Elementor, a WordPress site builder plugin with above five million energetic installations, has been located to be susceptible to an authenticated distant code execution flaw that could be abused to get in excess of impacted internet sites.
Plugin Vulnerabilities, which disclosed the flaw previous week, said the bug was launched in version 3.6. that was produced on March 22, 2022. Roughly 37% of end users of the plugin are on variation 3.6.x.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“That means that destructive code provided by the attacker can be run by the web site,” the scientists reported. “In this occasion, it is feasible that the vulnerability might be exploitable by an individual not logged in to WordPress, but it can conveniently be exploited by any individual logged in to WordPress who has obtain to the WordPress admin dashboard.”
In a nutshell, the issue relates to a situation of arbitrary file add to influenced web-sites, possibly foremost to code execution.
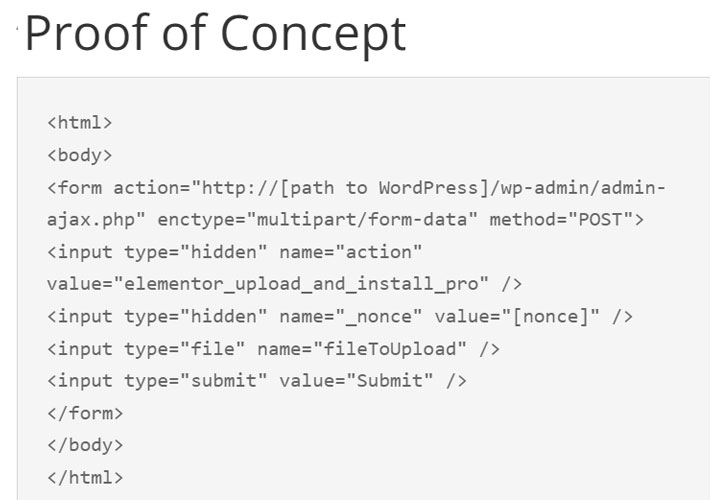
The bug has been dealt with in the most recent model of Elementor, with Patchstack noting that “this vulnerability could enable any authenticated person, irrespective of their authorization, to transform the website title, internet site emblem, modify the theme to Elementor’s topic, and worst of all, upload arbitrary documents to the web-site.”

The disclosure comes a lot more than two months right after Important Addons for Elementor was located to have a critical vulnerability that could result in the execution of arbitrary code on compromised internet websites.
Discovered this report attention-grabbing? Observe THN on Facebook, Twitter and LinkedIn to browse much more special content we article.
Some elements of this post are sourced from:
thehackernews.com


 Lazarus Group Behind $540 Million Axie Infinity Crypto Hack and Attacks on Chemical Sector
Lazarus Group Behind $540 Million Axie Infinity Crypto Hack and Attacks on Chemical Sector