Gigaset has disclosed a malware infection found in its Android units was the result of a compromise of a server belonging to an external update company service provider.
Impacting older smartphone designs — GS100, GS160, GS170, GS180, GS270 (additionally), and GS370 (in addition) series — the malware took the variety of numerous unwanted applications that have been downloaded and mounted by way of a pre-set up technique update app.
The infections are mentioned to have happened starting off March 27.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The German company of telecommunications equipment reported it took ways to inform the update services service provider of the issue, subsequent which more infections ended up prevented on April 7.
“Actions have been taken to immediately rid contaminated gadgets of the malware. In get for this to occur the devices need to be connected to the internet (WLAN, WiFi or cell data). We also endorse connecting the equipment to their chargers. Impacted products must automatically be freed from the malware inside 8 several hours,” the firm said in a assertion shared with The Hacker News.
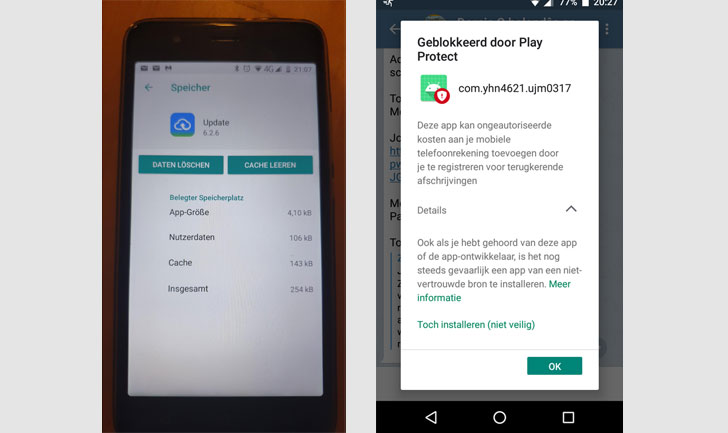
The total checklist of malware applications mounted on the devices consist of —
- Gem
- Intelligent
- Xiaoan
- asenf
- Tayase
- com.yhn4621.ujm0317
- com.wagd.smarter
- com.wagd.xiaoan
Alternatively, Gigaset has also urged consumers to look at for signs of any infection by checking out the Settings application and manually uninstall the applications in problem, in addition to putting in all software program updates that may perhaps be available for the device.
Versions GS160, GS170, and GS180 jogging all variations of the application, GS100 (up to model GS100_HW1._XXX_V19), GS270 (up to variation GIG_GS270_S138), GS270 as well as (up to version GIG_GS270_furthermore_S139), GS370 (up to model GIG_GS370_S128), and GS370 furthermore (up to edition GIG_GS370_moreover_S128) are impacted.
As earlier mentioned, Gigaset units GS110, GS185, GS190, GS195, GS195LS, GS280, GS290, GX290, GX290additionally, GX290 PRO, GS3, and GS4 series are not impacted by this incident.
Discovered this post interesting? Adhere to THN on Facebook, Twitter and LinkedIn to read through additional distinctive material we article.
Some pieces of this posting are sourced from:
thehackernews.com


 Digital artists meet scam artists, as criminals pounce on NFT craze
Digital artists meet scam artists, as criminals pounce on NFT craze