, and legal professionals all around the environment. The NGO has since also launched a Cell Verification Toolkit (MVT) to enable people today scan their iPhone and Android equipment for evidence of compromise.
Apart from making use of social engineering tips by designing a rogue web page with an identical look and really feel of Amnesty International’s authentic portal, the modus operandi aims to trick the visitor into downloading an “Amnesty Anti Pegasus Computer software” beneath the guise of an antivirus device that attributes capabilities to allow the bad actor obtain way a distant way into the compromised device and exfiltrate sensitive information and facts, this sort of as login credentials.

The Sarwent sample used in the minimal-quantity marketing campaign is a very-tailored variant coded in Delphi and is able of allowing for distant desktop obtain by VNC or RDP and executing command line or PowerShell instructions obtained from an attacker-controlled domain, the success of which are despatched back again to the server.
Talos attributed the infections with substantial self confidence to a Russian-talking actor finding in the country and regarded for mounting attacks involving the Sarwent backdoor because at the very least January 2021 sprawling throughout a selection of victims, noting the degree of modifications made to the meant antivirus as likely evidence that “the operator has entry to the resource code of the Sarwent malware.”
“The campaign targets persons who could be concerned that they are qualified by the Pegasus adware,” the researchers said. “This focusing on raises issues of doable condition involvement, but there is inadequate data […] to make any determination on which point out or nation. It is attainable that this is only a economically inspired actor seeking to leverage headlines to acquire new entry.”
Found this report appealing? Follow THN on Fb, Twitter and LinkedIn to read far more unique information we submit.
Some parts of this write-up are sourced from:
thehackernews.com


 Update Google Chrome ASAP to Patch 2 New Actively Exploited Zero-Day Flaws
Update Google Chrome ASAP to Patch 2 New Actively Exploited Zero-Day Flaws