Threat actors are abusing Microsoft Establish Engine (MSBuild) to filelessly produce remote entry trojans and password-thieving malware on specific Windows programs.
The actively ongoing campaign is said to have emerged previous thirty day period, scientists from cybersecurity firm Anomali reported on Thursday, including the malicious construct files arrived embedded with encoded executables and shellcode that deploy backdoors, allowing for the adversaries to get handle of the victims’ machines and steal sensitive details.
MSBuild is an open up-supply develop instrument for .NET and Visual Studio developed by Microsoft that permits for compiling source code, packaging, tests, deploying apps.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

In making use of MSBuild to filelessly compromise a equipment, the concept is to stay less than the radar and thwart detection, as this sort of malware can make use of a reputable software to load the attack code into memory, thereby leaving no traces of infection on the method and supplying attackers a significant degree of stealth.
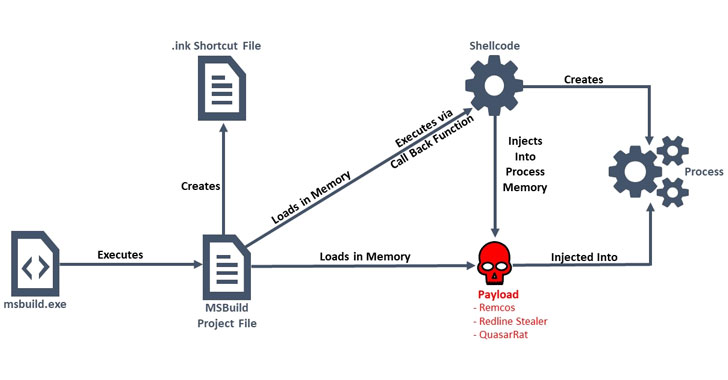
As of composing, only two security distributors flag a person of the MSBuild .proj files (“vwnfmo.lnk”) as destructive, even though a second sample (“72214c84e2.proj”) uploaded to VirusTotal on April 18 remains undetected by each and every anti-malware motor. The the greater part of the samples analyzed by Anomali were located to provide the Remcos RAT, with a couple others also delivering the Quasar RAT and RedLine Stealer.
Remcos (aka Remote Control and Surveillance software package), after mounted, grants entire accessibility to the distant adversary, its attributes ranging from capturing keystrokes to executing arbitrary commands and recording microphones and webcams, when Quasar is an open-source .NET-based RAT able of keylogging, password stealing, among the other people. Redline Stealer, as the title indicates, is a commodity malware that harvests qualifications from browsers, VPNs, and messaging shoppers, in addition to thieving passwords and wallets associated with cryptocurrency apps.
“The menace actors at the rear of this marketing campaign used fileless delivery as a way to bypass security steps, and this procedure is made use of by actors for a wide range of targets and motivations,” Anomali scientists Tara Gould and Gage Mele stated. “This campaign highlights that reliance on antivirus software package by itself is insufficient for cyber protection, and the use of respectable code to disguise malware from antivirus technology is successful and growing exponentially.”
Identified this post exciting? Stick to THN on Facebook, Twitter and LinkedIn to browse extra distinctive written content we article.
Some components of this short article are sourced from:
thehackernews.com

 Cisco to acquire threat intelligence provider Kenna Security
Cisco to acquire threat intelligence provider Kenna Security