The Apache Application Foundation has unveiled fixes to include an actively exploited zero-working day vulnerability influencing the extensively-employed Apache Log4j Java-based mostly logging library that could be weaponized to execute destructive code and make it possible for a full takeover of vulnerable systems.
Tracked as CVE-2021-44228 and by the monikers Log4Shell or LogJam, the issue concerns a circumstance of unauthenticated, remote code execution (RCE) on any application that works by using the open up-supply utility and impacts versions Log4j 2.-beta9 up to 2.14.1. The bug has scored a fantastic 10 on 10 in the CVSS ranking technique, indicative of the severity of the issue.
“An attacker who can handle log messages or log message parameters can execute arbitrary code loaded from LDAP servers when information lookup substitution is enabled,” the Apache Foundation explained in an advisory. “From Log4j 2.15., this habits has been disabled by default.”

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

Log4j is applied as a logging deal in a wide range of distinct common computer software by a range of companies, together with Amazon, Apple iCloud, Cisco, Cloudflare, ElasticSearch, Crimson Hat, Steam, Tesla, Twitter, and online video game titles this kind of as Minecraft. In the scenario of the latter, attackers have been equipped to gain RCE on Minecraft Servers by only pasting a specially crafted message into the chat box.
Exploitation can be attained by a single string of textual content, which can induce an software to achieve out to a malicious exterior host if it is logged by means of the vulnerable instance of Log4j, efficiently granting the adversary the capacity to retrieve a payload from a remote server and execute it regionally. The job maintainers credited Chen Zhaojun of Alibaba Cloud Security Group with identifying the issue.
A substantial attack surface
“The Apache Log4j zero-day vulnerability is in all probability the most critical vulnerability we have found this 12 months,” reported Bharat Jogi, senior manager of vulnerabilities and signatures at Qualys. “Log4j is a ubiquitous library utilised by tens of millions of Java apps for logging error messages. This vulnerability is trivial to exploit.”
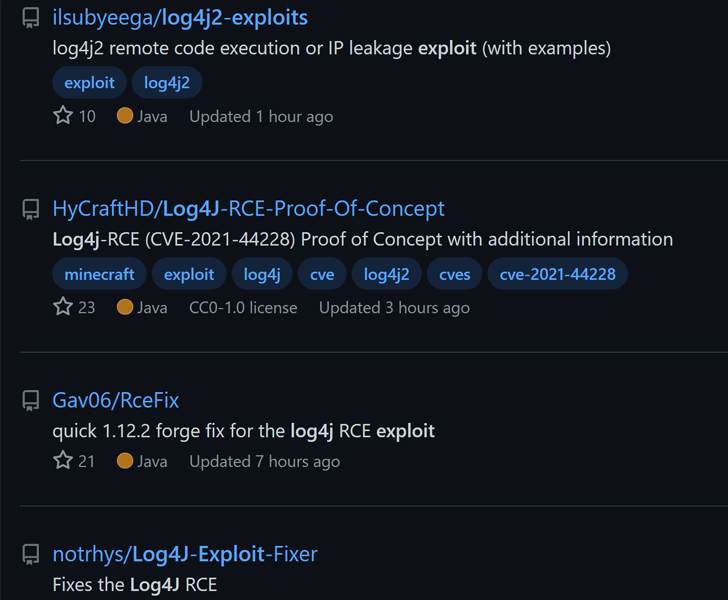
Cybersecurity companies BitDefender, Cisco Talos, Huntress Labs, and Sonatype have all verified evidence of mass scanning of influenced purposes in the wild for susceptible servers and attacks registered in opposition to their honeypot networks adhering to the availability of a proof-of-idea (PoC) exploit. “This is a low experienced attack that is particularly easy to execute,” Sonatype’s Ilkka Turunen explained.

GreyNoise, likening the flaw to Shellshock, claimed it observed malicious activity targeting the vulnerability commencing on December 9, 2021. Web infrastructure organization Cloudflare pointed out that it blocked about 20,000 exploit requests per minute close to 6:00 p.m. UTC on Friday, with most of the exploitation makes an attempt originating from Canada, the U.S., Netherlands, France, and the U.K.
Specified the simplicity of exploitation and prevalence of Log4j in company IT and DevOps, in-the-wild attacks aimed at susceptible servers are expected to ramp up in the coming days, creating it crucial to deal with the flaw instantly. Israeli cybersecurity organization Cybereason has also released a resolve called “Logout4Shell” that closes out the shortcoming by applying the vulnerability by itself to reconfigure the logger and reduce further exploitation of the attack.
“This Log4j (CVE-2021-44228) vulnerability is really bad. Millions of apps use Log4j for logging, and all the attacker requires to do is get the app to log a specific string,” Security skilled Marcus Hutchins stated in a tweet.
Uncovered this posting interesting? Stick to THN on Fb, Twitter and LinkedIn to go through a lot more special information we submit.
Some areas of this posting are sourced from:
thehackernews.com


 Cyber-attack on Hellmann Worldwide Logistics
Cyber-attack on Hellmann Worldwide Logistics