A previously not known Chinese-speaking danger actor has been linked to a long-standing evasive procedure aimed at South East Asian targets as much back again as July 2020 to deploy a kernel-manner rootkit on compromised Windows devices.
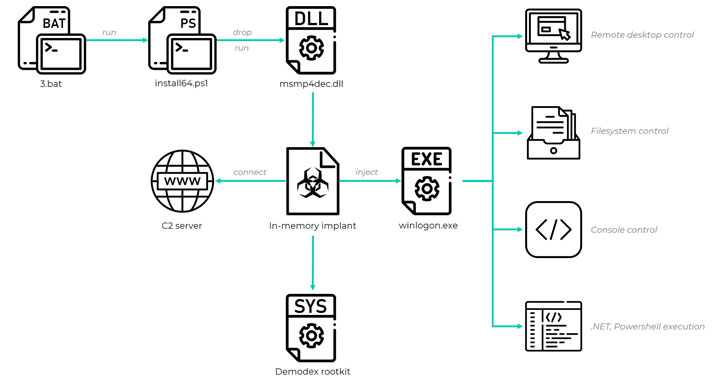
Attacks mounted by the hacking group, dubbed GhostEmperor by Kaspersky, are also said to have utilized a “subtle multi-stage malware framework” that will allow for offering persistence and remote regulate around the targeted hosts.
The Russian cybersecurity agency termed the rootkit Demodex, with infections documented throughout a number of high-profile entities in Malaysia, Thailand, Vietnam, and Indonesia, in addition to outliers positioned in Egypt, Ethiopia, and Afghanistan.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

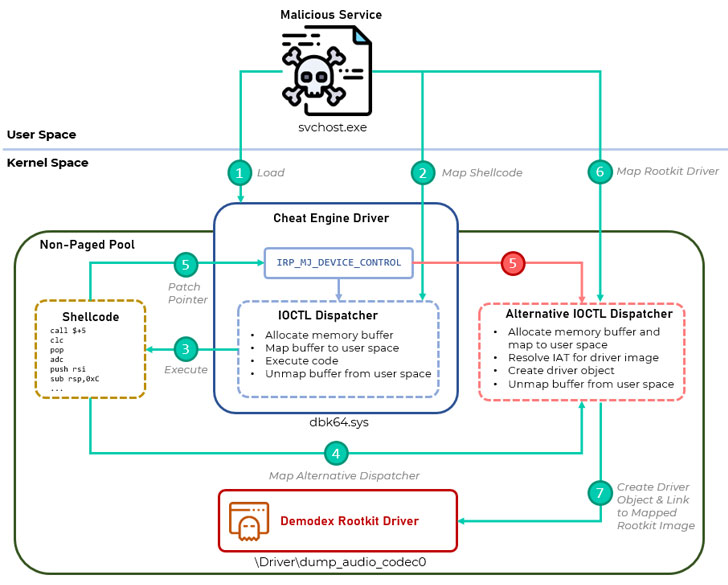
“[Demodex] is used to cover the consumer mode malware’s artefacts from investigators and security alternatives, even though demonstrating an appealing undocumented loading scheme involving the kernel mode ingredient of an open up-supply job named Cheat Motor to bypass the Windows Driver Signature Enforcement mechanism,” Kaspersky researchers reported.
GhostEmperor infections have been located to leverage numerous intrusion routes that culminate in the execution of malware in memory, main amid them currently being exploiting acknowledged vulnerabilities in general public-going through servers such as Apache, Window IIS, Oracle, and Microsoft Trade — which includes the ProxyLogon exploits that came to light-weight in March 2021 — to get an original foothold and laterally pivot to other pieces of the victim’s network, even on equipment operating modern variations of the Windows 10 working technique.
Adhering to a successful breach, select an infection chains that resulted in the deployment of the rootkit ended up carried out remotely through a different system in the same network applying legitimate program this sort of as WMI or PsExec, primary to the execution of an in-memory implant capable of installing further payloads throughout operate time.
Notwithstanding its reliance on obfuscation and other detection-evasion methods to elude discovery and analysis, Demodex receives around Microsoft’s Driver Signature Enforcement mechanism to permit the execution of unsigned, arbitrary code in kernel area by leveraging a genuine and open up-source signed driver named (“dbk64.sys”) that is shipped together with Cheat Engine, an application made use of to introduce cheats into video clip games.

“With a long-standing operation, substantial profile victims, [and] superior toolset […] the underlying actor is extremely experienced and completed in their craft, both equally of which are apparent by way of the use of a wide set of strange and innovative anti-forensic and anti-investigation approaches,” the scientists explained.
The disclosure will come as a China-connected risk actor codenamed TAG-28 has been uncovered as staying behind intrusions in opposition to Indian media and government companies these kinds of as The Occasions Group, the One of a kind Identification Authority of India (UIDAI), and the police division of the state of Madhya Pradesh.
Recorded Long term, previously this week, also unearthed destructive exercise focusing on a mail server of Roshan, just one of Afghanistan’s greatest telecommunications providers, that it attributed to four distinct Chinese point out-sponsored actors — RedFoxtrot, Calypso APT, as perfectly as two different clusters making use of backdoors linked with the Winnti and PlugX teams.
Uncovered this article attention-grabbing? Follow THN on Facebook, Twitter and LinkedIn to examine much more unique information we publish.
Some components of this report are sourced from:
thehackernews.com

 Amazon, Microsoft, Google back creation of Trusted Cloud Principles
Amazon, Microsoft, Google back creation of Trusted Cloud Principles