The next post is based mostly on a webinar collection on business API security by Imvision, that includes skilled speakers from IBM, Deloitte, Maersk, and Imvision discussing the value of centralizing an organization’s visibility of its APIs as a way to accelerate remediation attempts and strengthen the in general security posture.
Centralizing security is demanding in present day open up ecosystem
When approaching API visibility, the first point we have to understand is that modern enterprises actively avoid controlling all their APIs by 1 method. In accordance to IBM’s Tony Curcio, Director of Integration Engineering, numerous of his organization shoppers by now do the job with hybrid architectures that leverage traditional on-premise infrastructure when adopting SaaS and IaaS across many cloud vendors.
These architectures goal to raise resilience and flexibility, but are effectively knowledgeable that it complicates centralization efforts. In these companies, it is essential to have a centralized API locale with deployment into each of these destinations, to make sure bigger visibility and much better management of API-linked small business things to do.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The challenge for security teams is that there is just not a person central location exactly where all APIs are managed by the development staff – and as time passes, that complexity is very likely to only get worse. Furthermore, this complexity will not stop at the infrastructure degree, but carries on into the application layer.
Deloitte’s Moe Shamim, Senior Technology Government and Deputy CISO of US Consulting, sees non-monolithic application advancement as important. He statements that corporations must now crack down those hundreds of thousands of lines of code into API-dependent, modularized procedures and units in purchase to continue to be aggressive, all when making sure that threat vectors are stored down to a minimal. This involves considerable rethinking as one particular ought to now account for API gateways, IAMs, throttling and far more, which implies considerable time and resources.
The API footprint of corporations is no for a longer time growing organically about time. It now consists of various APIs whose origins occur from mergers and acquisitions, versioning, inner APIs, 3rd party APIs, drift from primary intended usage, dev, exam, debug and diagnostic applications and so on. This would make complexity an even larger issue, as quite a few APIs are undocumented and unmanaged, and pointless to say – unprotected.
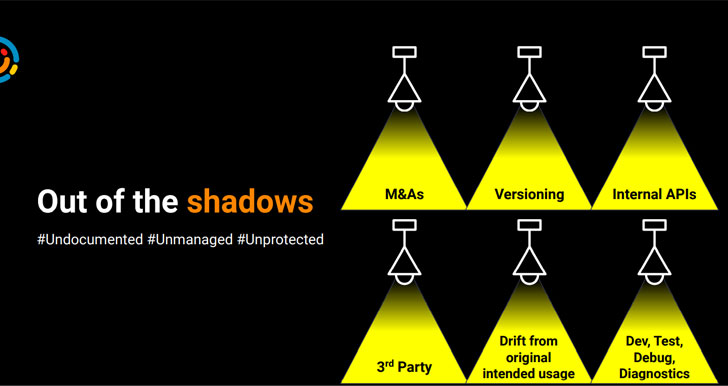 Exactly where do ‘Shadow APIs’ appear from?
Exactly where do ‘Shadow APIs’ appear from?
Enforcing a consistent plan throughout each of the distinct environments exactly where enterprise assets are situated is a obstacle in this hybrid cloud truth. A person must acquire this regularity challenge into consideration when selecting technology stacks, so that imposing procedures and governance applications everywhere you go is not an issue.
But this is less complicated said than done, specifically in effective enterprises that merge with and get other companies: just about every small business makes use of diverse technologies, mandating a custom-made, bespoke API security course of action for each and every new environment which is added.
Here is what you ought to fork out notice to when assessing a entire lifecycle API security resolution
API lifecycle? API way of life!
In accordance to Moe Shamim, the API lifecycle can be boiled down to the pillars observed in the picture below. When fashioning an API security technique, one must get into account architecture, distribution, style and design and a total slew of other factors that effect the way an group develops its strategy to APIs. You can seem at every single of these facets as controls you inject at every phase of the API lifecycle. And it effectively ties back again to visibility and centralization reviewed over.
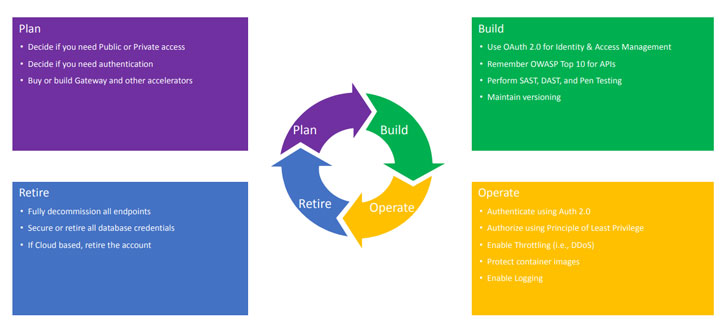 An picture of API lifestyle pillars
An picture of API lifestyle pillars
Arranging determines issues like irrespective of whether APIs will only be utilized within just the network firewall or publicly, as effectively as issues like authentication. It will also contact on more technological issues this kind of as builds, gateway forms and the programming languages that you will use. The essential point–and this goes for each and every conclusion you make concerning your security posture–is to make a alternative that aligns with your ecosystem of tools, and takes your risk modeling into thought.
In the Build pillar, scanning for OWASP Top 10 issues is a need to, and SAST applications are fantastic for that. Pentesting and versioning may perhaps not essentially be integrated into your security posture, but they’re each impressive mechanisms that will undoubtedly advantage your security arsenal.
The Function pillar consists of issues like throttling, caching, and logging. A robust logging and monitoring system is a ought to-have in the remediation period, as it permits you to deal with vulnerabilities from version to edition.
Past but not least, we get there at the Retire pillar of the lifecycle. Taking away endpoints that are no extended in use is an critical best apply generally, if you no for a longer period need to have a assistance – really don’t leave it on. And if you really don’t will need an API at all any more, just choose it offline the identical goes for cloud accounts.
Tony Curcio claims that one of the key tenets in the governance of API courses is coordination amongst the API producers, merchandise administration, and customers. Seeking at the security disposition of each of people personas and coordinating API insurance policies that ensure safe use for each and every is a elementary factor of an organization’s security posture.
Obtaining an API-to start with mentality in the organization certainly assists. At IBM, for case in point, they construct their have API management technology that allows them to expose, secure, and safeguard their APIs much more effortlessly. Possessing superior technology at the rear of you–like Imvison–also goes a prolonged way. Their AI technology aids us fully grasp far more about attack vectors, such as critical issues like its resource.
Having an intelligence-led security response tactic
Gabriel Maties, Senior Remedy Architect at Maersk, provides a different standpoint. With Maersk becoming 3 a long time into an API software and pursuing a critical breach, cybersecurity is taken into account continuously as a way to stay at minimum as great as the attackers, if not better.
Sharing his point of view on observability, Gabriel sees API management as a multi-actor discipline from the pretty beginning simply because it shares assets and exposes them internally. Therefore, just about every and every issue of entry into your program and its supporting mechanisms should be cautiously noticed and monitored centrally.
This centralization is significant due to the fact observability is multidimensional in the feeling that you can find by no means one particular solitary element to keep track of. This calls for a holistic perspective of APIs that permits you to conveniently fully grasp the place APIs are deployed, who owns them, who consumes them, how they are consumed, what usual intake appears like and how every 1 is secured. Centralization also enables you to fully grasp much better what each individual API’s lifecycle appears to be like like, how quite a few versions exist, what knowledge is shared, where by it is stored and who’s applying it.
Centralization is the only way to take care of this sophisticated ecosystem in a way that makes certain greatest reward and minimum amount risk.
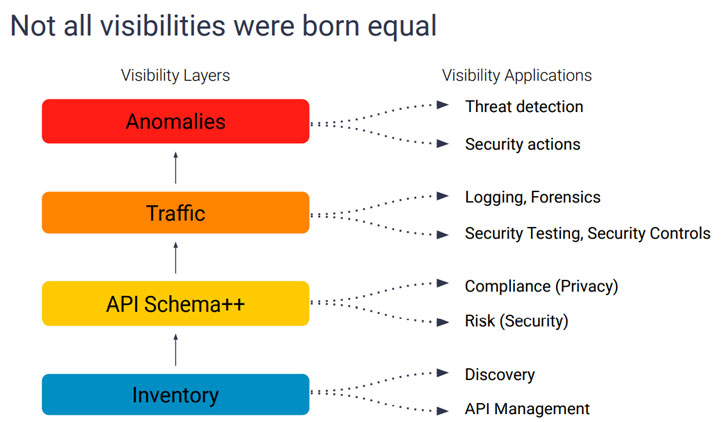 An image of API visibility layers
An image of API visibility layers
Possessing centralized observability further more permits insights, which permits you to get motion on your observations. Observability will allow you to appear at ongoing, active attacks that you might not even know aboutת and even formulate tactics that leverage the actions taken on the insights you draw from your observations.
Rule-based mostly security is extremely helpful, and machine learning and deep finding out are two systems that automate and streamline it. There is only no other alternative as the total of facts to contend with is too much to handle, not to mention that these systems permit adaptive menace safety that allows contend with new threats.
The lousy information is that hackers are also applying these similar technologies, and dealing with that involves significant organizational maturity to just take the steps essential to take care of that. We are speaking about some significant-obligation steps below, like turning off load balancers, switching above firewalls, and other infrastructural modifications finished in an automatic, rapid-fire manner. This are not able to be accomplished without a superior stage of maturity throughout the organization.
Supervised machine learning can enable corporations develop this maturity. It enables you to manage large numbers of rule sets and insights so that you can style automated motion flows. Details science provides important know-how in phrases of tracking distinct attacker behavior, which is critical when there are distinctive sources and superior, persistent threats.
This intelligence-led security reaction empowers a ongoing adaptive, reflexive reaction that leans on quantified evidence when transforming and updating procedures and procedures. This is the only way to deal with the more and more sophisticated attacks we are viewing.
The screens went black: A authentic-everyday living attack tale
Gabriel talked about a serious attack that he experienced when functioning at the Digital Container Shipping and delivery Affiliation (DCSA). A person working day, about nine months following he joined, their screens went blank. Disconnecting and unplugging actions did not assist, it was currently too late and in minutes hundreds of personal computers ended up rendered useless.
This was not an attack for financial incentives, but fairly a damaging just one intended to convey the DCSA to its knees. Gabriel and his team’s only decision was to rebuild, as the attackers applied a person-way encryption. Certainly, though rebuilding the technique, cybersecurity was a major priority. Dynamic assessment was deemed paramount to their attempts so that they could complete authentic-time examination to empower ongoing finding out and danger adaptation. Their goal was to find out what typical and abnormal interior habits looked like, as 80% of attacks are internal.
Adhering to the attack, Gabriel arrived up with 4 stages of observability, well being checks and a way to establish irrespective of whether a system’s wellbeing has been compromised. All processes and architecture selections ended up now compelled by means of cybersecurity evaluation and have to move a selection of checks and balances. This will not imply that all the containers need to be ticked to get a new course of action or final decision permitted, mainly because the major issue in this article is to generate information of your gaps and weaknesses so that you can leverage the appropriate abilities and distributors for your security philosophy.
About the past 2 yrs we have witnessed a escalating pattern of organizations adopting particular API resources that enable check, uncover and unsettle shadow APIs to greater realize their dangers. This is a excellent growth, as APIs are thoroughly distinctive from the software earth we arrived from. The only way to safeguard APIs is to undertake one of a kind applications and processes that ended up designed precisely for them.
API security: Receiving the board onboard
The proliferation and severity of cybersecurity attacks in our landscape are producing the boards and executives of numerous enterprises take more curiosity in API defense. Elevated visibility is another way to get execs to recognize the dangers they are uncovered to. If you can uncover a way to exhibit your execs how a great deal-unprotected details is at risk easily, you’ve won fifty percent the struggle.
This visibility will, in change, empower a additional adaptive, reflexive cybersecurity posture that will enable you to constantly find out, attract insights and modify your posture in reaction to new forms of attacks.
Get this RFP template to aid you simplify the approach of deciding on the ideal API security vendor for your business
Producing a steady, seen security posture throughout all of your organization property is a central tenet to any robust cybersecurity method. This security posture have to consider into account the four pillars of the API lifecycle: Plan, Establish, Function and Retire. To do that accurately, you’ve obtained to opt for the systems that will empower you to implement the procedures, equipment and governance that you resolved upon when starting off out on your API security journey.
Of no much less relevance is establishing a holistic, centralized tactic that empowers the visibility you need to have to secure your belongings. Advanced ML and Deep Discovering technologies shipped by ground breaking providers like Imvision can unquestionably assistance you obtain that.
Identified this report interesting? Follow THN on Facebook, Twitter and LinkedIn to go through extra exclusive content material we write-up.
Some components of this article are sourced from:
thehackernews.com

 Russian Bulletproof Hosting Kingpin Gets Five Years
Russian Bulletproof Hosting Kingpin Gets Five Years