In advance of searching malware, each researcher needs to come across a program the place to examine it. There are quite a few techniques to do it: establish your very own natural environment or use third-party answers. Today we will stroll through all the ways of producing a personalized malware sandbox in which you can execute a proper examination with out infecting your laptop or computer. And then assess it with a all set-built provider.
Why do you require a malware sandbox?
A sandbox lets detecting cyber threats and analyzing them properly. All details continues to be protected, and a suspicious file can not access the method. You can monitor malware procedures, discover their patterns and look into conduct.
Before setting up a sandbox, you must have a apparent intention of what you want to accomplish by way of the lab.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
There are two strategies how to manage your operating house for evaluation:
- Personalized sandbox. Produced from scratch by an analyst on their very own, especially for their requires.
- A turnkey remedy. A versatile services with a range of configurations to meet your demands.
How to make your own malware sandbox?
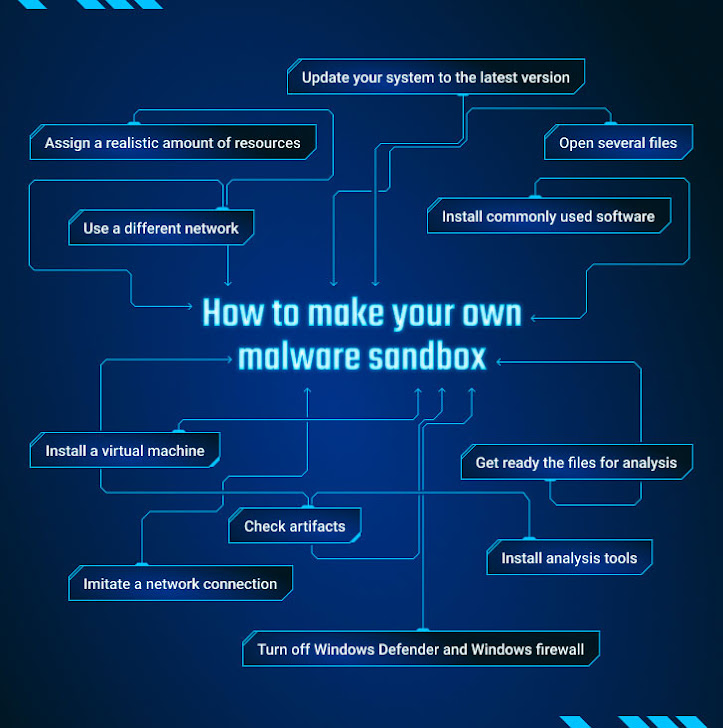
How to make your personal malware sandbox
Let’s stroll by way of all techniques that you want to set up the simple atmosphere for malware investigation:
1 — Set up a digital machine
Jogging malware really should take place in a adequately isolated atmosphere to keep away from infection of a host functioning method. It truly is far better to have an isolated computer, but you can established up a digital equipment or fairly a few of them with distinct variations of OSs. There are a bunch of VMs introduced in the market: VMWare, VirtualBox, KVM, Oracle VM VirtualBox, Microsoft Hyper-V, Parallels, or Xen.
2 — Verify artifacts
Modern malware is good – it understands no matter if it truly is operate on the virtual device or not. That is why it is really essential to get rid of artifacts. Verify code, get rid of detection, and other individuals.
3 — Use a different network
An additional precaution is to use a distinctive network process. Protecting against any infection of other computer systems on your network is critical. Get a VPN support and established it up effectively. You won’t be able to allow the targeted traffic leak transpire from a real IP deal with.
4 — Assign a real looking quantity of methods
Our target is to make a process glimpse as reliable as doable to trick any malicious system into executing. Make positive that you assign a practical quantity of sources: far more than 4 Gb of RAM, a minimal of 4 cores, and disk space of 100 Gb and far more. That is a primary need to pretend as a legit procedure. And continue to, preserve in head that malware checks the configuration of products. If there is a digital machine’s identify somewhere, a malicious item identifies it and stops functioning.
5 — Put in typically applied software program
If you put in Windows and depart it as is, a destructive object will get that it is analyzed.
Set up a couple of applications, like Word, browsers, and other applications that all customers usually have.
6 — Open up quite a few documents
Below we require to demonstrate that it is a authentic personal computer that belongs to another person. Open up a number of paperwork to accumulate logs and a couple of temp information. A number of styles of viruses test this. You can use Regshot or System check to make logs of registry and file program adjustments. Observe that these courses can be detected by malware when it is managing.
7 — Imitate a network connection
Some kinds of malware verify if it can link to web-sites like Google. How to trick a destructive program into imagining that it’s on the internet? Utilities like INetSim and the FakeNet instrument imitate a true Internet connection and make it possible for us to intercept the requests that malware is earning. Try to test network protocols between a malicious item and its host server. But beforehand, uncover out what the analyzed sample is connecting with working with WireShark. And it can take some effort and hard work not to give up this device to the malware, be mindful.
8 — Set up examination applications
Prepare the resources you may use for examination and guarantee that you know how to use them. You can go with Flare VM resources or make use of these packages:
- Debuggers: x64dbg investigates malicious code by executing it.
- Disassemblers: Ghidra would make reverse engineering much easier, with entry to the decompiler’s output. It also can be employed as a debugger.
- Targeted visitors analyzers: Wireshark checks network conversation that malware requests.
- File analyzers: Method Keep an eye on, ProcDOT purpose to watch and fully grasp how processes deal with information.
- Process monitors: Process Explorer, Method Hacker aid to view malware actions.
9 — Update your procedure to the most recent version
Your process should really be up-to-date as properly as all program. Filter out the regular Windows improvements that are happening pretty frequently. On the other hand, your experiment may well involve a diverse edition, these types of as how malware exploits some OS problems. In this state of affairs, decide on and get the vital version set up.
10 — Change off Windows Defender and Windows firewall.
Disable items like Windows defender. If you are functioning with malware, it can trip the antivirus.
11 — Get all set the information for assessment
Generate a shared folder, select a listing you require.
Established up a snapshot to roll again to the later on state of the VM in case of an error.
If you complete all these methods, you might be very good to go and commence the assessment.
Is there a extra successful solution to assess malware?
All these actions just take a whole lot of time and preparation. And even now, there is a possibility that your sandbox will not be protected adequate, invisible for malware, and offer the vital information and facts. So, what is a far better resolution? Here comes the next possibility – use a ready-built alternative. Let us take a glimpse at ANY.Run.
ANY.Run is an on-line malware sandbox that you can use for detection, checking, and examining threats. The finest element of it is time and convenience:
It is really however can be customizable – decide on an operating process, software set, localization, and other information for your uses. But the perk is that you don’t want to put in just about anything! Just take your computer system, and you are all established.
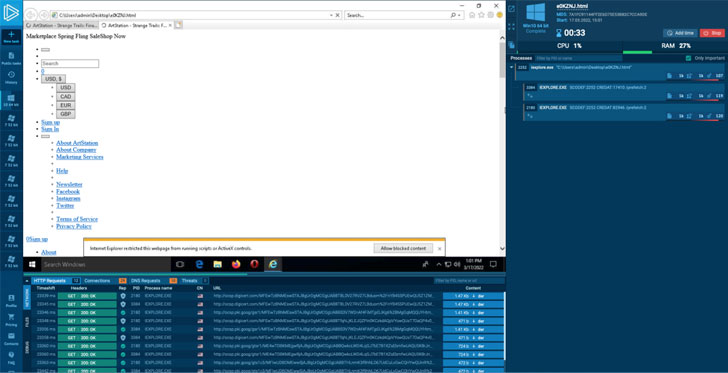
Two minutes is ordinarily more than enough to crack even an sophisticated malware, and most modern anti-evasion methods really don’t get the job done listed here. ANY.Run hunts them all.
Get pleasure from a more quickly alternative
The most effective encounter is your individual, that is why we give you to test the sandbox by on your own and check out the capabilities of ANY.Operate. And here is a specific offer you for our visitors – you can try the company for cost-free:
Compose the “HACKERNEWS” promo code in the email topic at [email protected] and get 14 times of ANY.Run quality subscription for totally free!
Of course, it’s up to you how to conduct malware assessment. You can spend some time creating your have digital surroundings or accomplish examination in various minutes using a convenient sandbox like ANY.Run. The selection is yours. The most essential point is what you will do with these providers and how to realize your objectives there. But that’s yet another story. Effective searching!
Identified this post fascinating? Follow THN on Facebook, Twitter and LinkedIn to browse much more special material we submit.
Some sections of this short article are sourced from:
thehackernews.com


 Tax-Season Scammers Spoof Fintechs Stash, Public
Tax-Season Scammers Spoof Fintechs Stash, Public