Cybersecurity researchers have disclosed a new class of vulnerabilities impacting main DNS-as-a-Provider (DNSaaS) providers that could enable attackers to exfiltrate delicate information from company networks.
“We observed a uncomplicated loophole that allowed us to intercept a part of all over the world dynamic DNS visitors going through managed DNS vendors like Amazon and Google,” scientists Shir Tamari and Ami Luttwak from infrastructure security company Wiz said.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Contacting it a “bottomless very well of beneficial intel,” the treasure trove of details consists of interior and exterior IP addresses, computer system names, employee names and destinations, and particulars about organizations’ web domains. The findings have been offered at the Black Hat United states 2021 security conference previous 7 days.
“The site visitors that leaked to us from internal network traffic gives destructive actors all the intel they would ever need to have to launch a thriving attack,” the scientists extra. “Much more than that, it presents anyone a bird’s eye perspective on what is occurring inside firms and governments. We liken this to acquiring country-state stage spying capacity – and obtaining it was as easy as registering a domain.”
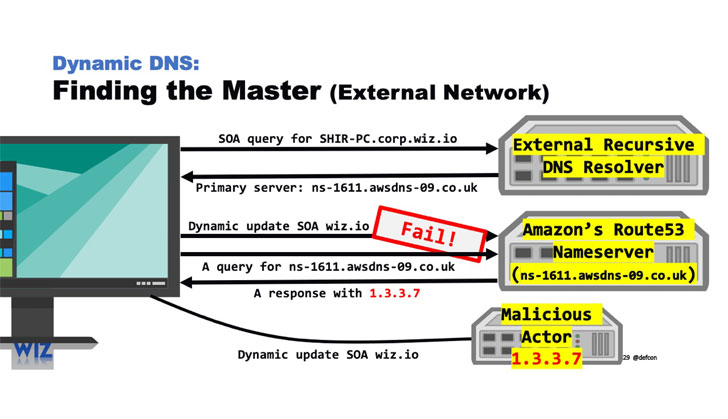
The exploitation system hinges on registering a area on Amazon’s Route53 DNS provider (or Google Cloud DNS) with the similar name as the DNS name server — which supplies the translation (aka resolution) of domain names and hostnames into their corresponding Internet Protocol (IP) addresses — ensuing in a state of affairs that properly breaks the isolation amongst tenants, so letting worthwhile details to be accessed.
In other words, by building a new domain on the Route53 system within AWS identify server with the exact moniker and pointing the hosted zone to their interior network, it results in the Dynamic DNS targeted traffic from Route53 customers’ endpoints to be hijacked and despatched immediately to the rogue and identical-named server, thus producing an straightforward pathway into mapping company networks.

“The dynamic DNS traffic we wiretapped arrived from more than 15,000 organizations, together with Fortune 500 firms, 45 U.S. government companies, and 85 international govt organizations,” the scientists explained. “The details included a wealth of important intel like inner and external IP addresses, laptop names, employee names, and office destinations.”
When Amazon and Google have given that patched the issues, the Wiz investigate group has also launched a instrument to allow companies examination if their internal DDNS updates are staying leaked to DNS companies or destructive actors.
Identified this post intriguing? Stick to THN on Fb, Twitter and LinkedIn to examine much more distinctive articles we put up.
Some elements of this article are sourced from:
thehackernews.com

 MSPs and MSSPs Can Increase Profit Margins With Cynet 360 Platform
MSPs and MSSPs Can Increase Profit Margins With Cynet 360 Platform