I am sure that several of you have by now read of a a short while ago disclosed critical Windows server vulnerability—called Zerologon—that could enable hackers wholly consider around company networks.
For individuals unaware, in temporary, all supported versions of the Windows Server running systems are vulnerable to a critical privilege escalation bug that resides in the Netlogon Remote Control Protocol for Area Controllers.
In other words, the underlying vulnerability (CVE-2020-1472) could be exploited by an attacker to compromise Active Directory solutions, and eventually, the Windows area with no requiring any authentication.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
What is actually even worse is that a proof-of-idea exploit for this flaw was produced to the community past week, and promptly soon after, attackers started out exploiting the weak spot in opposition to unpatched units in the wild.
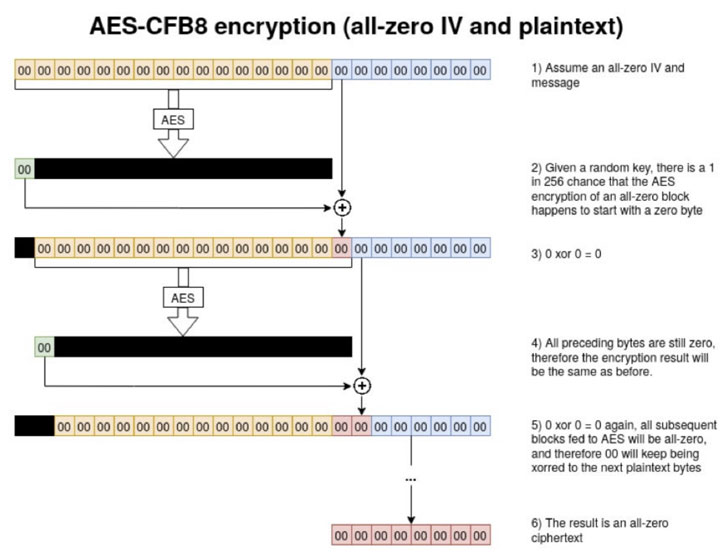
As described in our coverage based on a technological evaluation released by Cynet security scientists, the underlying issue is Microsoft’s implementation of AES-CFB8, in which it unsuccessful to use exceptional, random salts for these Netlogon messages.
The attacker wants to mail a specially crafted string of zeros in Netlogon messages to transform the area controller’s password saved in the Active Directory.
For THN audience keen to discover extra about this menace in detail, which includes complex information and facts, mitigations, and detection methods, they need to be a part of a dwell webinar (sign up here) with Aviad Hasnis, CTO at Cynet.
The no cost cybersecurity educational webinar is scheduled for September 30th at 5:00 PM GMT, and also aims to explore exploits deployed in the wild to just take advantage of this vulnerability.
Moreover this, the Cynet staff has also launched a cost-free detection resource that alerts you to any Zerologon exploitation in your atmosphere.
Sign-up for the live webinar right here.
Observed this article exciting? Comply with THN on Facebook, Twitter and LinkedIn to study more exceptional written content we publish.
Some parts of this article is sourced from:
thehackernews.com


 The Network Perimeter: This Time, It’s Personal
The Network Perimeter: This Time, It’s Personal