Ever considering the fact that any person had trigger to use a personal computer, passwords have been the mainstay of safe obtain to resources. It turns out, having said that, that passwords are not as secure as we at the time assumed.
They can be guessed or cracked simply, saved insecurely, and traded on line by nefarious cyber criminals. This means the globe is inevitably relocating in direction of applying multifactor authentication (MFA) as a much more protected usually means of authenticating your identification and accessing your critical facts.
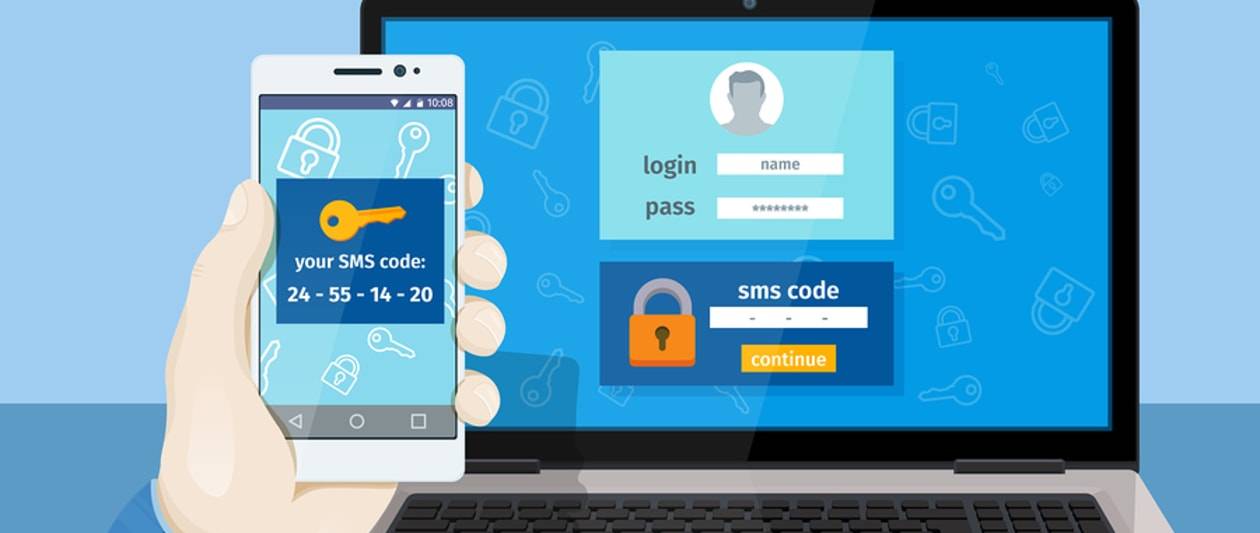
MFA adds an more action to the authentication system. In addition to what a consumer appreciates, this kind of as their username and password, MFA pairs this method with an action this could be a code despatched through an SMS concept or email, or a token sent via an authentication app.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
It truly is turning into considerably a lot more commonplace these times. If you’ve tried to entry your bank account information on the net, or have acquired anything from an on the internet retailer, you will most likely get an SMS despatched to your phone with a code you have to have to input just before you can continue more, in order to accessibility your account.
So, with MFA fast turning into commonplace, and for fantastic cause, it can be now expected to meet up with compliance demands in some industries. What really should you look at when choosing an MFA alternative? There are five components to contemplate.
Versatility: Does the MFA resolution utilize only the required sum of security dependent on what risk is posed by who’s accessing the sources? Also, does the resolution provide adaptable methods of authenticating buyers? Will it offer you hardware tokens, this sort of as a USB-primarily based dongle, or application tokens, this sort of as smartphone app to NFC to text information and thrust notification? Does it make it possible for buyers to use biometrics, these as fingerprint scans or facial recognition?
Prices: There’s a price tag to implementing MFA, which are down to what choice your organisation chooses to implement. Components tokens, for illustration, have deployment and recurring charges, these as server infrastructure, staffing, seller aid, and hardware generation and distribution. There are also charges concerned with software program tokens, though these tend to have fewer deployment fees, and implementation can be obtained in weeks.
Security: When employing an MFA, there are various degrees of security that can be utilised. Passwords and PINs are much less safe than hardware tokens or a FIDO authenticator, which can be applied when an organisation wants phishing-resistant authentication that can roam involving devices. A person-time codes provide large security when users really don’t have a committed authentication app, in the meantime. Press notifications, as well, can be a great selection if your customers can use a cell authentication app. Biometric authentication, finally, is good for technique logins or precise apps.
Scalability: Any MFA implementation your organisation opts for demands to be scalable so it can be deployed across your whole organisation, and acquire as the small business grows. This signifies security techniques really should be reliable across the organisation. Deployment need to deal with all finish-consumers, whether they are in the office environment or doing work remotely. MFA must also protect cloud and on-premises apps, VPN, server logins, and privilege elevation.
Simplicity of use: MFA must not only be quick to roll out, but must be straightforward to use. Some customers may perhaps be minimal in what they have as a further factor to log into means, these as missing a smartphone or being unable to use a hardware token. Organisations need to stability usability with value and security to increase acceptance.
Some sections of this article are sourced from:
www.itpro.co.uk

 Spider-Man Fans Warned About Scams Leveraging New Movie
Spider-Man Fans Warned About Scams Leveraging New Movie