Cisco has patched a critical security vulnerability impacting its Organization Network Functionality Virtualization Infrastructure Program (NFVIS) that could be exploited by an attacker to choose handle of an affected technique.
Tracked as CVE-2021-34746, the weak point has been rated 9.8 out of a maximum of 10 on the Prevalent Vulnerability Scoring Procedure (CVSS) and could enable a distant attacker to circumvent authentication and log in to a vulnerable unit as an administrator.
The network equipment maker mentioned it truly is mindful of a publicly accessible proof-of-concept (PoC) exploit code targeting the vulnerability, but extra it really is not detected any productive weaponization attempts in the wild.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The issue is triggered because of to incomplete validation of user-provided enter that is handed to an authentication script during the signal-in method, enabling an attacker to inject parameters into an authentication ask for. “A effective exploit could allow for the attacker to bypass authentication and log in as an administrator to the affected gadget,” the company reported in an advisory.
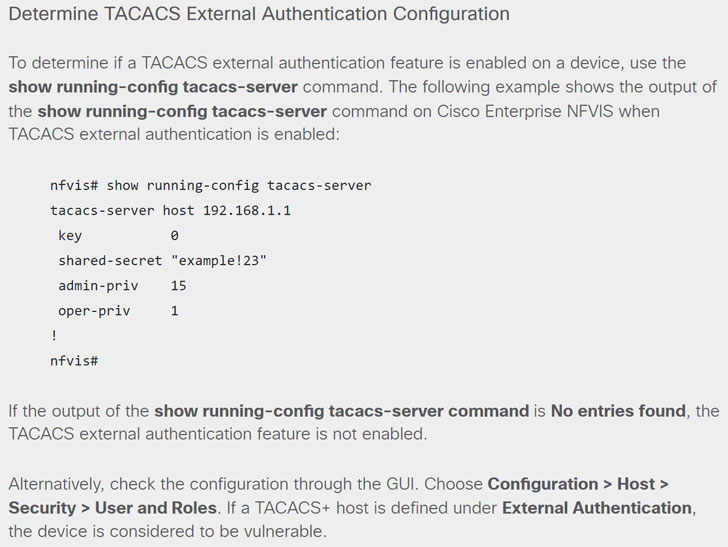
It is truly worth pointing out that company NFVIS deployments are impacted by this vulnerability only if TACACS exterior authentication process is configured on a specific gadget, which can be identified by operating the “display jogging-config tacacs-server” command. “If the output of the show working-config tacacs-server command is No entries located, the TACACS external authentication characteristic is not enabled,” the business mentioned.
The patches occur a small above a week after Cisco rolled out updates to handle a critical security vulnerability (CVE-2021-1577) impacting the Software Plan Infrastructure Controller (APIC) interface utilised in its Nexus 9000 Sequence Switches that could be potentially abused to study or generate arbitrary information on a vulnerable method.
The corporation is also in the system of readying fixes for a zero-day bug (CVE-2021-1585) in its Adaptive Security System Manager (ADSM) Launcher that could let an unauthenticated, remote attacker to execute arbitrary code on a user’s running method.
Observed this short article interesting? Adhere to THN on Fb, Twitter and LinkedIn to study additional distinctive written content we write-up.
Some parts of this article are sourced from:
thehackernews.com


 US Imprisons Dark Web Moderator
US Imprisons Dark Web Moderator