A well known Togolese human rights defender has been targeted with spyware by a threat actor recognised for placing victims in South Asia, marking the hacking group’s initially foray into electronic surveillance in Africa.
Amnesty Worldwide tied the covert attack marketing campaign to a collective tracked as “Donot Team” (aka APT-C-35), which has been joined to cyber offensives in India and Pakistan, though also figuring out clear evidence linking the group’s infrastructure to an Indian company termed Innefu Labs. The unnamed activist is believed to have qualified over a period of time of two months beginning in December 2019 with the aid of bogus Android applications and adware-loaded email messages.
“The persistent attacks around WhatsApp and email attempted to trick the sufferer into installing a destructive software that masqueraded as a protected chat application,” Amnesty Intercontinental explained in a report released very last 7 days. “The software was in actuality a piece of customized Android spyware built to extract some of the most sensitive and own data stored on the activist’s phone.”

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

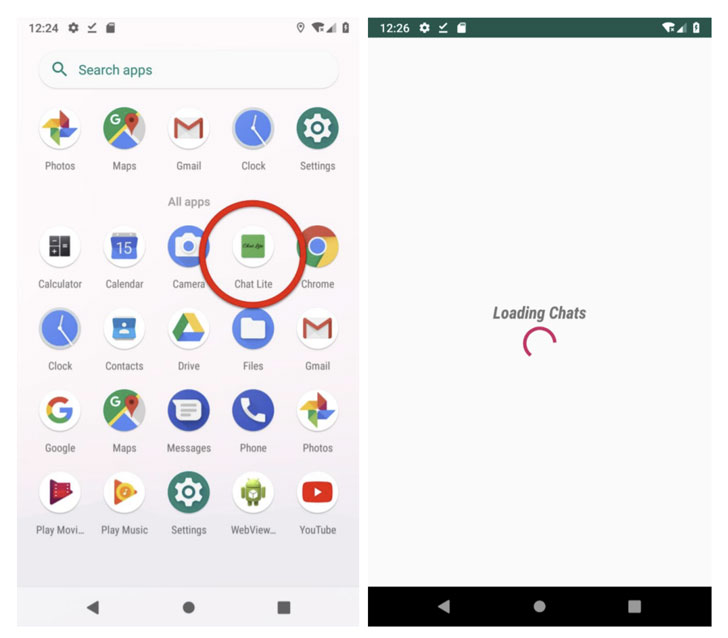
The messages originated from a WhatsApp account related with an Indian phone number that’s registered in the point out of Jammu and Kashmir. At the time set up, the destructive application — which usually takes the variety of an app named “ChatLite” — grants the adversary permissions to entry the camera and microphone, get pics and documents saved on the unit, and even get WhatsApp messages as they are getting sent and acquired.
But when the aforementioned endeavor failed, the attackers switched to an alternate an infection chain in which an email despatched from a Gmail account contained a malware-laced Microsoft Phrase doc that leveraged a now-patched remote code execution vulnerability (CVE-2017-0199) to fall a entire-fledged Windows spying software identified as the YTY framework that grants finish access to the victim’s machine.
“The spyware can be utilized to steal data files from the infected laptop and any related USB drives, document keystrokes, take standard screenshots of the computer system, and obtain added adware elements,” the scientists reported.
Despite the fact that Innefu Labs has not been immediately implicated in the incident, Amnesty Global said it uncovered a domain (“server.authshieldserver.com”) that pointed to an IP tackle (122.160.158[.]3) utilised by a Delhi- based mostly firm named Innefu Labs. In a assertion shared with the non-governmental corporation, Innefu Labs denied any connection to the Donot Staff APT, adding “they are not informed of any use of their IP handle for the alleged pursuits.”

We have achieved out to the organization for further more comment, and we will update the story if we listen to back.
“The stressing craze of private firms actively carrying out unlawful digital surveillance increases the scope for abuse while lessening avenues for domestic authorized redress, regulation, and judicial control,” Amnesty mentioned. “The nature of cross-border business cyber surveillance in which the surveillance targets, the operators, the conclusion shopper, and the attack infrastructure can all be located in diverse jurisdictions results in sizeable impediments to accomplishing remediation and redress for human legal rights abuses.”
Identified this report interesting? Follow THN on Fb, Twitter and LinkedIn to read through additional exclusive articles we write-up.
Some sections of this post are sourced from:
thehackernews.com

 Singapore launches new cyber security framework
Singapore launches new cyber security framework