Two lengthy-working surveillance campaigns have been located concentrating on the Uyghur local community in China and in other places with Android spyware resources created to harvest delicate info and keep track of their whereabouts.
This encompasses a previously undocumented malware strain referred to as BadBazaar and up to date variants of an espionage artifact dubbed MOONSHINE by researchers from the College of Toronto’s Citizen Lab in September 2019.
“Mobile surveillance tools like BadBazaar and MOONSHINE can be applied to track lots of of the ‘pre-criminal’ activities, steps viewed as indicative of religious extremism or separatism by the authorities in Xinjiang,” Lookout said in a detailed create-up of the operations.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
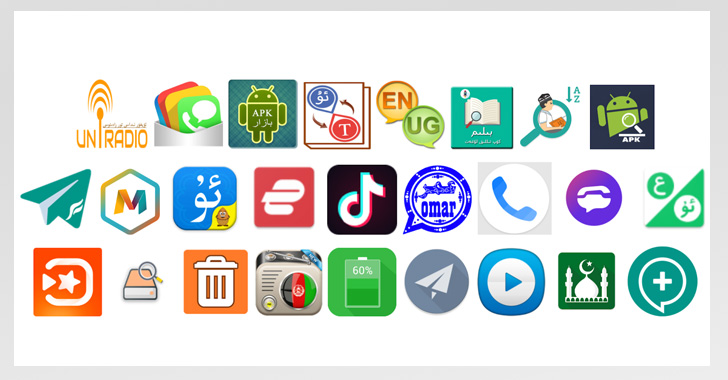
The BadBazaar marketing campaign, according to the security firm, is said to date as considerably back as late 2018 and comprise 111 special applications that masquerade as benign movie gamers, messengers, religious applications, and even TikTok.
When these samples have been dispersed by means of Uyghur-language social media platforms and interaction channels, Lookout observed it observed a dictionary application named “Uyghur Lughat” on the Apple Application Store that communicates with a server used by its Android counterpart to assemble standard iPhone information and facts.
The iOS app carries on to be readily available on the App Keep.
“Given that BadBazaar variants usually get their surveillance capabilities by downloading updates from their [command-and-control server], it is attainable the menace actor is hoping to afterwards update the iOS sample with equivalent surveillance functionality,” the researchers pointed out.
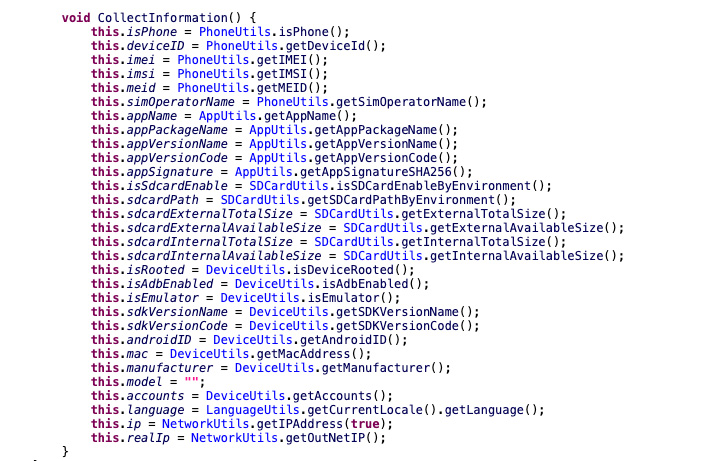
BadBazaar, after put in, arrives with various functions that make it possible for it to gather call logs, GPS places, SMS messages, and documents of interest record phone phone calls take pics and exfiltrate substantial product metadata.
Even more evaluation of BadBazaar’s infrastructure has disclosed overlaps with a different adware operation aimed at the ethnic minority that arrived to light-weight in July 2020 and which designed use of an Android toolset termed DoubleAgent.
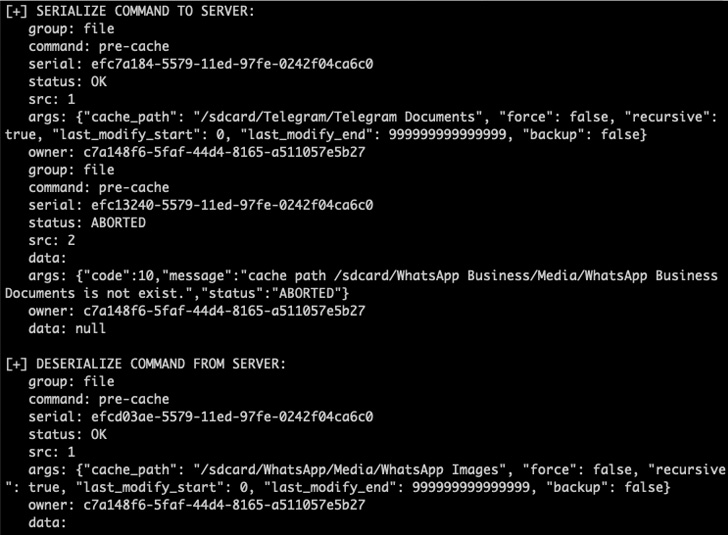
Attacks using MOONSHINE, in a related vein, have used above 50 malicious apps because July 2022 that are engineered to amass personal knowledge from the contaminated devices, in addition to recording audio and downloading arbitrary files.
“The the vast majority of these samples are trojanized versions of preferred social media platforms, like WhatsApp or Telegram, or trojanized variations of Muslim cultural applications, Uyghur-language applications, or prayer apps,” the scientists explained.
Prior destructive cyber pursuits leveraging the MOONSHINE Android spyware package have been attributed to a danger actor tracked as POISON CARP (aka Evil Eye or Earth Empusa), a China-dependent nation-condition collective known for its attacks from Uyghurs.
The conclusions arrive a little around a month immediately after Look at Position disclosed aspects of an additional extended-standing surveillanceware procedure aimed at the Turkic Muslim neighborhood that deployed a trojan named MobileOrder because at least 2015.

“BadBazaar and these new variants of MOONSHINE add to the previously extensive selection of one of a kind surveillanceware used in strategies to surveil and subsequently detain people in China,” Lookout said.
“The broad distribution of both equally BadBazaar and MOONSHINE, and the level at which new operation has been released show that progress of these families is ongoing and that there is a ongoing need for these instruments.”
The improvement also follows a report from Google Task Zero previous 7 days, which uncovered evidence of an unnamed business surveillance vendor weaponizing 3 zero-working day security flaws in Samsung telephones with an Exynos chip running kernel model 4.14.113. The security holes had been plugged by Samsung in March 2021.
That mentioned, the research huge mentioned the exploitation mirrored a pattern equivalent to the latest compromises wherever malicious Android applications were being abused to goal consumers in Italy and Kazakhstan with an implant referred to as Hermit, which has been joined to Italian enterprise RCS Lab.
Located this posting exciting? Follow THN on Fb, Twitter and LinkedIn to read through much more unique articles we article.
Some parts of this short article are sourced from:
thehackernews.com

 #IRISSCON: Social Engineering Testers Warned Not to Cross Ethical and Legal Boundaries
#IRISSCON: Social Engineering Testers Warned Not to Cross Ethical and Legal Boundaries