The scale of the danger connected with the just lately found Log4Shell vulnerability has been quantified for the initially time, with just about 1 million attack makes an attempt launched in just 72 hours following the critical vulnerability’s disclosure on 9 December.
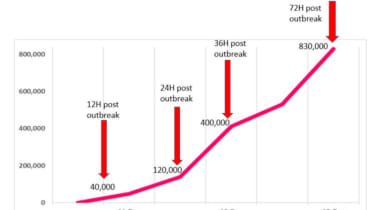
Specialists from Verify Position Research published observations from early vulnerability scans on Tuesday, which revealed makes an attempt to exploit techniques susceptible to Log4Shell improved from 40,000 in the quick 12-hour interval pursuing disclosure, to 830,000 makes an attempt following just 3 times.
Scientists said the vulnerability “is plainly just one of the most significant vulnerabilities on the internet in current a long time, and the potential for destruction is incalculable”. The security community is still scrambling to completely have an understanding of the attack surface for Log4Shell, the RCE vulnerability in the log4j Java logging part revealed very last 7 days.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“The quantity of mixtures of how to exploit it give the attacker many alternate options to bypass recently launched protections,” scientists mentioned. “It suggests that 1 layer of defense is not ample, and only multi-layered security posture would give a resilient safety. 3 days immediately after the outbreak, we are summing up what we see right up until now, which is clearly a cyber pandemic that has not noticed its peak but.”
Look at Level Exploration
The market has banded alongside one another to share quick fixes and easy techniques to remediate issues in the business, but analysis has revealed attackers are getting new approaches to exploit the vulnerability.
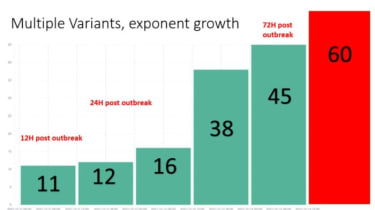
Check Level Exploration said it has found a steady raise in exploit evolutions in excess of the study course of 72 hrs because Log4Shell’s discovery, with extra than 60 distinct techniques now in use.
Results from their investigation are reported to resemble a cyber pandemic, in which attacks spread speedily and evolve continuously to crack by attempted fixes.
Check Issue Exploration
Who is most susceptible to Log4Shell?
The investigation also looked at corporate publicity to Log4Shell and concluded that a world regular of 40% of all networks throughout the earth could be susceptible to log4j flaws.
Australia and New Zealand had been identified to be the most uncovered at 46.2% of all company networks, with Europe near at the rear of with 42.2%. Asia and North The us are the minimum uncovered at 37.7% and 36.4% respectively.
Price-included resellers and the education and learning sectors ended up found to be significantly susceptible when compared to other industries, with around 50 percent of all organisations across the two sectors thought to be affected.
Compared with with the COVID-19 pandemic, the retail and hospitality sectors are imagined to be the minimum influenced, with all around a quarter of organisations exposed to log4j-primarily based attacks.
There is significant stress felt by security groups across the world to absolutely patch the vulnerability. Upgrading to the most up-to-date variation of the log4j library, version 2.15., is so far the finest mitigation against the flaw.
Also this week, the US’ Cybersecurity and Infrastructure Security Agency (CISA) instructed all federal businesses they had until 24 December to patch techniques and secure them from Log4Shell.
It follows a latest boost in emphasis on patch management across the US public sector, led by CISA, just after the company issued deadlines to all federal departments in November to patch a 300-sturdy record of significant cyber security vulnerabilities. The initially deadline passed months later but CISA declined to confirm to IT Pro if all federal businesses had satisfied the necessities in time.
Examine Stage Research explained it thinks the vulnerability in the log4j library “will keep with us for decades to appear” thanks to the complexity in patching it and the relieve in which attackers can exploit it.
Some areas of this report are sourced from:
www.itpro.co.uk


 UK’s New Cyber Strategy Designed to Boost Position as ‘Global Cyber Power’
UK’s New Cyber Strategy Designed to Boost Position as ‘Global Cyber Power’