Cybersecurity scientists on Tuesday disclosed information of a innovative campaign that deploys destructive backdoors for the goal of exfiltrating facts from a quantity of industry sectors located in Japan.
Dubbed “A41APT” by Kaspersky scientists, the findings delve into a new slew of attacks undertaken by APT10 (aka Stone Panda or Cicada) applying earlier undocumented malware to supply as lots of as a few payloads these kinds of as SodaMaster, P8RAT, and FYAnti.
The extended-functioning intelligence-collecting operation initially arrived into the scene in March 2019, with activities spotted as lately as November 2020, when experiences emerged of Japan-linked businesses staying focused by the risk actor in in excess of 17 regions around the globe.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The fresh new attacks uncovered by Kaspersky are reported to have occurred in January 2021. The an infection chain leverages a multi-stage attack method, with the original intrusion taking place via abuse of SSL-VPN by exploiting unpatched vulnerabilities or stolen qualifications.
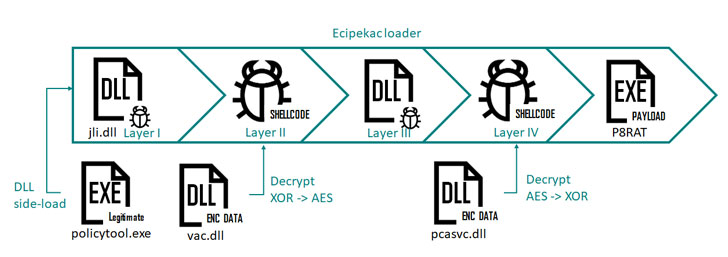
Heart to the campaign is a malware named Ecipekac (“Cake piece” in reverse, but with a typo) that traverses a four-layer “sophisticated loading schema” by producing use of 4 information to “load and decrypt 4 fileless loader modules a single after the other to sooner or later load the ultimate payload in memory.”
Even though the most important function of P8RAT and SodaMaster is to obtain and execute payloads retrieved from an attacker-managed server, Kaspersky’s investigation hasn’t yielded any clues as to the exact malware delivered on goal Windows programs.
Interestingly, the 3rd payload, FYAnti, is a multi-layer loader module in alone that goes by way of two extra successive layers to deploy a ultimate-phase distant accessibility Trojan recognized as QuasarRAT (or xRAT).
“The functions and implants of the marketing campaign … are remarkably stealthy, creating it tricky to track the danger actor’s pursuits,” Kaspersky researcher Suguru Ishimaru said. “The principal stealth features are the fileless implants, obfuscation, anti-VM ,and elimination of exercise tracks.”
Identified this posting attention-grabbing? Follow THN on Facebook, Twitter and LinkedIn to go through extra distinctive articles we write-up.
Some sections of this write-up are sourced from:
thehackernews.com


 NHS Reduces Cyber-Skills Shortages but Breach Problems Remain
NHS Reduces Cyber-Skills Shortages but Breach Problems Remain