Although it is a norm for phishing campaigns that distribute weaponized Microsoft Business files to prompt victims to enable macros in purchase to bring about the an infection chain in the background, new findings show that macro security warnings can be disabled totally without the need of requiring any consumer conversation.
In still one more instance of malware authors continue to evolve their approaches to evade detection, scientists from McAfee Labs stumbled on a novel tactic that “downloads and executes destructive DLLs (ZLoader) with out any destructive code current in the original spammed attachment macro.”


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
ZLoader infections propagated working with this mechanism have been primarily noted in the U.S., Canada, Spain, Japan, and Malaysia, McAfee famous. The malware — a descendant of the infamous ZeuS banking trojan — is well acknowledged for aggressively employing macro-enabled Office documents as an first attack vector to steal credentials and individually identifiable data from end users of targeted economic establishments.
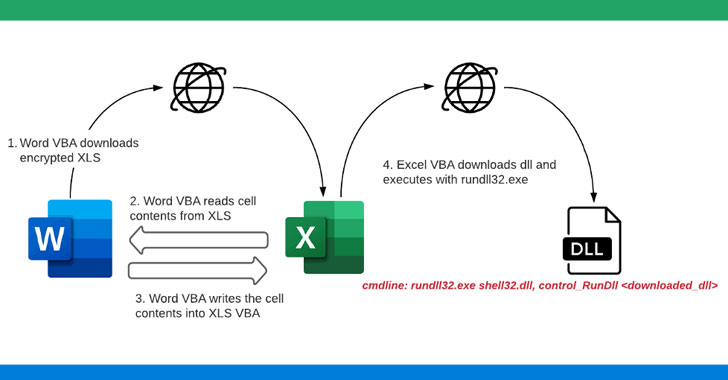
In investigating the intrusions, the scientists observed that the an infection chain started out with a phishing email containing a Microsoft Term document attachment that, when opened, downloaded a password-guarded Microsoft Excel file from a remote server.
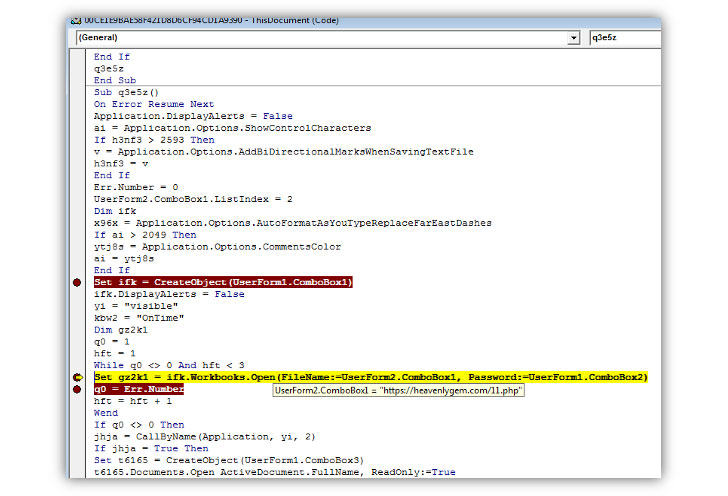
“Soon after downloading the XLS file, the Word VBA reads the mobile contents from XLS and produces a new macro for the similar XLS file and writes the cell contents to XLS VBA macros as features,” the researchers reported. “The moment the macros are prepared and all set, the Phrase doc sets the coverage in the registry to ‘Disable Excel Macro Warning’ and invokes the destructive macro function from the Excel file. The Excel file now downloads the Zloader payload. The Zloader payload is then executed working with rundll32.exe.”

Supplied the “substantial security risk” posed by macros, the aspect is ordinarily disabled by default, thus prompting danger actors to screen a convincing lure to trick victims into enabling them. By turning off the security warning presented to the consumer, the attacks are noteworthy because of the steps it takes to thwart detection and remain under the radar.
“Destructive files have been an entry place for most malware people and these attacks have been evolving their an infection tactics and obfuscation, not just limiting to immediate downloads of payload from VBA, but creating brokers dynamically to obtain payloads,” the researchers said. “Use of these types of agents in the infection chain is not only restricted to Phrase or Excel, but even more threats may use other dwelling off the land applications to down load its payloads.”
Observed this article exciting? Follow THN on Fb, Twitter and LinkedIn to read far more unique written content we put up.
Some elements of this posting are sourced from:
thehackernews.com

 Proposed law seeks to boost federal cyber workforce through apprenticeships, training
Proposed law seeks to boost federal cyber workforce through apprenticeships, training