Risk actors are exploiting ProxyLogon and ProxyShell exploits in unpatched Microsoft Trade Servers as section of an ongoing spam marketing campaign that leverages stolen email chains to bypass security software package and deploy malware on vulnerable programs.
The findings arrive from Trend Micro subsequent an investigation into a quantity of intrusions in the Middle East that culminated in the distribution of a under no circumstances-ahead of-found loader dubbed SQUIRRELWAFFLE. Very first publicly documented by Cisco Talos, the attacks are thought to have commenced in mid-September 2021 by using laced Microsoft Office documents.
“It is recognized for sending its destructive emails as replies to pre-current email chains, a tactic that lowers a victim’s guard from malicious actions,” scientists Mohamed Fahmy, Sherif Magdy, Abdelrhman Sharshar stated in a report posted previous 7 days. “To be capable to pull this off, we consider it associated the use of a chain of each ProxyLogon and ProxyShell exploits.”

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

ProxyLogon and ProxyShell refer to a collection of flaws in Microsoft Trade Servers that could enable a danger actor to elevate privileges and remotely execute arbitrary code, properly granting the capability to consider management of the susceptible equipment. Although the ProxyLogon flaws ended up dealt with in March, the ProxyShell bugs were being patched in a collection of updates produced in May well and July.
Craze Micro explained it observed the use of community exploits for CVE-2021-26855 (ProxyLogon), CVE-2021-34473, and CVE-2021-34523 (ProxyShell) on a few of the Exchange servers that had been compromised in distinctive intrusions, working with the entry to hijack authentic email threads and mail destructive spam messages as replies, therefore escalating the probability that unsuspecting recipients will open up the e-mail.
“Providing the destructive spam making use of this method to reach all the inside domain consumers will decrease the risk of detecting or stopping the attack, as the mail getaways will not be able to filter or quarantine any of these internal e-mail,” the scientists stated, including the attackers at the rear of the operation did not have out lateral movement or set up more malware so as to remain underneath the radar and prevent triggering any alerts.

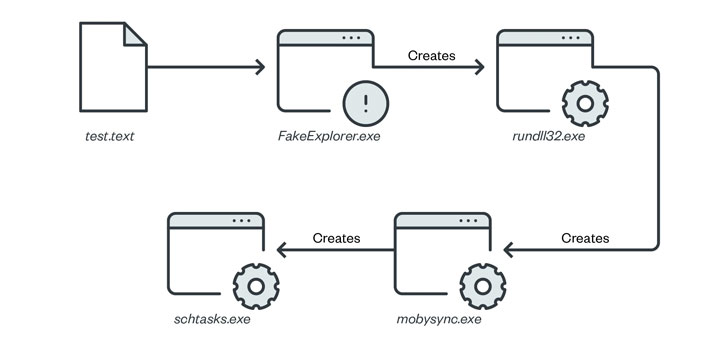
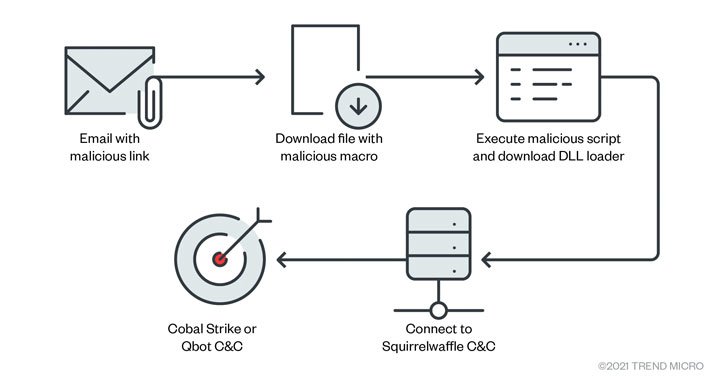
The attack chain involves rogue email messages containing a hyperlink that, when clicked, drops a Microsoft Excel or Phrase file. Opening the doc, in transform, prompts the recipient to enable macros, in the long run top to the obtain and execution of the SQUIRRELWAFFLE malware loader, which acts as a medium to fetch last-phase payloads these types of as Cobalt Strike and Qbot.
“SQUIRRELWAFFLE campaigns ought to make people wary of the distinct ways utilized to mask malicious email messages and documents,” the scientists concluded. “Email messages that come from dependable contacts may not be enough of an indicator that whichever website link or file involved in the email is safe.”
Found this report intriguing? Stick to THN on Facebook, Twitter and LinkedIn to read far more exclusive information we publish.
Some components of this post are sourced from:
thehackernews.com

 Hackers Exploit ProxyLogon and ProxyShell Bugs in Phishing Blitz
Hackers Exploit ProxyLogon and ProxyShell Bugs in Phishing Blitz