The cybersecurity planet is continually evolving to new sorts of threats and vulnerabilities. But ransomware proves to be a distinctive animal—most damaging, persistent, notoriously challenging to stop, and is demonstrating no symptoms of slowing down.
Falling target to a ransomware attack can cause significant information loss, data breach, operational downtime, costly restoration, lawful implications, and reputational hurt.
In this story, we have lined everything you need to have to know about ransomware and how it performs.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
What is ransomware?
Ransomware is a malicious application that gains manage around the infected unit, encrypts documents, and blocks consumer accessibility to the information or a method right until a sum of revenue, or ransom, is paid out.
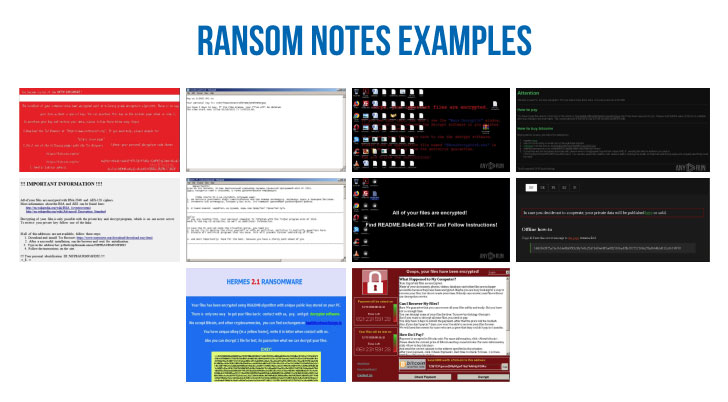
Crooks’ scheme contains a ransom note—with quantity and instructions on how to shell out a ransom in return for the decryption key—or direct communication with the sufferer.
When ransomware impacts corporations and establishments of each and every size and kind, attackers often focus on healthcare, education and learning, IT, govt, and finance sectors with deeper pockets—causing damages ranging from hundreds of thousands and thousands to billions of pounds.
Ransomware attacks began selecting up in 2012, and due to the fact then, it has become the most pervasive cyber-attacks throughout the planet.
For instance, HelloKitty ransomware hit Polish online video game developer CD Projekt Crimson final week with fairly a well-known tactic, i.e., attackers threatened the organization to leak the source code of online games, together with Cyberpunk 2077, Witcher 3, Gwent, and along with private files in the business.
And it’s truly happened! Following CD Projekt announced that they would not be paying the ransom, attackers produced an auction for the stolen knowledge on a hacker forum.
And it isn’t the only instance. Ransomware has usually been a person of the most popular forms of destructive samples uploaded in malware analysis sandbox ANY.Run. In excess of 124,00 interactive classes with ransomware were analyzed on-line only in 2020.
From a locker to the enterprise
One particular of the ways to protect from attacks is recognition. We imagine it is a need to for enterprise executives and workforce to have an understanding of this form of danger.
In this posting, we’ll choose a seem at the background of ransomware:
The initial ransomware
The very first recognised ransomware attack was carried out in 1989 by an AIDS researcher, Joseph Popp, who distributed malicious 20,000 floppy disks to AIDS scientists spanning extra than 90 nations, saying that the disks contained a survey method. Considering the fact that then, the ransomware threat has advanced a ton and obtained far more features.
Locker ransomware
In 2007, Locker ransomware, a new classification of ransomware malware, appeared that does not encrypt files alternatively, it locks the victim out of their device, avoiding them from employing it.
Identical to this, WinLock demanded a $10 ransom for the unlocking code. Later on, Citadel, Lyposit, and Reveton worm managed a display screen with a good concept from a pretend regulation enforcement agency.
This usually can take the sort of locking the computer’s or device’s consumer interface and then inquiring the person to pay out a cost to restore entry to it.
Scareware
In afterwards years, attackers changed their technique to capitalize on anxiety by spreading faking applications and antivirus (AV) applications. The attack involves a pop-up information shown to victims stating that their computer systems have been infected with viruses. It lures victims to a web page exactly where they’re questioned for money to pay for software program to take care of the difficulty. All the things seemed dependable: logos, colour schemes, and other copyrighted materials.
From that moment, criminals understood that it was significantly less difficult to compromise several internet sites, focus on phishing, and get the full course of action automated.
Crypto ransomware
In 2013, CryptoLocker emerged as the initially cryptographic malware that typically comes as an email attachment. The Gameover ZeuS botnet was dependable for these attacks. CryptoLocker encrypts data files, and soon after that, a bitcoin payment was essential to unlock them.
If the ransom was not been given in 3 times, the ransom doubled. CryptorBit, CryptoDefense, CryptoWall, WannaCry enlarged decoy variations and even utilized technique weaknesses to infect personal computers.
The hottest action in that evolution is the arrival of ransomware-as-a-support, which to start with appeared in 2015 with the Tox toolkit launch. It gave would-be cybercriminals the solution to produce tailor made ransomware instruments with highly developed evasion abilities.
Company ransomware
Ransomware attackers leveled up and went to the company stage. They chosen to offer with huge organizations and scare them of a feasible outbreak.
For illustration, a target obtained an email with a menace of dispersed denial-of-company (DDoS) attack. To avoid it, victims desired to spend a ransom.
A single additional situation is the data compromise ransom. A criminal threatens a target to exploit compromised facts to the community until a ransom is compensated. The pursuing tactic is helpful on the organization level, as companies do not want to set their standing at stake.
Now it really is distinct that malware will go on to evolve. And probably it will purchase hybrid attacks, together with other malware family members.
Attack in details
As we now know the heritage and styles of ransomware, now it can be time to recognize how it works.
- Deployment: In the initial stage, attackers distribute important factors made use of to infect, encrypt, or lock the system, downloaded with out the user’s awareness, applying phishing, or following exploiting focused process flaws.
- Set up: When the payload is downloaded, the upcoming move is infection. The malware drops a small file that is typically able of protection evasion. The ransomware executes and attempts to obtain persistence on the contaminated process by putting by itself to autorun the registry keys, making it possible for distant attackers to handle the method.
- Command-and-Control: The malware then connects to the attackers’ command and control (C2) server to acquire guidance and, generally, to deposit the uneven personal encryption key out of the victim’s achieve.
- Destruction: As soon as data files get encrypted, the malware deletes first copies on the process, and the only way to restore them is to decrypt encoded information.
- Extortion: Here occur ransom notes. The victim receives to know that his info is compromised. The payment array varies in accordance to the type of focus on. To confuse and scare a victim, attackers may well delete various information from the pc. However, if a user pays the ransom, it is not a guarantee that the facts will be restored or ransomware by itself will be deleted.
Popular family members and operators
Many types of malware are famed in the ransomware entire world. Let’s search by way of them and communicate about well-liked operators that stand out in malware history:
1) GandCrab ransomware is a single of the most infamous ransomware releases in the past few yrs that amassed just about $2 billion in payments from its victims.
Believed to be a product of a Russian hacker team, GandCrab was found in 2018 as a part of Ransomware-as-a-Assistance (RaaS) bought to other cybercriminals.
Although GandCrab introduced “retirement” in 2019, some researchers claim that it returned with a new pressure, termed Sodinokibi, with a identical codebase. Sodinokibi targets Microsoft Windows devices and encrypts all information apart from configuration files.
2) Subsequent, Maze ransomware, which designed headlines in the past two a long time, is regarded for releasing stolen information to the general public if the victim does not pay out to decrypt it.
It was the initially ransomware attack that put together knowledge encryption with info theft. Furthermore, they threatened to make the info general public if the ransom was not paid out. When the COVID-19 started off, Maze announced that they would depart hospitals by yourself. But afterwards, they broke that guarantee as effectively.
In 2020 Maze announced they shut down its functions. But it’s much more likely that they just moved to another malware.
3) Netwalker utilised method hollowing and code obfuscation to target corporate victims. But in January 2021, legislation enforcement agencies teamed up against Netwalker and took over domains in a dark web used by malware actors.
4) Wannacry spreads autonomously from computer system to personal computer making use of EternalBlue, an exploit supposedly developed by the NSA and then stolen by hackers.
It is the most uploaded type of ransomware in ANY.Operate services in 2020. It strike leading malware with 1930 duties. You can look into them in the community submission library, research by the “wannacry” tag.
5) Avaddon’s malspam typically incorporates the only smiley to entice people into downloading the attachment. The malware also checks the user’s locale prior to infecting. If it is Russian or Cherokee, Avaddon would not encrypt methods.
6) Babuk is a new malware targeting enterprises in 2021. Babuk comprises secure encryption that helps make it unattainable to restore files for absolutely free.
Targets of ransomware attacks
There are a number of factors attackers first pick what form of organizations they want to target with ransomware:
- Simple to evade protection. Universities, small companies that have modest security groups are an uncomplicated concentrate on. File sharing and an considerable databases make the penetration straightforward for attackers.
- Possibility of a fast payment. Some corporations are pressured to pay back a ransom quickly. Federal government agencies or clinical services often will need fast obtain to their data. Law companies and other companies with sensitive knowledge generally want to keep a compromise a secret.
And some ransomware spreads immediately, and anyone can turn out to be its victim.
The Quick Progress of Ransomware
The main reason why this sort of malware has grow to be successful is the attacks that bring success to cybercriminals. Markets enable crooks obtain innovative ransomware for producing money.
Malware authors present many means to pack the ransomware. Malicious software program encrypts systems quickly and stealthily. As shortly as the ransom is acquired, it is no obstacle to protect the tracks. These points lead to a major increase.
Now criminals go bald and expect to get hundreds or 1000’s of pounds as organizations you should not want to risk info reduction and outages.
Ransomware distribution approaches
Listed here are many strategies of how ransomware spreads:
- Email (spam)
- Watering Gap attack
- Malvertising
- Exploit kits
- USB and removable media
- Ransomware as a company
- Zero days
Ransomware analysis in ANY.Operate
Let’s examine a sample of ransomware alongside one another.
Below is a job with Sodinokibi malware. Many thanks to ANY.Run interactivity, we can adhere to the user’s path:
Very first of all, we wait around for the malicious software to finish file-encrypting on the disc. The distinguishable aspect of Sodinokibi is the desktop wallpaper with text.
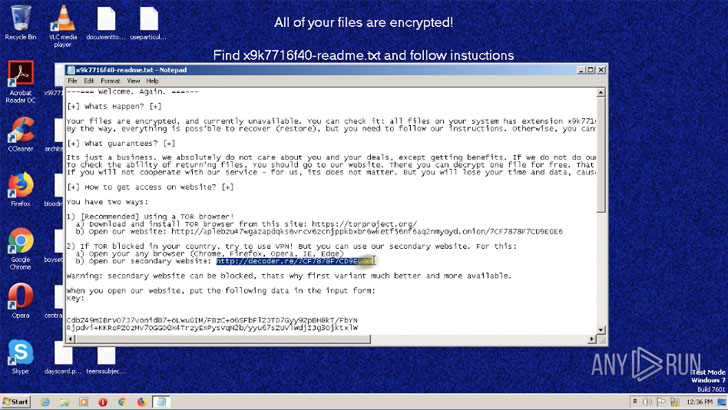
Then we open up a text file on the desktop. Sure, we can interact with information and folders in the digital Device during the job execution.
There we can see instructions with the URL address. We can copy it and open it in the browser. On the new site, we will need to enter the vital each critical is distinctive for every single infected Machine.
There is ours in the text file so that we can enter it. And then a website page with the sum of the ransom payment appears and a countdown. Lastly, we open up the file with an graphic for take a look at decryption and open up it.
Avoidance measures
2021 began with arrests of ransomware gangs. The Egregor hacker group has been taken down by French and Ukrainian police past week.
That is a very good tendency that legislation enforcement businesses preserve defeating malware actors. Even so, we have to have to be careful and try to halt attacks, far too.
To shield from ransomware, companies should have an elaborate plan from malware, such as backup facts. Considering the fact that ransomware is very difficult to detect and struggle, various defense mechanisms really should be made use of.
ANY.Operate is a person of them that aids to identify malware early and avoid infections. Apart from that, the most vital safety is the education of team. They need to have to prevent any suspicious inbound links or data files. Workers who know that ransomware exists and how it performs can detect these types of attacks.
Uncovered this report attention-grabbing? Follow THN on Facebook, Twitter and LinkedIn to browse additional exceptional written content we write-up.
Some components of this post are sourced from:
thehackernews.com

 Legal Firm Leaks 15,000 Cases Via the Cloud
Legal Firm Leaks 15,000 Cases Via the Cloud