A cyberespionage group with suspected ties to the Kazakh and Lebanese governments has unleashed a new wave of attacks from a multitude of industries with a retooled edition of a 13-calendar year-old backdoor Trojan.
Check Position Analysis termed out hackers affiliated with a group named Dark Caracal in a new report released yesterday for their initiatives to deploy “dozens of digitally signed variants” of the Bandook Windows Trojan about the previous year, consequently at the time once again “reigniting curiosity in this aged malware spouse and children.”
The unique verticals singled out by the menace actor include government, economical, power, meals field, healthcare, instruction, IT, and authorized institutions situated in Chile, Cyprus, Germany, Indonesia, Italy, Singapore, Switzerland, Turkey, and the US.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The unusually substantial wide range of qualified marketplaces and areas “reinforces a prior hypothesis that the malware is not developed in-house and utilised by a single entity, but is element of an offensive infrastructure offered by a 3rd party to governments and risk actors throughout the world, to facilitate offensive cyber functions,” the scientists stated.
Dark Caracal’s substantial use of Bandook RAT to execute espionage on a world scale was to start with documented by the Electronic Frontier Foundation (EFF) and Lookout in early 2018, with the group attributed to the theft of enterprise mental residence and individually identifiable information and facts from hundreds of victims spanning above 21 countries.
The prolific team, which has operated at minimum considering the fact that 2012, has been connected to the Lebanese General Directorate of Basic Security (GDGS), deeming it a country-point out degree sophisticated persistent menace.
The concurrent use of the same malware infrastructure by different teams for seemingly unrelated strategies led the EFF and Lookout to surmise that the APT actor “possibly uses or manages the infrastructure discovered to be hosting a variety of popular, global cyberespionage strategies.”
Now the identical team is back at it with a new strain of Bandook, with additional efforts to thwart detection and investigation, for each Test Stage Investigation.
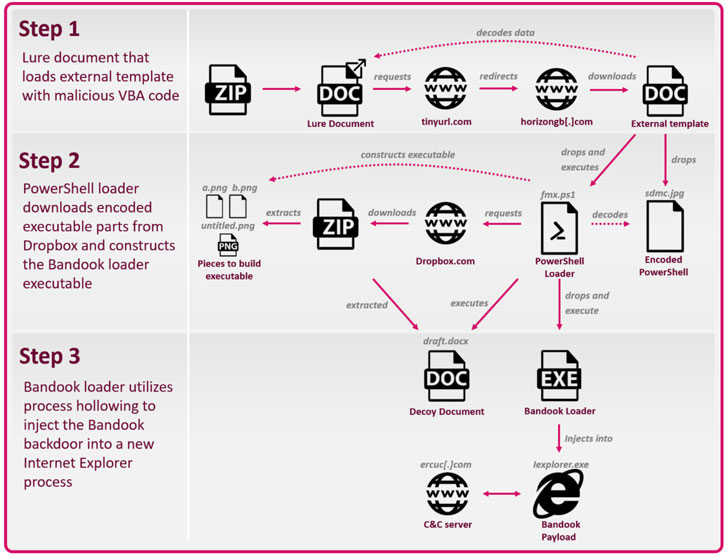
A 3-Stage An infection Chain
The an infection chain is a three-phase system that begins with a lure Microsoft Phrase document (e.g. “Qualified paperwork.docx”) sent within a ZIP file that, when opened, downloads destructive macros, which subsequently proceeds to fall and execute a 2nd-phase PowerShell script encrypted inside of the primary Word document.
In the last stage of the attack, this PowerShell script is applied to down load encoded executable areas from cloud storage companies like Dropbox or Bitbucket in purchase to assemble the Bandook loader, which then will take the accountability of injecting the RAT into a new Internet Explorer process.
The Bandook RAT — commercially out there setting up in 2007 — arrives with all the abilities generally connected with backdoors in that it establishes get hold of with a remotely-controlled server to obtain further instructions ranging from capturing screenshots to carrying out numerous file-linked operations.
But according to the cybersecurity firm, the new variant of Bandook is a slimmed-down edition of the malware with guidance for only 11 instructions, although prior variations were being recognized to characteristic as many as 120 commands, suggesting the operators’ need to minimize the malware’s footprint and evade detection in opposition to substantial-profile targets.
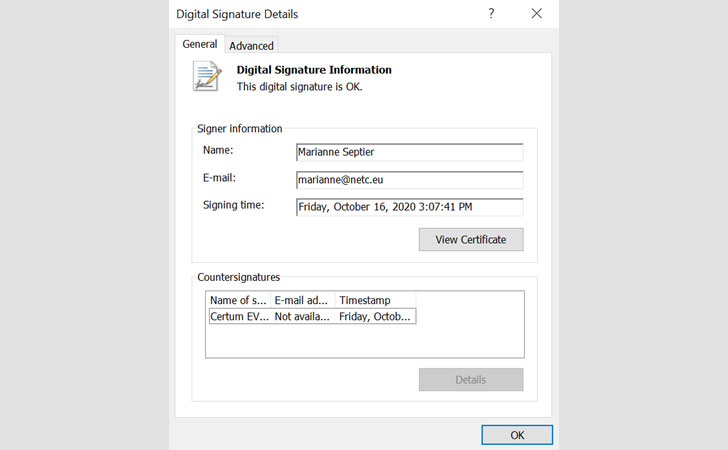
That is not all. Not only valid certificates issued by Certum were being employed to signal this trimmed model of the malware executable, Check Issue researchers uncovered two far more samples — comprehensive-fledged digitally-signed and unsigned variants — which they believe are operated and marketed by a one entity.
“Though not as able, nor as practiced in operational security like some other offensive security providers, the team driving the infrastructure in these attacks would seem to improve in excess of time, incorporating various layers of security, valid certificates and other procedures, to hinder detection and evaluation of its operations,” the researchers concluded.
Identified this short article fascinating? Comply with THN on Facebook, Twitter and LinkedIn to study much more unique articles we publish.
Some pieces of this post are sourced from:
thehackernews.com


 #DTX Cybersecurity Mini Summit: How CISOs Can Transform an Organizations’ Cyber-Capabilities
#DTX Cybersecurity Mini Summit: How CISOs Can Transform an Organizations’ Cyber-Capabilities