Cybersecurity scientists have identified a amount of malicious deals in the NPM registry specifically targeting a amount of prominent firms based in Germany to carry out provide chain attacks.
“When compared with most malware located in the NPM repository, this payload appears especially perilous: a highly-advanced, obfuscated piece of malware that functions as a backdoor and lets the attacker to choose overall handle more than the contaminated device,” scientists from JFrog stated in a new report.
The DevOps firm explained that proof details to it currently being both the work of a advanced danger actor or a “pretty intense” penetration check.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
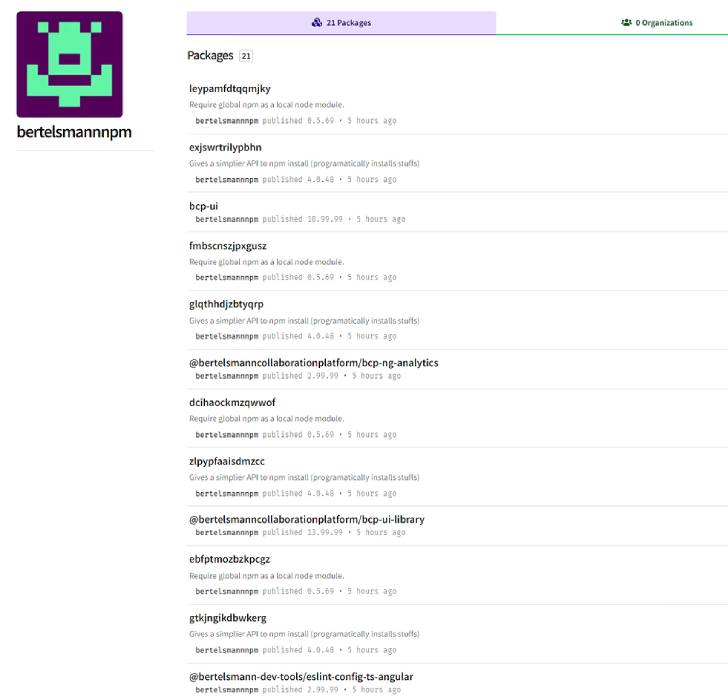
All the rogue offers, most of which have considering the fact that been taken out from the repository, have been traced to 4 “maintainers” – bertelsmannnpm, boschnodemodules, stihlnodemodules, and dbschenkernpm — indicating an attempt to impersonate legit companies like Bertelsmann, Bosch, Stihl, and DB Schenker.
Some of the deal names are mentioned to be incredibly particular, boosting the possibility that the adversary managed to recognize the libraries hosted in the companies’ inner repositories with the objective of staging a dependency confusion attack.
The conclusions develop on a report from Snyk late previous month that thorough just one of the offending offers, “gxm-reference-web-auth-server,” noting that the malware is concentrating on an unknown company that has the same deal in their personal registry.
“The attacker(s) likely experienced facts about the existence of these kinds of a offer in the firm’s private registry,” the Snyk security study staff explained.
Contacting the implant an “in-house development,” JFrog pointed out that the malware harbors two elements, a dropper that sends information and facts about the contaminated machine to a remote telemetry server ahead of decrypting and executing a JavaScript backdoor.
The backdoor, though missing a persistence mechanism, is developed to acquire and execute commands despatched from a really hard-coded command-and-regulate server, assess arbitrary JavaScript code, and upload documents again to the server.
“The attack is hugely qualified and relies on hard-to-get insider facts,” the researchers mentioned. But on the other hand, “the usernames designed in the NPM registry did not attempt to cover the focused enterprise.”
Identified this post attention-grabbing? Follow THN on Facebook, Twitter and LinkedIn to study more distinctive information we publish.
Some parts of this posting are sourced from:
thehackernews.com


 Microsoft Fixes Three Zero-Days in May Patch Tuesday
Microsoft Fixes Three Zero-Days in May Patch Tuesday