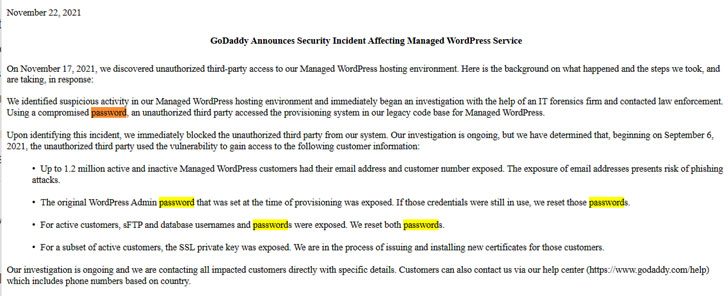
Web hosting large GoDaddy on Monday disclosed a data breach that resulted in the unauthorized entry of data belonging to a whole of 1.2 million energetic and inactive customers, generating it the 3rd security incident to arrive to light-weight given that 2018.
In a submitting with the U.S. Securities and Exchange Commission (SEC), the world’s premier domain registrar claimed that a malicious third-party managed to obtain obtain to its Managed WordPress hosting surroundings on September 6 with the enable of a compromised password, working with it to attain sensitive data pertaining to its consumers. It can be not instantly very clear if the compromised password was secured with two-factor authentication.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The Arizona-based mostly corporation claims over 20 million customers, with additional than 82 million domain names registered utilizing its services.
GoDaddy exposed it identified the crack-in on November 17. An investigation into the incident is ongoing and the enterprise claimed it is really “calling all impacted consumers specifically with certain facts.” The subsequent info is believed to have been accessed by the intruder —
- Email addresses and consumer numbers of up to 1.2 million energetic and inactive Managed WordPress customers
- Authentic WordPress Admin password that was set at the time of provisioning was uncovered
- sFTP and database usernames and passwords affiliated with its energetic prospects, and
- SSL private keys for a subset of energetic clients
GoDaddy explained it’s in the course of action of issuing and putting in new certificates for the impacted customers. As a precautionary evaluate, the business also said it has reset the afflicted passwords and it really is bolstering its provisioning program with added security protections.

According to Wordfence CEO Mark Maunder, “GoDaddy saved sFTP passwords in such a way that the plaintext variations of the passwords could be retrieved, instead than storing salted hashes of these passwords, or furnishing community important authentication, which are both of those business best tactics.”
Whilst info breaches are no extended a sporadic occurrence, the exposure of email addresses and passwords provides risk of phishing attacks, not to point out help the attackers to breach the vulnerable WordPress sites to add malware and entry other individually identifiable data stored in them.
“On internet sites wherever the SSL non-public crucial was uncovered, it could be achievable for an attacker to decrypt visitors utilizing the stolen SSL personal key, supplied they could efficiently perform a gentleman-in-the-center (MITM) attack that intercepts encrypted visitors amongst a web page customer and an afflicted site,” Maunder said.
Discovered this short article interesting? Observe THN on Fb, Twitter and LinkedIn to browse more exclusive information we publish.
Some parts of this posting are sourced from:
thehackernews.com

 Cisco Flaw Affects Firewalls
Cisco Flaw Affects Firewalls