A Chinese cyberespionage group recognised for targeting Southeast Asia leveraged flaws in the Microsoft Exchange Server that came to gentle earlier this March to deploy a previously undocumented variant of a remote entry trojan (RAT) on compromised systems.
Attributing the intrusions to a danger actor named PKPLUG (aka Mustang Panda and HoneyMyte), Palo Alto Networks’ Device 42 danger intelligence crew claimed it recognized a edition of the modular PlugX malware termed Thor that was delivered as a put up-exploitation instrument to a single of the compromised servers. Dating back to as early as 2008, PlugX is a totally-featured next-phase implant with capabilities these as file upload, download, and modification, keystroke logging, webcam command, and entry to a remote command shell.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
“The variant noticed […] is one of a kind in that it incorporates a change to its core supply code: the replacement of its trademark phrase ‘PLUG’ to ‘THOR,'” Unit 42 scientists Mike Harbison and Alex Hinchliffe pointed out in a technological generate-up published Tuesday. “The earliest THOR sample uncovered was from August 2019, and it is the earliest regarded occasion of the rebranded code. New features had been noticed in this variant, which include increased payload-shipping and delivery mechanisms and abuse of trustworthy binaries.”
Following Microsoft disclosed on March 2 that China-centered hackers — codenamed Hafnium — ended up exploiting zero-working day bugs in Exchange server collectively known as ProxyLogon to steal delicate facts from find targets, multiple danger actors, such as ransomware teams (DearCry and Black Kingdom) and crypto-mining gangs (LemonDuck), have been also noticed exploiting the flaws to hijack Exchange servers and put in a web shell that granted code execution at the optimum privilege degree.
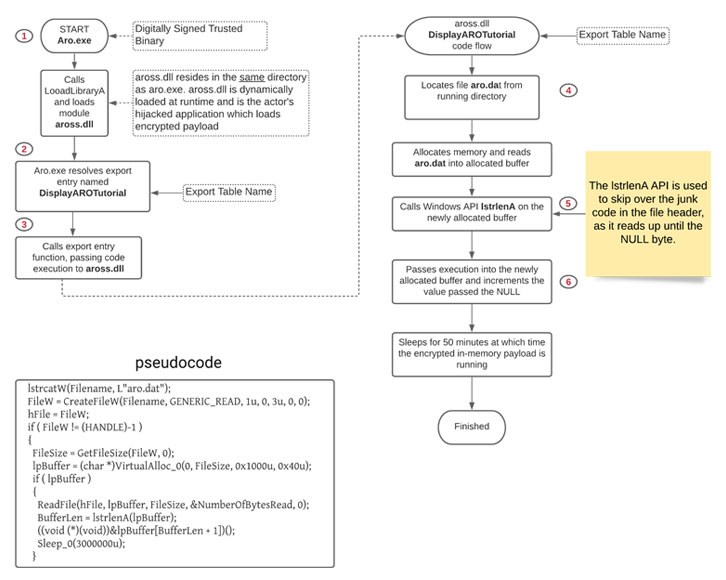
PKPLUG now joins the list, according to Device 42, who uncovered the attackers bypassing antivirus detection mechanisms to goal Microsoft Trade Server by leveraging reputable executables this sort of as BITSAdmin to retrieve a seemingly innocuous file (“Aro.dat”) from an actor-controlled GitHub repository. The file, which properties the encrypted and compressed PlugX payload, alludes to a freely offered highly developed repair and optimization tool that’s created to cleanse up and correct issues in the Windows Registry.

The most recent sample of PlugX comes outfitted with a wide variety of plug-ins that “deliver attackers various capabilities to check, update and interact with the compromised technique to fulfil their objectives,” the scientists mentioned. THOR’s links to PKPLUG stem from piecing together the command-and-control infrastructure as nicely as overlaps in the destructive behaviors detected among the other lately uncovered PlugX samples.
Added indicators of compromise linked with the attack can be accessed listed here. Device 42 has also manufactured offered a Python script that can decrypt and unpack encrypted PlugX payloads devoid of possessing the linked PlugX loaders.
Observed this article exciting? Adhere to THN on Facebook, Twitter and LinkedIn to go through a lot more special articles we submit.
Some components of this report are sourced from:
thehackernews.com


 Zyxel USG Flex 200 review: A timely and effective solution
Zyxel USG Flex 200 review: A timely and effective solution