Much more than 1.31 million consumers tried to put in destructive or undesirable web browser extensions at least once, new conclusions from cybersecurity organization Kaspersky present.
“From January 2020 to June 2022, extra than 4.3 million exceptional customers ended up attacked by adware hiding in browser extensions, which is roughly 70% of all customers afflicted by malicious and unwelcome increase-ons,” the company mentioned.
As several as 1,311,557 people fall below this class in the 1st 50 percent of 2022, for each Kaspersky’s telemetry details. In comparison, the variety of these buyers peaked in 2020 at 3,660,236, adopted by 1,823,263 exceptional buyers in 2021.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
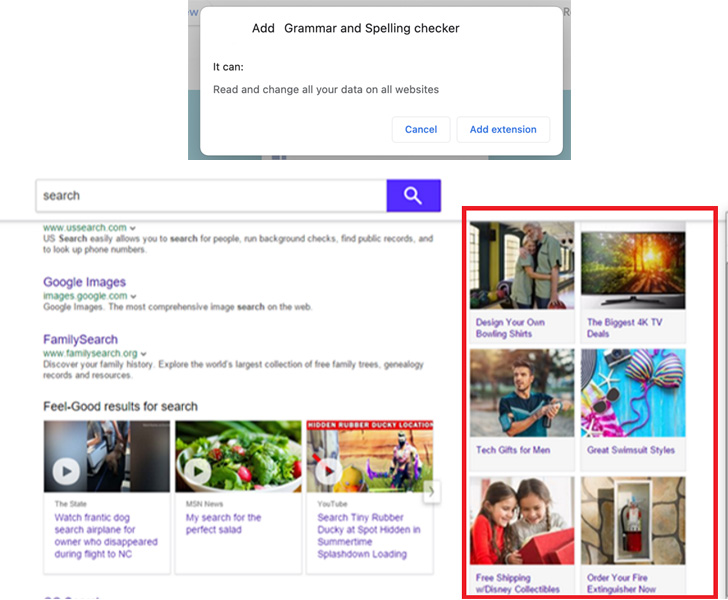
The most commonplace threat is a relatives of adware known as WebSearch, which masquerade as PDF viewers and other utilities, and comes with capabilities to obtain and evaluate lookup queries and redirect end users to affiliate one-way links.

WebSearch is also notable for modifying the browser’s start off site, which contains a lookup engine and a variety of hyperlinks to third-party sources like AliExpress that, when clicked by the victim, assist the extension developers get paid money by way of affiliate hyperlinks.
“Also, the extension modifies the browser’s default look for engine to search.myway[.]com, which can capture user queries, obtain and review them,” Kaspersky pointed out. “Dependent on what the user searched for, most relevant spouse web pages will be actively promoted in the lookup final results.”
A 2nd set of extensions entail a menace named AddScript that conceals its malicious functionality under the guise of movie downloaders. While the add-ons do offer the marketed functions, they are also created to make contact with a distant server to retrieve and execute a piece of arbitrary JavaScript code.
Around a single million end users are said to have encountered adware in H1 2022 alone, with WebSearch and AddScript focusing on 876,924 and 156,698 exceptional customers.
Also located ended up cases of data-stealing malware like FB Stealer, which intention to steal Facebook login qualifications and session cookies of logged-in end users. FB Stealer has been liable for 3,077 unique infection makes an attempt in H1 2022.
The malware generally singles out users on the lookout for cracked program on lookup engines, with FB Stealer sent by means of a trojan identified as NullMixer, which propagates by means of cracked installers for software this sort of as SolarWinds Broadband Engineers Version.

“FB Stealer is mounted by the malware relatively than by the consumer,” the researchers claimed. “The moment extra to the browser, it mimics the harmless and regular-hunting Chrome extension Google Translate.”
These attacks are also economically-determined. The malware operators, soon after getting hold of the authentication cookies, log in to the target’s Fb account and hijack it by altering the password, successfully locking out the sufferer. The attackers can then abuse the access to ask the victim’s good friends for income.
The results arrive a minor over a thirty day period following Zimperiumm disclosed a malware household identified as ABCsoup that masquerades as a Google Translate extension as aspect of an adware marketing campaign focusing on Russian users of Google Chrome, Opera, and Mozilla Firefox browsers.
To continue to keep the web browser absolutely free of infections, it is really suggested that customers adhere to reliable resources for downloading software program, evaluate extension permissions, and periodically review and uninstall incorporate-ons that “you no longer use or that you do not identify.”
Identified this write-up fascinating? Abide by THN on Facebook, Twitter and LinkedIn to examine more exclusive content material we write-up.
Some elements of this post are sourced from:
thehackernews.com


 Open source sabotage sparks fears of backlash
Open source sabotage sparks fears of backlash