An Iranian cyberespionage team recognized for targeting governing administration, defense technology, army, and diplomacy sectors is now impersonating journalists to method targets by using LinkedIn and WhatsApp and infect their units with malware.
Detailing the new methods of the “Charming Kitten” APT group, Israeli company Clearsky stated, “starting July 2020, we have identified a new TTP of the group, impersonating ‘Deutsche Welle’ and the ‘Jewish Journal’ employing email messages together with WhatsApp messages as their key platform to method the goal and convince them to open up a malicious backlink.”
This improvement is the very first time the menace actor is claimed to have carried out a watering hole attack by means of WhatsApp and LinkedIn, which also incorporates building phone calls to victims, Clearsky famous in a Thursday assessment.
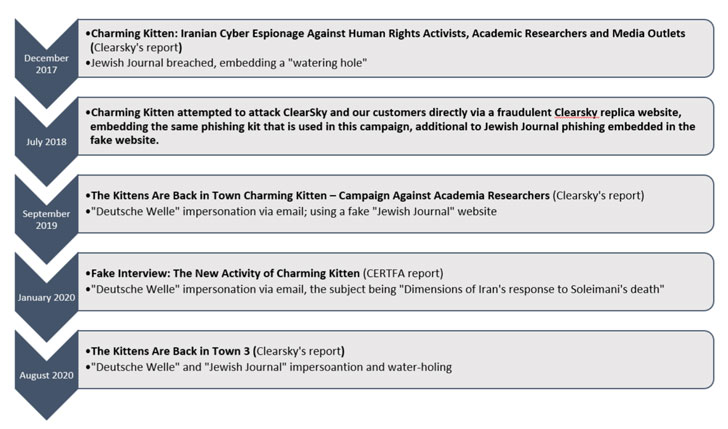
Soon after the business alerted Deutsche Welle about the impersonation and the watering hole in their internet site, the German broadcaster confirmed, “the reporter which Charming Kitten impersonated did not ship any email messages to the target nor any other academic researcher in Israel in the earlier couple of weeks.”Charming Kitten (also recognised by aliases APT35, Parastoo, NewsBeef, and Newscaster) has been formerly connected to a collection of covert campaigns at least given that December 2017 with an intention to steal delicate information from human legal rights activists, educational scientists, and media retailers.
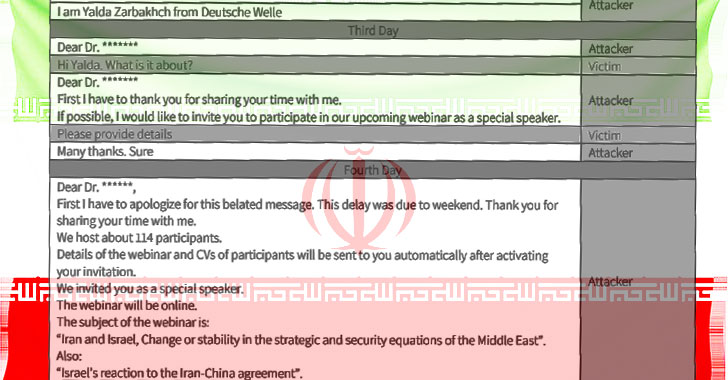
The watering hole — in this circumstance, a destructive backlink embedded in the compromised Deutsche Welle domain — sent the info-stealer malware via WhatsApp, but not in advance of the victims have been first approached via experimented with-and-tested social engineering strategies with an intention to lure the lecturers to speak at an on the web webinar.
“The correspondence started with an email despatched to the focus on, initiating a conversation,” Clearsky stated. “Following a short discussion with the goal, the Charming Kitten attacker requests to transfer the dialogue to WhatsApp. If the concentrate on refuses to shift to WhatsApp, the attacker will ship a information by using a faux LinkedIn profile.”
In just one state of affairs, the adversary even took the step of messaging and calling a sufferer to achieve the target’s rely on and subsequently walk the person by the actions of connecting to the webinar utilizing the malicious connection earlier shared in the chat.
Despite the fact that APT35 may perhaps have picked up a new ruse, this is not the initial time the Iranian hackers have utilized social media channels to spy on staff of desire.
In a three-yr-lengthy “Procedure Newscaster” uncovered by iSIGHT Companions (now owned by FireEye) in 2014, the threat actor was discovered to have created wrong Fb accounts and a bogus news web site to spy on armed service and political leaders in the U.S., Israel, and other international locations.
“In this campaign, we noticed a willingness of the attackers to converse on the phone specifically with the victim, applying WhatsApp calls, and a respectable German phone quantity. This TTP is unusual and jeopardizes the phony identity of the attackers,” Clearsky researchers explained.
Located this posting attention-grabbing? Observe THN on Fb, Twitter and LinkedIn to study more exceptional content we submit.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

 Musk: Tesla Was Target of Russian Ransomware Conspiracy
Musk: Tesla Was Target of Russian Ransomware Conspiracy