Microsoft on Wednesday shared extra specifics about the strategies, techniques, and processes (TTPs) adopted by the attackers at the rear of the SolarWinds hack to stay below the radar and stay clear of detection, as cybersecurity firms get the job done in the direction of finding a “clearer picture” of one particular of the most complex attacks in new record.
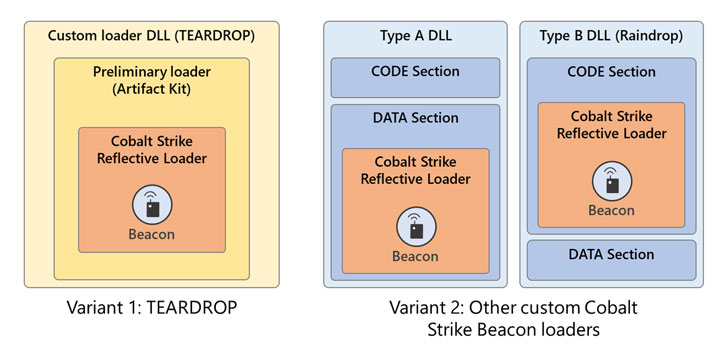
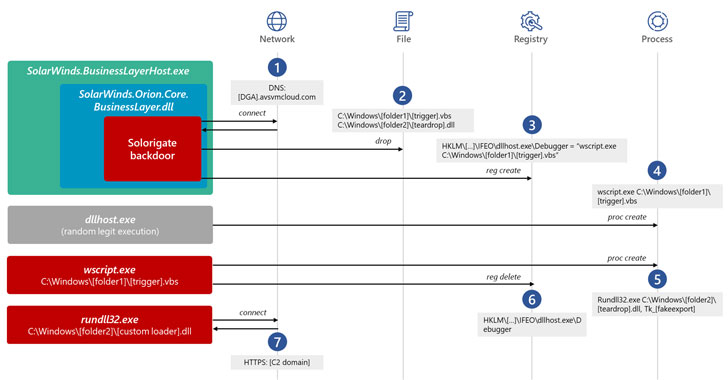
Calling the threat actor “skillful and methodic operators who follow functions security (OpSec) ideal techniques,” the enterprise said the attackers went out of their way to assure that the initial backdoor (Sunburst aka Solorigate) and the submit-compromise implants (Teardrop and Raindrop) are separated as significantly as possible so as to hinder attempts to place their malicious activity.
“The attackers guiding Solorigate are proficient marketing campaign operators who thoroughly planned and executed the attack, remaining elusive although preserving persistence,” scientists from Microsoft 365 Defender Investigate Workforce, Microsoft Risk Intelligence Center (MSTIC), and Microsoft Cyber Defense Functions Heart (CDOC) claimed.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Though the precise identity of the team tracked as StellarParticle (CrowdStrike), UNC2452 (FireEye), SolarStorm (Palo Alto Unit 42), and Dark Halo (Volexity) remain unidentified as still, the U.S. government before this month formally tied the espionage marketing campaign to a group most likely of Russian origin.
A Selection of Strategies to Stay Undetected
Microsoft’s timeline of the attacks demonstrates that the thoroughly-useful Sunburst DLL backdoor was compiled and deployed on to SolarWinds’ Orion system on February 20, adhering to which it was dispersed in the variety of tampered updates sometime in late March.
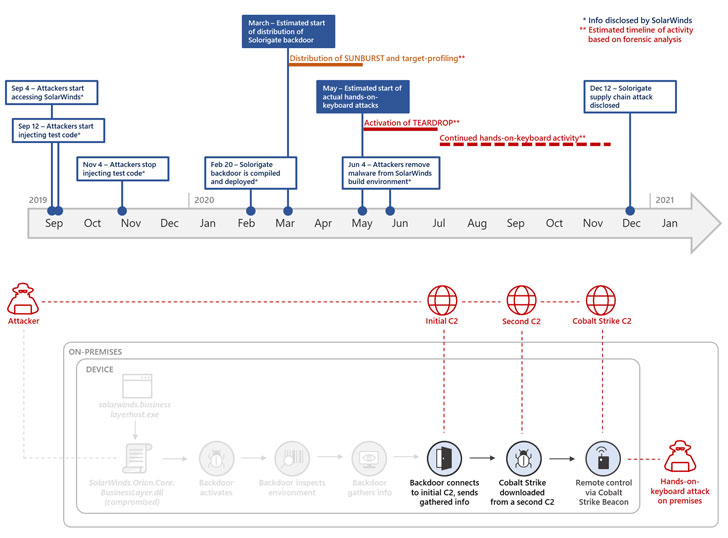
An just about two-month-extended reconnaissance time period to profile its targets — one thing that calls for a stealthy persistence to continue to be undetected and acquire valuable facts — in the long run paved the way for the deployment of Cobalt Strike implants on picked target networks in Could and the elimination of Sunburst from SolarWinds develop surroundings on June 4.
But solutions as to how and when the transition from Sunburst to Raindrop happens has yielded tiny definitive clues, even if it appears that the attackers deliberately separated the Cobalt Strike loader’s execution from the SolarWinds method as an OpSec evaluate.
The strategy is that in the function the Cobalt Strike implants were being uncovered on goal networks, it wouldn’t reveal the compromised SolarWinds binary and the source chain attack that led to its deployment in the initial place.
The results also make it very clear that, although the hackers relied on an array of attack vectors, the trojanized SolarWinds computer software shaped the main of the espionage operation:
- Methodic avoidance of shared indicators for each and every compromised host by deploying personalized Cobalt Strike DLL implants on every program
- Camouflaging destructive applications and binaries to mimic present data files and plans by now current on the compromised equipment
- Disabling party logging employing AUDITPOL ahead of arms-on keyboard action and enabling it again the moment full
- Generating special firewall guidelines to lower outgoing packets for specified protocols right before jogging noisy network enumeration pursuits that were later on taken off following the network survey
- Executing lateral movement routines only right after disabling security products and services on targeted hosts
- Allegedly working with timestomping to adjust artifacts’ timestamps and leveraging wiping treatments and tools to stop discovery of destructive DLL implants
Adopting a Zero Trust Mentality
“This attack was at the same time advanced and standard,” Microsoft reported. “The actor demonstrated sophistication in the breadth of practices utilized to penetrate, expand throughout, and persist in affected infrastructure, but numerous of the methods, techniques, and procedures (TTPs) had been separately regular.”
To safeguard in opposition to these types of attacks in the potential, the business endorses that businesses adopt a “zero believe in mentality” to obtain the minimum privileged access and decrease hazards by enabling multi-factor authentication.
“With Solorigate, the attackers took advantage of wide part assignments, permissions that exceeded role needs, and in some circumstances deserted accounts and applications which really should have had no permissions at all,” Alex Weinert, Microsoft’s director of id security, said.
Identified this post intriguing? Abide by THN on Facebook, Twitter and LinkedIn to go through more special information we put up.
Some areas of this write-up are sourced from:
thehackernews.com

 Google Chrome makes it easier to fix weak passwords
Google Chrome makes it easier to fix weak passwords